Malware 'Unflod Baby Panda' Hits Jailbroken iOS Devices, Steals Apple ID and Passwords

A new security issue pertaining to malware infected jailbroken iOS devices has recently been discovered by jailbreakers on reddit and later reported by renowned security researcher, Stefan Essar aka i0n1c.
According to iPhone Hacks, a malware known as "Unflod Baby Panda" has reportedly infected certain jailbroken iOS devices with software installed via Chinese pirate repositories.
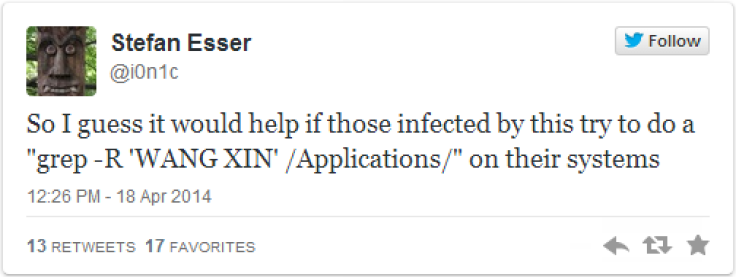
The malware is reportedly suspected to be signed with an iPhone developer certificate and registered to a person named WANG XIN. It is not yet known if this is a real person or fake or a victim of stolen certificate.
Here is what the folks at security firm SektionEins reported about the malware:
This malware appears to have Chinese origin and comes as a library called Unflod.dylib that hooks into all running processes of jailbroken iDevices and listens to outgoing SSL connections.
From these connections it tries to steal the device's Apple-ID and corresponding password and sends them in plaintext to servers with IP addresses in control of US hosting companies for apparently Chinese customers.
How to Detect Malware Infection
Those suspecting a malware infection on their iPhones or iPads can confirm the same as follows:
- Navigate to /Library/MobileSubstrate/DynamicLibraries/ and check if the "Unflod.dylib" file exists within this folder. If yes, then it confirms that your device is infected with malware, else your device is free from the malware infection.
- Alternatively, run a grep command on your iOS device to verify if there is a malware infection, as suggested by Stefan Esser in a recent Twitter update.
i0n1c also reports that the malware 'Unflod.dylib' was first recognised by Dr. Web via Virustotal with a Detection ratio of 1/50 (one out of 50 instances).
How to Remove 'Unflod Baby Panda' Malware Infection on iPhone or iPad
- First locate the malware files: Unflod.dylib and Unflod.plist using iFile and then delete them manually using a file shredder tool such as iShredder (to delete files permanently).
- Change the Apple ID password and enable two-step verification.
- If you are unsure about any other secondary infections due to the malware, then perform a full restore to remove all existing threats from your device.
Note: A full system restore will eventually delete all jailbreak apps and tweaks installed on the device. So, ensure that you have a backup of user data and necessary jailbreak installation files before you proceed.
© Copyright IBTimes 2024. All rights reserved.