US Navy caught trying to buy zero-day security flaws in order to exploit popular software
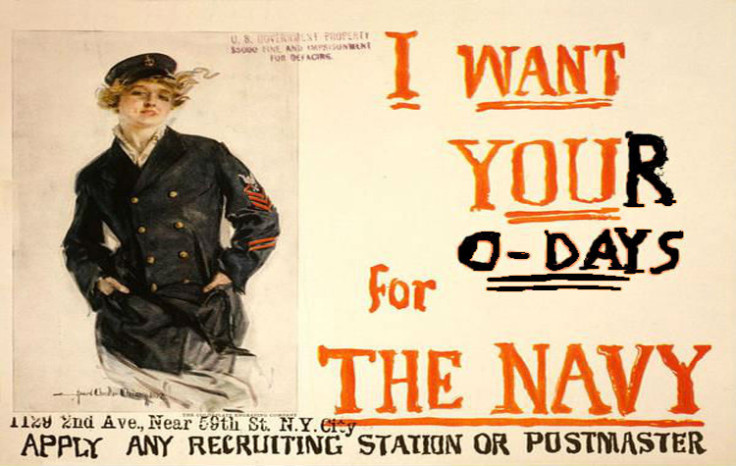
The Electronic Frontier Foundation (EFF) has spotted the US Navy publicly soliciting people to sell security vulnerabilities to well-known software, so that the US government can build backdoors into the software.
On a page posted to government agency contracting website FedBizOpps, which was deleted shortly after being highlighted by the EFF, the US Navy said the US government needs "to have access to vulnerability intelligence, exploit reports and operational exploit binaries affecting widely used and relied upon commercial software".
Specifically, the security flaws had to be either Zero-Days or N-Days, meaning flaws that were less than six months old, and therefore less likely to have been fixed.
The post, preserved by the EFF, specifically mentions the US Navy wants security vulnerabilities relating to software belonging to Microsoft, Adobe, Android, IBM, Apple, EMC, Cisco, Linksys, Linux, EMC and Java.
These large tech firms all produce software that controls everything from mobile devices, desktop publishing and secure telecommunications to computer-aided design, website programming and cloud storage.
What does the US government need security vulnerabilities for?
As part of Edward Snowden's revelations about mass surveillance in 2013, the NSA's PRISM programme bullied big tech companies such as Apple, Google, Facebook and Yahoo into giving the US government "backdoors" into their products.
The backdoor access enabled US intelligence agencies to access and harvest encrypted data about citizens, for example, reading Gmail emails or Facebook communications.
In 2012, a Forbes investigation claimed there are many companies in the world who spot security vulnerabilities but will never tell Google or any other commercial vendor because they can make lots of money by selling the hacking techniques to government agencies.
"What's more noteworthy is how little regard the government seems to have for the process of deciding to exploit vulnerabilities," the EFF writes in a post.
"As we've explained before, the decision to use a vulnerability for 'offensive' purposes rather than disclosing it to the developer is one that prioritises surveillance over the security of millions of users. To its credit, the government has acknowledged that this decision is an extraordinarily important one in every case.
"The Navy tried to send this particular solicitation down the memory hole, but we're hopeful that through our FOIA suit, we can shed more light on the conflict between the government's public statements and its apparent practices surrounding its stockpiling of zero-days."
US government says it does keep security agencies in check
The US government says it has a "disciplined, rigorous and high-level decision-making process for vulnerability disclosure" called the Vulnerabilities Equities Process (VEP) and the EFF is in the process of suing the government to find out what exactly that entails.
When the furore over the Heartbleed OpenSSL security vulnerability happened in April 2014, White House spokesperson Michael Daniel stressed the US government had no intention of leaving lots of vulnerabilities deliberately undisclosed, as doing this would put the internet and American citizens at risk.
Daniel shared a list of questions the White House insists security agencies answer if they want to withhold knowledge of a crucial security vulnerability.
He wrote in the White House blog: "Too little transparency and citizens can lose faith in their government and institutions, while exposing too much can make it impossible to collect the intelligence we need to protect the nation.
"We weigh these considerations through a deliberate process that is biased toward responsibly disclosing the vulnerability, and by sharing this list we want everyone to understand what is at stake."
© Copyright IBTimes 2024. All rights reserved.