Ashley Madison hack list: How you can search if your credit card details are at risk from fraudsters
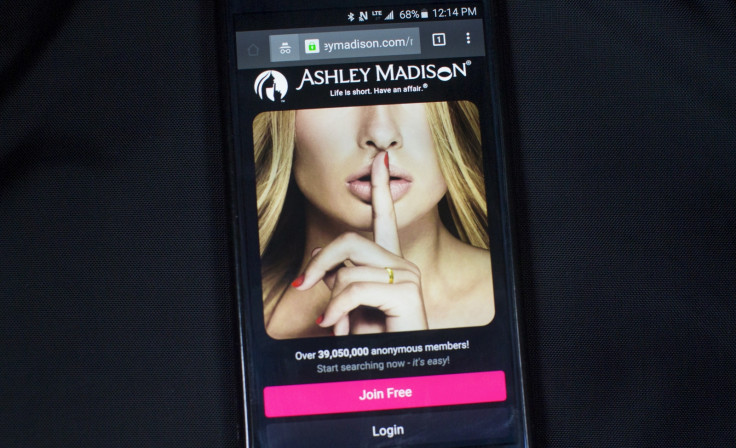
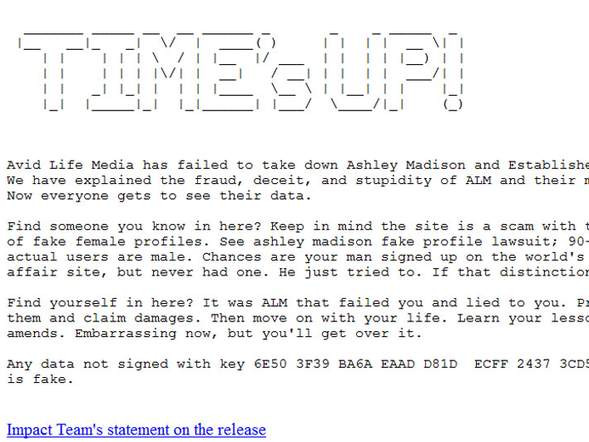
On top of the embarrassing personal information leaked by the Impact Team when they dumped the details of more than 32m users from the cheating website Ashley Madison on the dark web, the hackers included the information of millions of credit card transactions.
Using the leaked list, fraudsters and blackmailers can piece together a variety of information about users of Avid Life Media websites users including their addresses, phone numbers and the last four digits of their credit card number, linked to the address.
If you have not yet checked to see if you have been exposed in the Ashley Madison leak, the safest and most reliable way to do so is through haveibeenpwned.com, created by Microsoft security developer Troy Hunt.
Other databases exist and may offer more information but the use of all these databases comes with a health warning. Some websites have been harvesting users email addresses and spamming them with advertising and the websites themselves, or pop-ups and adverts that could contain malicious spyware. Users should remain circumspect while accessing untested sites.
Contained within the dump was almost 3GB of transaction data according to theverge.com. The information appears to include 9,693,860 credit card transactions in total but, despite the vast amount, it appears not many users will be at direct risk unless they used weak passwords.
Hunt, who has blogged extensively on the Ashley Madison data breach and its security implications, explained that so long as customers replace their cards (which he describes as "no biggie") and created unique passwords then users should be fine. He did say however that if this was not the case then "someone could've, you know, just gone and reset pretty much every other account you have on the web".
Matt Little, vice president of product development at PKWARE, an international data security and smart encryption company, told IBTimes UK that internet users needed to be careful about what they shared on the web. "Information has value. It needs to be protected the same way we protect our valuable physical assets," he said
Ashley Madison protected its users passwords using byrypt, which effectively renders them useless to a hacker. Little explained encrypting the entire database, not just the passwords was "essential to protect customer privacy and is absolutely required for sites like Ashley Madison that have customers expecting privacy".
But, again, this will only protect Avid Life Media customers who used strong, unique passwords, and this appears to not always have been the case.
A survey by Dashlane, a password management service, has found that users of all dating websites have a tendency to use weak passwords. Ashley Madison was found to score 30 out of 100 according to the service in terms of password strength. Dashlane's experts assessed each site on 19 different criteria, including the minimum length of the required password and whether there was a requirement for a mix of letters and numbers.
The study also assessed whether the website made a password visible on entry, and whether it rejected common passwords, such as '12345678' or 'letmein'.They found that although they store highly sensitive data, dating websites lag behind major mainstream services in their approach to user password policies.
Fraud is not the only threat users with leaked data face. Blackmailers have already pocketed a believed $6,400 from the leak after they sent extortion emails.
Little explained: "This is a wakeup call. We need to think about this from an information perspective. We need to protect our valuable, sensitive and sacred information. It will get into the wrong hands. We need to armour data at its core, with encryption rending the information useless."
© Copyright IBTimes 2025. All rights reserved.






















