Is Russia Preparing for the Cyber Cold War?
Russia's defence ministry has established a centre for advanced research which could herald the dawn of a global cyber cold war.

In the last month, the security industry has being getting to grips with the highly-complex cyber espionage tool known as Flame. While the computer virus is not a danger to you or me, it does pose a serious threat to governments and highlights that leaders around the world are now embarking on high-level, cyber-attacks against other nation states.
Therefore, it will be of great interest to a number of governments that Russia has announced the establishment of the Russian Foundation for Advanced Research Projects in the Defense Industry which will "take on all high-risk and fundamental research projects" according to deputy prime minister Dmitry Rogozin.
As well as telling the Russian government the best way to ensure the country's superiority in defence technology, it will also highlight areas where the country may be vulnerable - with cyber espionage likely to be top of its list.
While Vladimir Putin or any of his govermnet colleagues have not openly said that cyber espionage tools or cyber weapons will be developed at the centre, it would seem like a huge oversight if Russia was not developing weapons similar to Stuxnet and Flame.
With the cost of Stuxnet rumoured to be about $10 million (£6.4m), the same as the cost of dropping a single bomb on Iraq, the economics of cyber-attacks make a lot of sense.
So a Cyber Cold War could be on the cards, but will the Russians be once again staring down the Americans on the other side of the divide?
Stuxnet and Flame
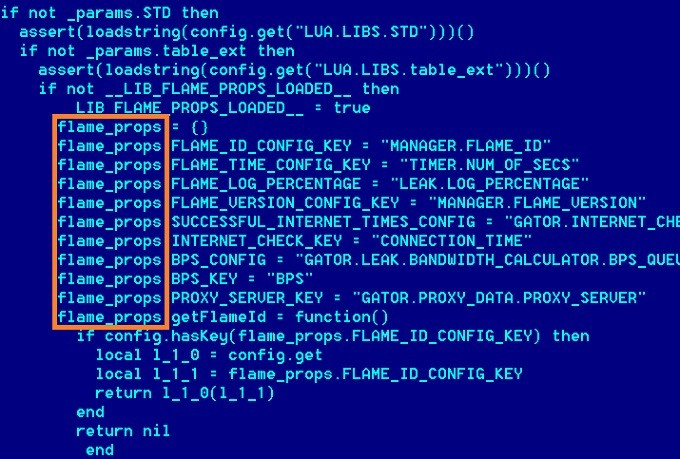
While no government or group has taken responsibility for the development of Flame, all evidence points to it being developed by the same people behind the Stuxnet cyber weapon, which sought to damage 1,000 centrifuges at the Natanz nuclear facility in Iran from 2009.
In his book Confront and Conceal, New York Times journalist David Sanger says Stuxnet, and by association Flame, was developed by the US government, initially under George W. Bush and carried on by current US president, Barack Obama.
Sanger quotes current and former American, European and Israeli officials involved in the program.
However, security experts believe that the US is playing a dangerous game by carrying out such attacks which will leave it vulnerable as an obvious target for attacks from outside.
Considering that the US is one of the countries most reliant on networked computer systems in the world, it has more to lose than many other countries.
While Stuxnet and Flame were both developed to target computer systems in Iran, it would be naïve to assume that Iran is the only country that the US is seeking to attack though the use of malware.
Two of the world's foremost security experts, Kaspersky Lab founder, Eugene Kaspersky and F-Secure security chief Mikko Hypponen have both told us that they believe most if not all governments are involved in cyber espionage to a greater or lesser degree.
Cyber War
Hypponen believes this type of espionage has been going on for 10 years or more, but beleives we are yet to see a cyber war: "I don't think we have seen cyber war yet. How can you have a cyber war without a real war? What are we then going to call it when there is a real war?"

Indeed some governments are very up-front about it, with both German and Denmark governments admitting they were establishing cyber espionage divisions.
To see just how seriously the US is taking its cyber espionage program, all you need do is look at the jobs listings on the National Securtiy Agency (NSA) website.
According to the Cyber Careers section of the website, the NSA's remit is to "gather foreign intelligence and to defend US government information systems."
One of the 'Hot Jobs' on the computer science section is in the Cryptanalytic Computer Network Operations Development Program.
Duties would include solving "challenging cryptanalytic problems of critical importance to protecting the Nation's interests in cyberspace." While this may mean little to you or me, cutting-edge cryptography like mentioned in the description was used in the development of the Flame virus.
With the US clearly looking to position itself for a Cyber Cold War, one question which remains to be answered is if Russia has the resources to launch sophisticated attacks on the computer networks of the US government agencies.
Russian Cybercriminals
In order to develop Flame and before that Stuxnet, the US government and its partner-in-crime, Israel, had to recruit some of the top minds in the field of computer science, mathematics and cryptography.
When mathematics behind Flame was analysed, it stunned some academics, with those who created it developing never-before-seen solutions to complex mathematical problems.
However, Russia is no slouch when it comes to cyber experts itself, as it is widely thought to house the largest proportion of cyber criminals in the world.
In an article in Forbes last April, it was estimated that Russians accounted for more than a third of the global cyber crime market, estimated at $12.5bn.
The hacking skills of malware gangs like Koobface had made them millionaires and Russian computer geniuses are held in high esteem within the global hacking community.
It is clear therefore that the knowledge base and required skills are there, and it may only be a matter of incentivising these hackers to work for the government instead of themselves before we see Russia emerge as the next cyber espionage force.
While the physical Cold War threat of nuclear weapons was always a constant reminder to those living in the US and USSR that annihilation was only the a button press away, the same cannot be said for the Cyber Cold War.
Flame went undetected by the world's security firms for more than two years, despite being one of the most complex computer virus ever discovered.
This means that Russia and the US may have already embarked on a cyber war without either side having knowledge of what the other is up to, while citizens of both countries live in complete ignorance of how their governments may be putting their lives at risk.
© Copyright IBTimes 2025. All rights reserved.





















