Flame and Stuxnet Creators Co-Operated on Viruses
In-depth research reveals that the creators of the highly complex Flame virus co-operated with the team behind the Stuxnet virus at some point.
The Flame malware was discovered a little over two weeks ago, and at the time the highly complex cyber-weapon was thought to have been developed completely independently from Stuxnet and Duqu, the most high profile cyber-weapons to be discovered previously.
"At the time of its discovery, there was no strong evidence of Flame being developed by the same team that delivered Stuxnet and Duqu. The development approach of Flame and Duqu/Stuxnet was different as well, which lead to the conclusion that these projects were created by separate teams," a statement from Kaspersky Labs said.
However, following in-depth research conducted by Kaspersky Lab experts, who helped to identify the malware initially, it has been revealed these teams in fact co-operated at least once during the early stages of development.
"They [Flame and Stuxnet] each have different architectures with their own unique tricks that were used to infect systems and execute primary tasks. The projects were indeed separate and independent from each other. However, the new findings that reveal how the teams shared source code of at least one module in the early stages of development prove that the groups cooperated at least once. What we have found is very strong evidence that Stuxnet/Duqu and Flame cyber-weapons are connected," said Alexander Gostev, Chief Security Exper at Kaspersky Lab
Stuxnet was the first known cyber-weapon to target industrial facilities. The fact that Stuxnet also 'accidently' infected regular PCs worldwide led to its discovery in June 2010, although the earliest known version of the malicious program was created one year before that.
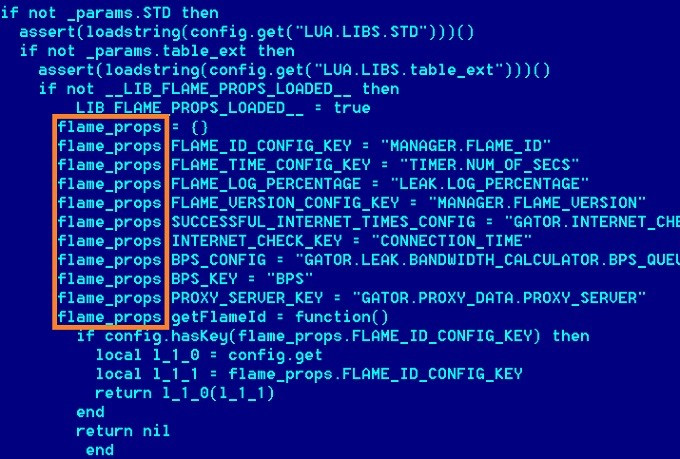
Resource 207
It was this June 2009 version which contains a special module known as "Resource 207". In the subsequent 2010 version of Stuxnet this module was completely removed. The "Resource 207" module is an encrypted DLL file and it contains an executable file that's the size of 351,768 bytes with the name "atmpsvcn.ocx".
This particular file, as it is now revealed by Kaspersky Lab's investigation, has a lot in common with the code used in Flame. "The list of striking resemblances includes the names of mutually exclusive objects, the algorithm used to decrypt strings, and the similar approaches to file naming," Kaspersky said in a statement.
Vitaly Kamluk, the firm's chief malware expert, said: "There is a link proven - it's not just copycats. We think that these teams are different, two different teams working with each other, helping each other at different stages."
Last week it was revealed by a New York Times journalist David Sanger, in an extract from an up-coming book, that Stuxnet was part of a US and Israeli intelligence operation codenamed "Olympic Games", started under President George W. Bush and expanded under President Barack Obama, and aimed at spying on Iran's nuclear program.
The FBI has now launched an investigation looking into who might be behind the leaks, according to the Wall Street Journal.
No country has officially taken responsibility for the Stuxnet attack, and speaking about Flame to the BBC, a spokesman for the Israeli government distanced the country from involvement following an interview in which a minister seemed to back the attacks.
"There was no part of the interview where the minister has said anything to imply that Israel was responsible for the virus," the spokesman said.
While the discovery of a link between Stuxnet and Flame is interesting, it does not help identify who is behind the malware, according to Professor Alan Woodward, a security expert from the University of Surry, who told the BBC:
"The fact that they shared source code further suggests that it wasn't just someone copying or reusing one bit of Stuxnet or Flame that they had found in the wild, but rather those that wrote the code passed it over," he said.
"However, everything else still indicates that Flame and Stuxnet were written designed and built by a completely separate group of developers. At the very least it suggests there are two groups capable of building this type of code but they are somehow collaborating, albeit only in a minor way."
© Copyright IBTimes 2025. All rights reserved.






















