What is Kronos? A brief history of the Trojan linked to WannaCry hero Marcus Hutchins
The arrest of MalwareTech caused a shockwave - so what exactly is accused of creating?

A banking Trojan known as 'Kronos' has hit the headlines following the arrest of Marcus Hutchins, a 23-year-old British security expert who was widely credited with stopping a global cybersecurity crisis in May 2017. According to the FBI, Hutchins "created" it.
The federal indictment naming Hutchins, who used the name 'MalwareTech' online, clearly stated the accusation in black and white. The suspect was arrested after travelling to the US for Defcon, an annual hacking conference. But what exactly is the Kronos Trojan and what does it do?
The first references to the malware emerged back in 2014 from a cybersecurity division of IBM, who found that the malicious Trojan had been made available for sale in a Russian underground forum.
It was being advertised for $7,000 (£5,330) and claimed to be able to evade detection from anti-virus software.
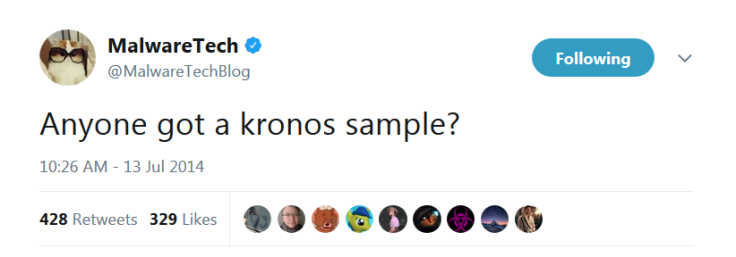
Kronos was a form of banking Trojan, meaning it came disguised as legitimate software but could, in reality, steal usernames and passwords. IBM's team disclosed the find on 11 July 2014. Two days later, MalwareTech tweeted: "Anyone got a kronos sample?"
Continuing with references to Greek mythology, the Trojan – also reportedly linked to a botnet of infected computers - was "compatible" with Zeus, another popular banking malware.
On the criminal marketplace, the Kronos seller (who, of course, is not confirmed to be Hutchins) was offering a one-week test for $1,000. The payment method – like most other forms of cybercrime – was in bitcoin, which remains one of the popular forms of digital currency to this day.
It all went rather silent until 2 October 2015, when IBM found that Kronos was targeting banks in the UK and India. "Kronos's new configuration includes more strategic updates, including elaborate web injection schemes for some of the banks it targets," experts stated at the time.
A year later, on 15 November, cybersecurity firm Proofpoint released analysis saying that its researchers "observed several relatively large email campaigns" distributing Kronos. On 10 and 14 November, the team spotted swathes of spam hitting healthcare and hospitality targets.
How exactly Hutchins is linked to Kronos remains unclear. In its indictment, published 3 August 2017, the US Department of Justice (DoJ) referenced a second unnamed defendant who reportedly sold the malware on an underground marketplace called AlphaBay for a total of $3,000.
AlphaBay was recently dismantled following a global cybercrime operation.
Hutchins became a well-known figure in the cybersecurity community after stopping the spread of "WannaCry" ransomware in May 2017 by locating a killswitch hidden in its code. The malware eventually spread to 300,000 machines across 150 countries, authorities said.
In the wake of his arrest, friends and supporters refused to believe Hutchins was involved in the creation of Kronos. The 23-year-old was a security researcher by trade and, they said, must have simply been analysing the Trojan's code. At this point, such views remain speculation.
After rising to prominence, Hutchins reportedly worked in some capacity with British intelligence agency GCHQ. The National Cyber Security Centre (NCSC), a fork of the agency, said on 3 August: "This is a law enforcement matter and it would be inappropriate to comment further."
© Copyright IBTimes 2024. All rights reserved.






