At least 500 Android apps with 100 million total downloads found hosting malware
Google said it has now removed the malware-laced applications from its Play Store.
Google has removed more than 500 Android applications from its official Play Store after a mobile security company revealed they had been built upon suspicious advertising code which could be used to spy on victims. The apps had been downloaded more than 100 million times.
Researchers from Lookout Security Intelligence discovered that the suspicious code – from a software development kit (SDK) called "Igexin" – could be used to snoop on infected devices via downloaded malicious plugins, the firm said in a blog post this week (21 August).
Not all of the apps were confirmed to contain the spying functions. However, experts said that Igexin – a Chinese firm - could have introduced the ability at any time.
The code was so well hidden that app developers were probably never even aware of its existence.
"It is becoming increasingly common for innovative malware authors to attempt to evade detection by submitting innocuous apps to trusted app stores, then at a later time, downloading malicious code from a remote server," the Lookout blog post read.
"Igexin is somewhat unique because the app developers themselves are not creating the malicious functionality - nor are they in control or even aware of the malicious payload that may subsequently execute.
"Instead, the invasive activity initiates from an Igexin-controlled server."
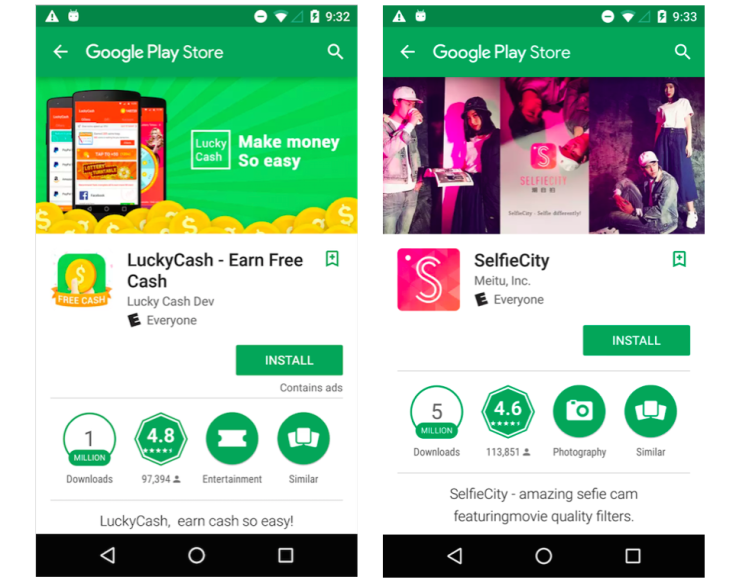
Applications containing the suspicious SDK included games targeted at teenage users (one with 50m-100m downloads), weather applications (one with 1m-5m downloads) and internet radio streaming services (one with between 500,000 and 1m downloads).
Once on a device, they could reportedly hijack call logs and GPS location data.
In an e-mail to Ars Technica, a Google spokesman said: "We've taken action on these apps in Play, and automatically secured previously downloaded versions of them as well. We appreciate contributions from the research community that help keep Android safe."
Advertising SDKs are used to help developers deliver targeted ads to customers.
Lgexin was known to promote "targeted advertising services that leverage data collected about people such as their interests, occupation, income, and location".
But a quick Google search shows security firms have labelled Igexin as a "potentially unwanted application" since at least 2015.
One advisory from Symantec said that it had been known to "send details about installed applications to a remote location".
Lookout started its analysis after being made aware of suspicious traffic from the applications.
But its analysis stressed that the developers – in this instance – should not be blamed. In the majority of cases they set the app permissions, but here it wouldn't have mattered.
"It is likely many app developers were not aware of the personal information that could be exfiltrated from their customers' devices as a result of embedding Igexin's ad SDK," wrote Lookout researchers Adam Bauer and Christoph Hebeisen in the blog.
"It required deep analysis of the apps' and ad SDK's behaviour [...] to make this discovery," they added. "Not only is the functionality not immediately obvious, it could be altered at any time."
Google, which owns the Android OS, tries hard to keep its own marketplace free from malware-laced applications, but many still slip through the cracks.
© Copyright IBTimes 2024. All rights reserved.