Hacking at Sony has similarities with earlier attacks in Middle East and South Korea
The recent hacking attack at Sony Pictures has "striking similarities" with those that happened earlier in the Middle East and South Korea, according to security experts.
Russia-based anti-virus software maker Kaspersky Lab said the three hacking campaigns might have been conducted or organised by the same group.
Kaspersky researcher Kurt Baumgartner told Reuters there are "unusually striking similarities", and "it could be a single actor or it could be that there are trainers or individuals who float across groups."
Last week, the computer systems of Sony Corp's film and TV studio unit were hacked, and at least five new movies are now being shared online illegally. The malware involved in the Sony Entertainment attack is called Trojan Destover and is capable of wiping disk drives.
Sony Pictures was looking into whether the hacking was done by cyber warriors in North Korea. The studio is reportedly releasing a movie called The Interview about a CIA plot to kill North Korean leader Kim Jong-Un.
In 2012, Saudi Arabia's national oil company and Qatar's RasGas were hit by a virus known as Shamoon that damaged tens of thousands of computers. In 2013, more than 30,000 PCs at South Korean banks and broadcasting companies were hit by a similar attack by a virus dubbed DarkSeoul malware.

In an in-depth tech blog, Baumgartner said the Destover has implications for data recovery, similar to DarkSeoul and Shamoon. In addition, they have similarities in functions, resources used and execution style.
"In all three cases: Shamoon, DarkSeoul and Destover, the groups claiming credit for their destructive impact across entire large networks had no history or real identity of their own," Baumgartner said.
"All attempted to disappear following their act, did not make clear statements but did make bizarre and roundabout accusations of criminal conduct, and instigated their destructive acts immediately after a politically-charged event that was suggested as having been at the heart of the matter."
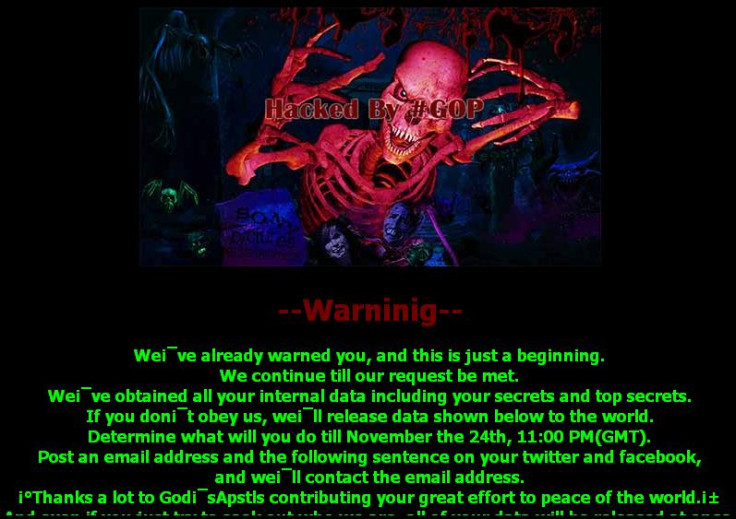
There are also similarities in the images used by hackers after the attack.
Samples of Destover malware contained configuration files created on systems using Korean language packs, he added, suggesting the North Korean link to the attack. However, he noted it is unclear if the hackers work directly for the government.
Kaspersky's rival, California-based Symantec, denied the findings, saying the similarities are due to copying.
"There is no evidence to suggest that the same group is behind both attacks," Symantec said on its blog.
© Copyright IBTimes 2025. All rights reserved.





















