Google Android: Smartphones hit with Mazar Bot malware that can 'erase everything'

Android users are being warned about a new strain of malware called Mazar Bot that is hitting smartphones, giving attackers full administrative rights to monitor and control nearly every aspect of the phone.
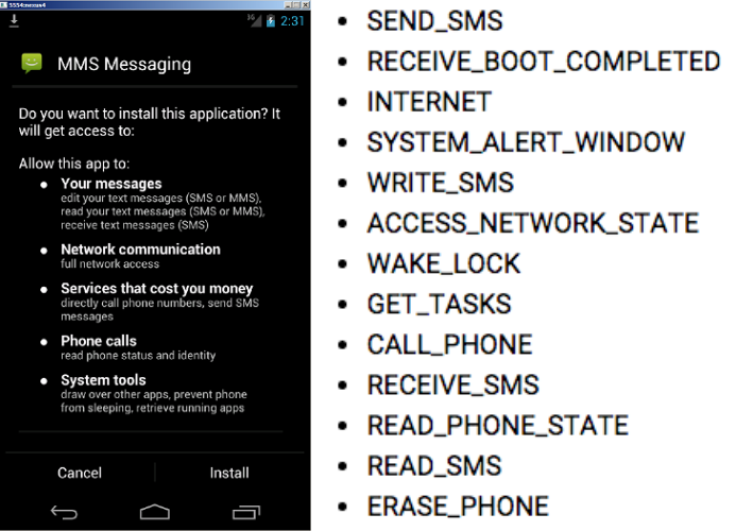
The manipulative and persistent piece of malware, found to be in active use by researchers at Heimdal Security, takes hold via a malware-ridden SMS/MMS message that, once clicked, spreads a torrent of alarming exploits such as sending malicious text messages, anonymously accessing the web, putting the phone into sleep mode and even fully erasing all content from the device.
Unlike the typical Android exploit, Mazar Bot targets users with a direct message and is not downloaded through a third-party application store. Until now, the malware was advertised as being for sale on the dark web however this is the first known case of it being exploited in active attacks.
Once on a device, the malware covertly downloads Tor that allows it to connect anonymously to the internet to ping a server that effectively acts like a beacon to alert the attacker that a fresh device has been compromised. What's worse, it can install the Android-based Polipo Proxy application which lets the owner of the malware intercept and spy on all internet traffic passing through the smartphone.
According to Andra Zaharia, security specialist at Heimdal Security, this could lead to Man-in-the-Middle (MITM) attacks which are often used to steal sensitive details such as email account logins, social media credentials and banking information.
Who is behind Mazar Bot?
While it's not 100% certain, security experts claim that evidence suggests the attackers operating the malware are Russian. When Mazar Bot was first discovered last year by researchers from Recorded Security, it was revealed the malware was being advertised on a Russian-language dark web-hosted website.
Additionally, the malware is coded not to work on Russian handsets. "Our team was not surprised to observe that the malware cannot be installed on smartphones running Android with the Russian language option," said Zaharia. "Mazar Bot will check the phone to identify the victim's country and this will stop the malicious APK if the targeted phone turns out to be owned by a Russian user."
And unfortunately, according to Heimdal Security, the malware is only likely to evolve in the coming months. "Attackers may be testing this new type of Android malware to see how they can improve their tactics and reach their final goals, which probably is making more money," added Zaharia. "We can expect this malware to expand its reach."
The Android mobile operating system has faced a number of major security concerns over the past 12 months, including the notorious Stagefright malware which at the time was said to have impacted up to 95% of all Android devices.
© Copyright IBTimes 2024. All rights reserved.






