'Anonymous is a Brand Like al-Qaida' - An Interview with Mikko Hypponen
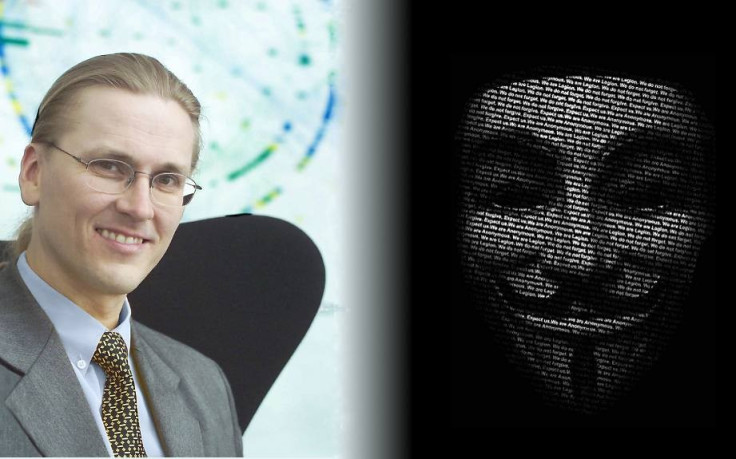
In an exclusive interview with International Business Times UK, top security expert Mikko Hypponen of F-Secure talked about Anonymous, hacktivism and the challenges of cyber-security.
Mikko Hyppönen is currently the Chief Research Officer for Finnish online security company F-Secure. He has a track record of assisting law enforcement across the world deal with cyber-criminality and has advised several governments on cyber-policy.
Today, many security companies say that no matter how good your security is, if a hacker is persistent enough they will find a way to break in. Is this the case, especially with groups like Anonymous where the end goal isn't necessarily financial gain?
We go to great lengths to make it [products and networks] unhackable, no guarantees. If we could provide you with 100 percent security we would, we can't, we never will, but neither can anyone else. Think of it in terms of, lets say a locksmith.
You can get the best locksmith in the world to design the best lock he can design, is it pick proof? No, it's not, it can be very hard to pick, but it is pickable. Because you can get, say, the next 10 best locksmiths and give them unlimited money and time, they will figure out a way to pick it. If they have the motivation and the funding, it can be done. Exactly the same thing applies to everything else. It's a trade off between how committed the attacker is and how well you're secured.
A good example, you mentioned Anonymous. So, Sony, which was hacked 37 times last year, mostly because of what they did with George Hotz, suing him [for] modifying his own PlayStation - which was a bad idea by Sony - I mean compared to what Apple did with Comex. Exactly the same thing, George Hotz hacked his own PlayStation, Sony sued him. Comex hacked his iPhone, Apple hired him - good move - Apple wasn't hacked 37 times.
But it's sort of easy to see why Sony could be hacked. Sony has 168,000 employees in 180 countries and dozens of data centres across the world, a massive infrastructure. So if a hacker goes looking for a hole, he's going to find a hole, it's just so massive a system.

For example, one of the ways Sony was hacked, I think hack five or six, happened through Sony Thailand. Sony Thailand had web servers set up in 2009 that they had forgot about, but the website was still up and running without ISS updates. So the attackers got on through into Sony Thailand's network and from there they gained access to Sony Tokyo and so on. And so you can see how, no matter how hard you work, there will be a way in if you have a massive infrastructure, which Sony does.
However, lets take another example, HBGary Federal. They have 30 employees, one location, one data centre, every single employee is a world class security expert - I know many of the guys and they're really, really good - and they were hacked. So, if they can be hacked anybody can be hacked. If it happens to a company like that, it can pretty much happen to anyone - there are no secure systems. How many of the fortune 500 are hacked? 500.

If all of these companies are insecure, would you say this phenomenon is systematic of a problem that's not going to go away in security? Not just because of cyber criminals, but because of "hacktivists" whose political motivation gives them a dog-and-bone like mentality towards their target?
Actually those are the first two of the three enemies threatening us today. I spend quite a bit of time doing what we call "threat analysis," trying to see the motives behind the attackers. So we go through the motives and define the attacker based on their motivation. Right now I put them into three groups - in the near future possibly four groups, I'm speaking here about extremists and terrorists using online resources and how I believe it's likely they're going to become the fourth group. Though, right now it's still three: criminals, hacktivists and third, governments.
By governments you're referring to the slew of allegations going China's way?
And the UK, everyone. There's a whole range there starting from espionage to cyber sabotage, in the future cyber war, to attacks on their own citizens - which happens in Syria and Iran thanks to technology provided by the UK to Syria to track down dissidents and kill them.
Going back to criminals, it's very easy to understand them. They want money and that's it, there's no other motive or logic. If they can't make money, they move on to something else and there, when defending yourself, you just want to be a little better guarded than the other guy. For example, online banks, they know they can't be 100 percent safe, so they just try and have a bit higher security than the competing banks so the attackers will go after the other banks first. Money is the easiest motive to understand.
Hacktivists, Anonymous, LulzSec they don't want money. Their motive is different; political, "lulz," something along those lines. These guys, their motives can be anything other than money. The governments, the biggest part of these attacks are espionage, most of which are credited to China - most of them probably accurately.
With this and the recently-leaked FBI conference call, discussing how young some "hacktivists" are in mind, how do you see the security industry developing and dealing with these constant threats?
Is that really a problem for security? I think it's a much bigger problem, this is the next generation, the generation growing up that's unaware there was a time before the internet. To them the internet is as natural as breathing air, they don't remember a time before Google, they don't remember a time before Wikipedia. They think about protests in a different way than we do. They don't see any difference between going outside the headquarters of a company and sitting-in and bringing down its website. To them it's exactly the same thing, of course, one of them is a crime and they don't seem to care.
I've thought about this and I think it's a long term problem and I think, in a way, it's a problem that will solve itself. What I mean by that is, we are the dinosaurs, we just don't get it. But it's ok because we're going to grow old and we're going to die out. But the next generation, these guys, they're going to grow up and they're going to pass their own rules. Maybe one day they will change the law and distributed denial of service (DDoS) attacks will be a form of legal protest.
This is just like a problem you would have in the real world, if you go out and hang out with the wrong kind of crowd you end up in trouble. This is exactly what happens online, you end up in the wrong forums, the wrong chats and get interested in the "dark side." I suppose it is tempting.

Interesting, but do you think this will solve the more serious attacks that see Anons actually hack, not DDoS, companies' networks and sites for political reasons?
I believe, for example with the Stratfor hack, that they weren't really going after Stratfor. I think they just happened to get in and found a justification for the hack. Though, as seen by their release, there are some skeletons in Stratfor's closet, which I guess proves that almost every company has skeletons. I think they just got lucky and found a way to justify why.
Do you think that's true of all Anonymous's campaigns, taking for example their activity in Iran and Turkey?
What you stumbled on there is something different. It's quite interesting, Anonymous is like an amoeba, it's got too many different operations run by truly different people which might not share a single person with another operation, but they use the same branding - they are part of the Anonymous brand, just like al-Qaida. Its just a brand nowadays, nothing else It's run the same, so that, like al-Qaida, anyone can credit an attack to Anonymous and no-one's there to say otherwise. Like they say themselves; "we all are Anonymous".
© Copyright IBTimes 2025. All rights reserved.





















