Mac Malware on the Rise – Child Porn Ransomware Demands $300 Release Fee
A piece of malware targeting Apple's computers takes over the browser and accuses users of having child porn images on their PCs and demands a fee of $300 to get back control of the computer.
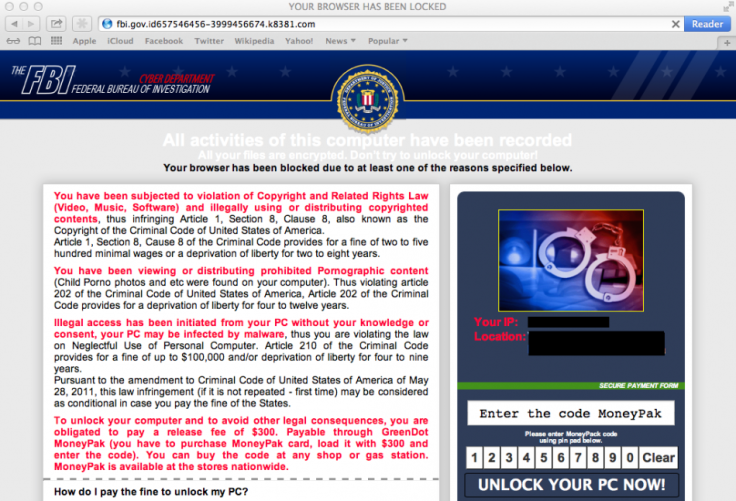
The message (seen above) claims to be from the FBI and but in reality is from cyber-criminals hoping users will simply pay the release fee in order to avoid the potential embarrassment of reporting the message to their internet provider or the authorities.
Ransomware like this has been prevalent on Windows-based PCs for many years, but with the increase in popularity of Apple's computers - in particular its range of laptops - cyber-criminals are keen to exploit this as-yet-untapped source of income.
Security firm Malwarebytes uncovered the ransomware which is affecting Apple's Safari browser.
The ransomware page is pushed onto unsuspecting users browsing regular websites, but in particular when searching for certain, popular keywords. The message which shows up claims to be from the Federal Bureau of Investigations (FBI) and reads:
"You have been viewing or distributing prohibited Pornographic content (Child porno photos and etc were found)...To unlock your computer and to avoid other legal consequences, you are obligated to pay a release fee of $300."
Pop-up message
The cyber-criminals have even gone so far as to use a URL which looks real (fbi.gov.id). If you try to simply close the page however, you will find you can't, getting the pop-up message below.
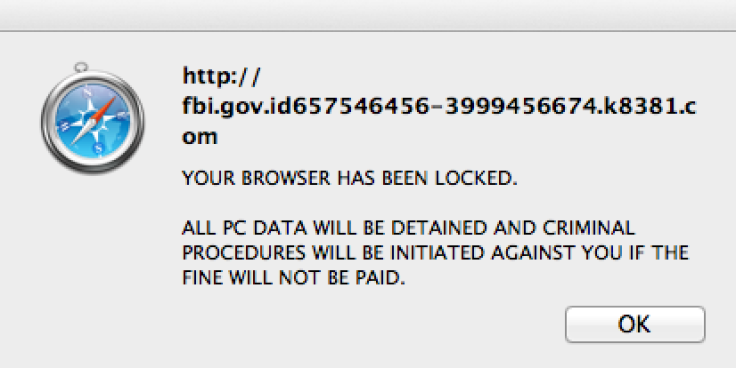
The only way to close the page is to "force quit" but the cyber-criminals take advantage of the "restore from crash" feature of the browser and when you restart Safari the message appears again.
Jerome Segura, senior security researcher at Malwarebytes said:
"The bad guys know how to use social engineering to entice victims as, for example, I was lead to this locked page by doing a search for Taylor Swift on Bing images. The victim will feel they may have actually being doing something wrong and got caught and ashamed, will pay the 'fine.'"
Segura also outlines how to get rid of the ransomware message by clicking on the Safari menu and going to the Reset Safari option. Tick all options which show up and press Reset and the webpage will disappear.
Presumption
Apple users have long been living under the presumption that they were immune from malware or computer viruses - and with good reason. Cyber-criminals are a lot of things, but stupid is not one of them (for the most part at least) and that is why for years they went after the money and targeted the much more numerous Windows PC user base.
Things seem to be changing however.
This week, as well as the child porn ransomware campaign, we have seen another new piece of Apple malware emerge - a nation-state backed Trojan which is targeting activists in Russia and Kazakhstan.
The activist-targeting Trojan known as Janicab was uncovered by Finnish security company F-Secure and is remarkable for being signed with an official Apple Developer ID indicating that it has been developed and deployed by a nation-state.
This is only the second time an Apple Developer ID has been used to sign malware targeting Mac systems, following a report in May of an Angolan activist discovering a backdoor having been installed on his Mac again using an official developer ID.
Government sponsored
F-Secure's Sean Sullivan, who posted a blog post detailing how the malware bypasses Apple's security settings, told TechWeekEurope: "As both of these cases appear to be targeted attacks against activists, it is also likely that they're government sponsored - and so faking the needed identity info may not be such a difficult task."
Then malware uses a technique known as a right-to-left override trick to fool the Mac OS X system into thinking the file being downloaded is simply a PDF, when in fact it silently downloads the malware which continuously captures audio using the computer's own microphone as well as taking screenshots and uploading them to the command and control server.
© Copyright IBTimes 2024. All rights reserved.






