GCHQ's Online Spying Tricks: Rigged Polls, Facebook Propaganda, Skype, LinkedIn Info Capture

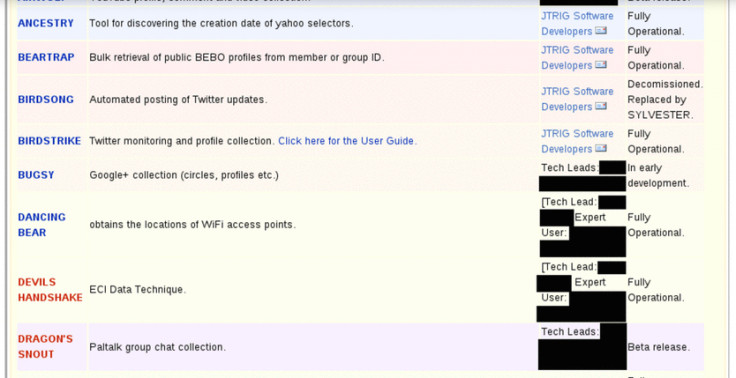
A comprehensive document that lists all the tools and spying techniques used by GCHQ to plant fake information on the internet in order to spy on people and push propaganda has been released by The Intercept, a platform for publishing documents leaked by NSA whistleblower Edward Snowden.
The Joint Threat Research Intelligence Group (JTRIG) was responsible for developing most of the software programs listed in the documents, which enable GCHQ personnel to make fake victim blog posts, manipulate online polls, send fake SMS text messages, promote a specific video message on YouTube, carry out Denial of Service (DDOS) attacks against websites, and even post fake Facebook posts to entire countries.
Of course, the software programs also include tools enabling the government to spy on and capture information on people from fax machines, smartphones and computers.
To that end, there is malware able to silently copy and forward emails to a GCHQ server, grab IP addresses of Skype (and previously, MSN messenger) users, hunt for users on the TOR anonymity network, find private photographs on Facebook, and locate private Wi-Fi access points.
The Intercept is a website run by a group of journalists who have been given access to documents relating to the NSA and government intelligence gathering, and their reports come from primary sources from the documents.
The Intercept is able to stay editorially independent and can release documents as and when it sees fit, such as now, when MPs are debating the emergency Data Retention and Investigatory Powers Bill (DRIP) in the House of Commons that David Cameron wants to be rushed through.
"Serious questions have been raised about whether top national security officials even know what GCHQ is doing," writes Glenn Greenwald.
"Chris Huhne, a former cabinet minister and member of the national security council until 2012, insisted that ministers were in "utter ignorance" about even the largest GCHQ spying program, known as Tempora—not to mention "their extraordinary capability to hoover up and store personal emails, voice contact, social networking activity and even internet searches."
Here is a list of some of the most intrusive programs we've noticed on the list:
HACIENDA – A port-scanning tool designed to scan an entire country or city, using GEOFUSION to identify IP locations. Banners and content are pulled back on certain ports. Content is put into the EARTHLING database, and all other scanned data is sent to GNE and is available through GLOBAL SURGE and Fleximart.
AIRWOLF – Collect Youtube profile, comment and video collection.
SYLVESTER – Framework for automated interaction/ alias management on online social networks
FATYAK – Public data collection from LinkedIn.
GESTATOR – Amplification of a given message, normally video, on popular multimedia websites (YouTube).
TRACER FIRE – An Office document that grabs the target's machine info, files, logs etc and posts it back to the GCHQ.
BOMB DAY – The capability to increase website hits/rankings.
CHINESE FIRECRACKER – Overt brute login attempts against online forums.
SILVER SPECTOR – Allows batch Nmap scanning over TOR.
ANGRY PIRATE –A tool that will permanently disable a target's account on their computer.
CLEAN SWEEP –Masquerade Facebook wall posts for individuals or entire countries.
ROLLING THUNDER –Distributed denial of service using P2P. Built by ICTR, deployed by JTRIG.
SCRAPHEAP CHALLENGE – Perfect spoofing of emails from Blackberry targets.
PREDATORS FACE – Targeted Denial of Service against Web Servers.
VIPERS TONGUE –A tool that will silently put Denial of Service calls on a satellite phone or GSM phone.
GLITTER BALL – Online gaming capabilities for sensitive operations. Currently Second Life.
SODAWATER – A tool for regularly downloading Gmail messages and forwarding them onto CERBERUS mailboxes.
SILVER LORD – Disruption of video-based websites hosting extremist content through concerted target discovery and content removal.
© Copyright IBTimes 2025. All rights reserved.






















