Masque Attack returns: Hacking Team leveraged iOS vulnerability to install fake messaging apps

Hacking Team used a vulnerability in iOS known as Masque Attack to install fake messaging apps mimicking the likes of Facebook, WhatsApp, Skype, and others, to steal sensitive information from non-jailbroken iPhones and iPads. Revealed by security firm FireEye at the Black Hat hacker conference taking place in Las Vegas, this attack represents the "first truly advanced attack infrastructure using Masque Attack ever seen, and it is a proof point that advanced attackers are finally putting some real rigour behind smartphones, tablets, and Apple products."
The only previous use of the MasQue vulnerability in the wild was the Wirelurker attack targeting Apple users in China.
The details of this attack come from the huge 400GB data dump which was published online by a hacker who breached the security of Italian surveillance company Hacking Team. Among the data, FireEye found emails which suggests that despite the company's own claims that it could only attack jailbroken iPhones, its customers have been using this attack method for months to spy on non-jailbroken iPhones - marking it as the second time the Masque vulnerability has been seen exploited in the wild.
Just last month FireEye reported two new manifestations of the Masque Attack vulnerability called Manifest Masque and Masque Extension which it says affected almost one third of all iPhones and iPads.
As was previously revealed by security company Lookout in July, Hacking Team used a fake Newsstand app to infiltrate non-jailbroken iPhones using the Masque Attack vulnerability which takes advantage of the fact that Apple doesn't individually review enterprise apps distributed by companies and that it had given Hacking Team an enterprise certificate with which to sign its apps (now revoked).
Partially patched
The Masque Attack vulnerability, first uncovered in November 2014, allows attackers to take advantage of the fact that Apple does not enforce matching certificates for apps with the same bundle identifier. This means that a victim could click on a link claiming to be an update to a popular app - WhatsApp, Facebook, Skype, and others in this case - while in fact it downloaded a piece of malware which looks and acts like the real app.
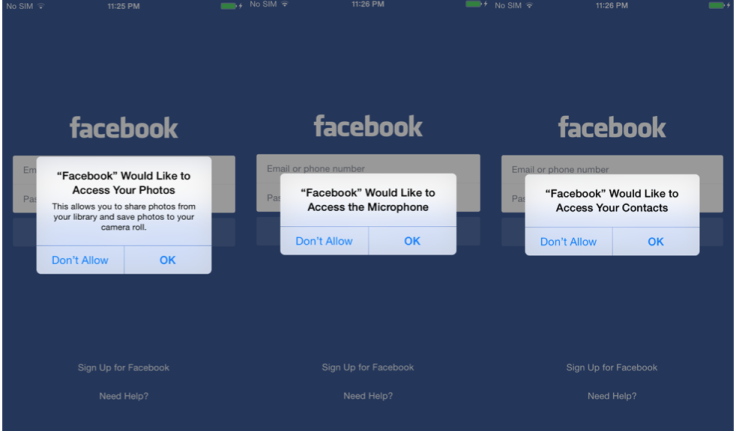
Hacking Team's fake newsstand app is really a remote control app which can be used to download any of 11 reverse-engineered and weaponised versions of these popular social networking and messaging apps:
WhatsApp, Twitter, Facebook, Facebook Messenger, WeChat, Google Chrome, Viber, Blackberry Messenger, Skype, Telegram, and VK
While Apple partially patched the Masque Attack vulnerability in iOS 8.1.3, FireEye says the attackers can still use a unique bundle identifier to deploy the weaponised app, adding: "In this scheme, the attack falls back to the Enpublic attack."
FireEye researcher Zhaofeng Chen warned: "From the attack tools leaked from the Hacking Team, we have now seen that advanced targeted attacks against iOS devices have begun to emerge. We encourage all iOS users to always update their devices to the latest version of iOS and pay close attention to the avenues that they download their apps."
While the latest revelation from Hacking Team shows that non-jailbroken iPhones and iPads can be attacked, this is not yet a major threat for the vast majority of iOS users, as this particular attack requires the attacker to have an enterprise certificate from Apple, which is not easy to come by. It would also likely require physical access to the iPhone, though the rising level of sophistication of attacks against Apple's products indicates that it is only a matter of time before a more widespread threat is detected.
© Copyright IBTimes 2024. All rights reserved.






