iOS 6 Untethered Jailbreak: New iOS 6.1.3 Update Will Kill Evasi0n Jailbreak, Says Planetbeing
David Wang (aka planetbeing) has revealed in a recent report on Forbes that the newly released iOS 6.1.3 beta 2 update from Apple fixes a key vulnerability used in the evasi0n jailbreak. The report further suggests that Apple has indeed patched one of the five key exploits used in evasi0n, which could eventually kill the jailbreak and render it useless.
As iDownloadBlog notes, discussing the future of evasi0n jailbreak with Forbes' writer Andy Greenberg, planetbeing had this to say:
"If one of the vulnerabilities doesn't work, evasi0n doesn't work. We could replace that part with a different vulnerability, but [Apple] will probably fix most if not all of the bugs we've used when 6.1.3 comes out."
Unlike in the past, Apple seems to have fixed its software vulnerabilities in a relatively quicker time with the iOS 6.1.3 update. Contrary to expectations of the jailbreak community, Apple seems to have succeeded in plugging the vulnerabilities used by the evad3rs dev team in evasi0n jailbreak tool within weeks of its release.
According to analysts, the popularity of the evasi0n jailbreak tool (downloaded across seven million devices in just four days) and security concerns raised by iOS researchers may have forced Apple to fix the vulnerabilities.
Here is what Andy Greenberg writes in his recent Forbes report, citing the concerns raised by iOS security researchers:
"Security researchers have nonetheless pointed out that Evasi0n could give criminals or spies some nasty ideas. The tool uses five distinct bugs in iOS, all of which might be appropriated and combined with other techniques for malicious ends. And F-Secure researcher Mikko Hypponen points out that if a hacker used a Mac or Windows exploit to compromise a user's PC, he or she could simply wait for the target to plug in an iPhone or iPad and use evasi0n to take over that device as well.
More likely, perhaps, is a scenario described by German iPhone security researcher Stefan Esser. He argues that a hacker could use a secret exploit to gain access to an iPhone or iPad and then install evasi0n, using the jailbreaking tool to hide his or her tracks and keep the secret exploit technique undiscovered by Apple and unpatched. "That way they protect their investment and leave no exploit code that could be analyzed for origin," Esser wrote on Twitter.
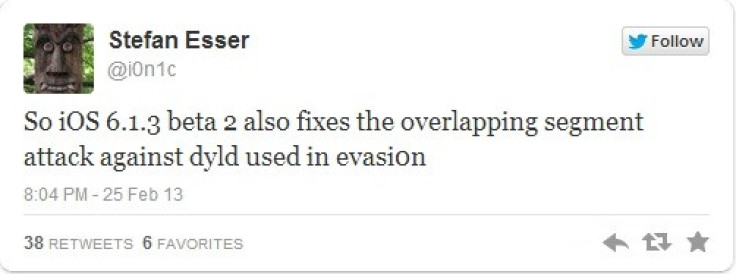
As iPhone Hacks notes, there is more bad news for the jailbreak community: renowned iOS security researcher and hacker Stefan Esser (aka i0n1c) recently tweeted that besides the timezone vulnerability, Apple has fixed yet another vulnerability for overlapping segment attack against dyld used in evasi0n.
Although it is too early to predict the extent of damage that the iOS 6.1.3 update could do to your jailbroken device, jailbreakers are strictly advised to avoid updating their device to iOS 6.1.3 until further notice from the evad3rs Dream Team. On the brighter side (for non-jailbreakers), iOS 6.1.3 reportedly brings major enhancements to Maps app for Japan and a fix for the passcode security bug.
© Copyright IBTimes 2024. All rights reserved.






