Who are Lizard Squad? The hackers who took down PSN, Xbox Live and Facebook

Lizard Squad is a group of up to 15 hackers which is gaining notoriety for attacking major companies like Sony, Microsoft and Facebook in order to publicise its hacking tool known as Lizard Stresser.
The group is gaining increasing notoriety in 2015 as it claims credit for an increasingly high-profile list of attacks on major online targets including the PlayStation Network and even Facebook.
Here we look at the group, their attacks, the service they are selling and whether or not they are really linked to Islamic State:
PSN, Xbox Live, Facebook and Tinder attacks
Lizard Squad first came to the world's attention last August when it began attacking a range of online games and gaming networks.
The group claimed credit for knocking games such as Runescape and World of Warcraft offline, however it was only when it claimed credit for a major attack against Sony's PlayStation Network on Sunday 24 August that Lizard Squad began to get the attention of the media.
In the following months the group retained a low profile, but in December it ramped up its activities significantly.
At the beginning of the month it carried out denial-of-service attacks against the PlayStation Network (PSN) and Xbox Live warning users that more serious attacks would happen over Christmas.
The group followed through on this promise knocking both gaming networks offline for significant periods over Christmas, and projected the group into the mainstream media's attention for the first time.
The attacks caused widespread anger among gamers around the world and they were only stopped when the group accepted an offer from internet entrepreneur Kim Dotcom of 3,000 vouchers for his Mega cloud storage service worth $99 (£65) each.
Also in December, the group claimed responsibility for knocking the whole of North Korea offline in a distributed-denial-of-service attack on 22 December for a period of 24 hours.
On 26 December the group also attempted to attack the Tor network though the relevance of the attack was questioned when it was revealed the group only managed to take control of 0.247% of the entire network.
On 26 January the group defaced and knocked offline the website of Malaysia Airlines, claiming to have obtained some customer data in the attack and saying it plans to release the information at some point.
On 27 January, the group claimed responsibility for what would be its largest and most daring attack to date - knocking the 1.35 billion users of Facebook offline. The social network, along with Instagram, Tinder and AIM were all knocked offline for 40 minutes, with Lizard Squad claiming there "is more to come soon" following the attack.
ISIS link
Ever since the group began carrying out attacks last August, the group has consistently mentioned Islamic State during its attacks.
In August, the media's interest was piqued by apparent claims that Lizard Squad had taken down the PlayStation Network in the name of the Islamic State, claiming that "Kuffar [non-muslims] don't get to play videogames until bombing of the ISIL stops."
The account went on to say:
Today we planted the ISIS flag on @Sony's servers #ISIS #jihad pic.twitter.com/zvqXb2f5XI
— Lizard Squad (@LizardSquad) August 24, 2014Things escalated even further when a single tweet from the account led to an American Airlines flight carrying the president of Sony Online Entertainment, John Smedley, to be diverted following a bomb threat:
.@AmericanAir We have been receiving reports that @j_smedley's plane #362 from DFW to SAN has explosives on-board, please look into this.
— Lizard Squad (@LizardSquad) August 24, 2014In January, when the group knocked the website of Malaysia Airlines offline, it initially replaced the homepage with a holding page claiming it was "Hacked by Cyber Caliphate" and encouraged visitors to follow the group on Twitter.
Cyber Caliphate is the hacking wing of Islamic State (IS) which is thought to be responsible for a recent hack of the US Central Command's Twitter and YouTube accounts.
The link to Islamic State is tenuous and is likely just a marketing ploy used by Lizard Squad to get more coverage by the media, thereby raising the profile of its hacking tool.
The Lizard Squad Twitter account (which has now been suspended) was created in August 2011, meaning it is highly unlikely that it is linked to a movement that begun in April 2013.
Lizard Stresser: DDoS-for-hire
LizardStresser is a DDoS-for-hire tool which the group of hackers sell for as little as $6 up to $500 to those looking to knock other websites or individuals offline.
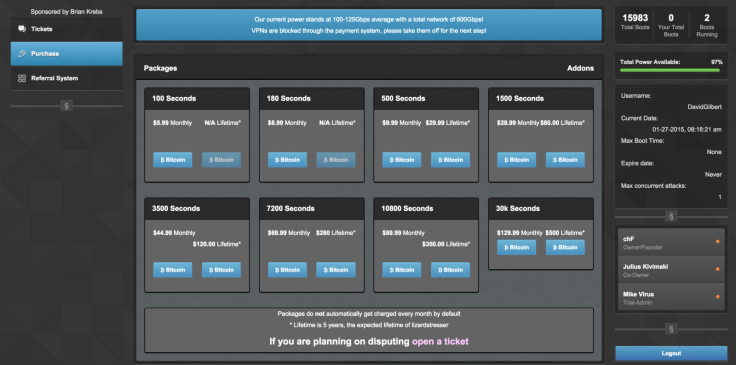
Security researcher Brian Krebs discovered that the tool was using a network of thousands of hacked home routers to carry out the attacks.
Known as a "booter" or "stresser" service, the website LizardStresser.su is hosted in Bosnia and is able to use the network of home routers as they are typically only protected by factory-default usernames and passwords.
The group said that all its attacks are just ways of advertising the hacking tool by showing off just how powerful it is.
Lizard Squad are a group of rogue hackers who shot to fame in December when they knocked the PlayStation Network and Xbox Live offline for a sustained period of time over Christmas.
Since then the group has begun selling a tool called LizardStresser which is a DDoS tool allowing willing parties to pay to knock another individual or business offline. The group uses its own attacks to promote the tool.
Arrests
Since the attacks on PSN and Xbox Live in December, authorities in the US and UK have been carrying out a major investigation resulting in several arrests in the UK in recent weeks.
On New Years' Eve a 22-year-old from Twickenham was arrested on suspicion of fraud by false representation and Computer Misuse Act offences, and is scheduled to appear in court again on 10 March.
This week, a teenager from Southport near Liverpool was arrested in relation to the attacks on PSN and Xbox Live, as well as so-called swatting offences - the term used to describe the act of knowingly providing false information to law enforcement about a target.
In an interview last year, the Southport teenager claimed that Lizard Squad had up to 15 members.
© Copyright IBTimes 2025. All rights reserved.


























