Windows zero-day flaw that impacts 'every version' being sold on Russian forum for $90,000
Cyber sleuths at security firm Trustwave have uncovered chatter on a Russian underground malware forum discussing a zero-day vulnerability in "every version" of Windows that is being openly sold for $90,000 (£62,000).
The Local Privilege Escalation (LPE) flaw reportedly exists in all versions of Microsoft Windows OS starting from Windows 2000 and, if recent claims from Microsoft officials are to be believed, could leave its allegedly 1.5 billion-strong global userbase at risk of attack.
According to analysis released by researchers with SpiderLabs, a team of penetration testers and ethical hackers at Trustwave, the security flaw being sold allows attackers to upgrade any Windows user level account to an administrator account, giving them access to install malicious software, gain access to other machines and change user settings.
In hacking circles, zero-day vulnerabilities are much sought-after pieces of code previously unknown to anyone that can be exploited to infiltrate or attack a computer system without warning. Previously, a number of these bugs were uncovered in Adobe Flash software after the now-infamous breach at Hacking Team.
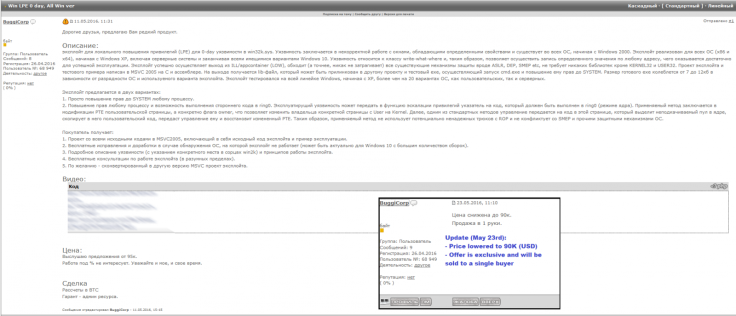
The forum post was initially made on 11 May on an underground hacking forum that, according to SpiderLabs, is frequently used to hire malware coders, buy exploit kids or even rent entire botnets. However, failing to shift the flaw on the first go, the vendor updated the post on 23 May reducing the price by $5,000 and providing two videos showing the bug in action – even working on an up-to-date build of Windows 10 (as shown above).
Translated into English, the forum post states: "Dear friends, I offer you a rare product. Exploit for local privilege escalation (LPE) for a 0day vulnerability in win32k.sys. The vulnerability exists in the incorrect handling of window objects, which have certain properties, and [the vulnerability] exists in all OS [versions], starting from Windows 2000.
"[The] exploit is implemented for all OS architectures (x86 and x64), starting from Windows XP, including Windows Server versions, and up to current variants of Windows 10 [...] the exploit was tested on all versions of Windows, starting from XP, and on at least 20 different variants of Windows OS, including Windows Server versions."
Microsoft has been notified about the potential zero-day being traded online. In a comment to IBTimes UK, it said: "Windows is the only platform with a customer commitment to investigate reported security issues, and proactively update impacted devices as soon as possible. We recommend customers use Windows 10 and the Microsoft Edge browser for the best protection. Our standard policy is to provide solutions via our current Update Tuesday schedule."
Meanwhile, the SpiderLabs researchers said it's important to note that despite indications the sellers' offer is legitimate, there is no real way to check its legitimacy without "taking the risk of purchasing the exploit or waiting for it to appear in the wild."
While it's also noted that Remote Code Execution (RCE) exploits are clearly the most desired form of hacking tool, these so-called Local Privilege Escalation vulnerabilities are a close second.
"Zero days have long been sold in the shadows," the SpiderLabs analysis said. "Finding a zero day listed in between these fairly common offerings is definitely an anomaly. It goes to show that zero days are coming out of the shadows and are fast becoming a commodity for the masses, a worrying trend indeed."
[UPDATE] This story was updated on 2 June to relect how the SpiderLabs team works with Trustwave and to insert a fresh comment from Microsoft.
© Copyright IBTimes 2025. All rights reserved.





















