CryptoHitman: Jigsaw ransomware rebrands as porn-peddling cybercrime tool

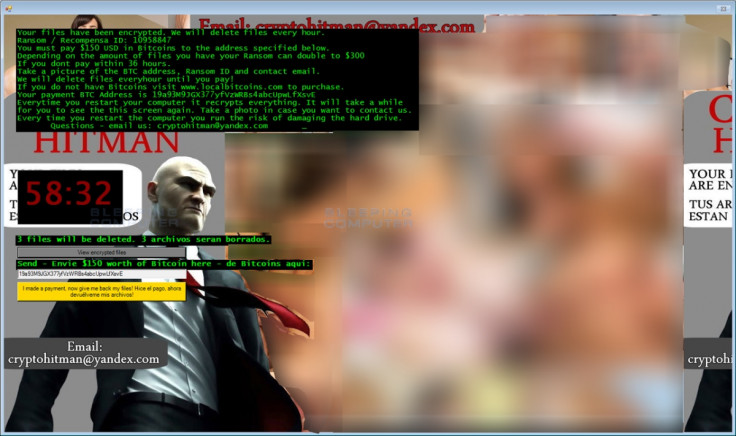
A ruthless strain of ransomware known as Jigsaw has ditched its namesake pop-culture icon from the Saw movies and now serves its victims with an image of video game character Hitman alongside hardcore pornography, according to security experts.
Despite the rebrand, the crypto-ransomware – now under the CryptoHitman moniker – researchers warn it remains an effective cyberweapon. The tool is able to lock down a computer system until a 'ransom' is paid. But what sets it apart from other malware strains is that it displays a countdown clock and deletes a selection of files every hour until the money is paid.
Lawrence Abrams, a security researcher with Bleeping Computer, said: "Like the previous Jigsaw ransomware infections, CryptoHitman will encrypt your data with AES [Advanced Encryption Standard] encryption and demand a ransom payment. Unfortunately, this version will still delete your files every time you restart the process and when the timer runs down to zero.
"The only major differences is the new pornographic locker screen, the use of the Hitman character, the new .porno extension that is added to all encrypted files, and new filenames for the ransomware executables. Otherwise, this ransomware performs the same as the original Jigsaw ransomware."
When it first emerged, the Jigsaw ransomware quickly gained notoriety for its extortion capabilities. As previously reported, it can target more than 120 file extensions and demands $20-$200 (£14-£140) from the unfortunate victim. What's worse, if no money is paid within 72 hours it is designed to delete everything on the infected hard drive.
Luckily, a researcher called Michael Gillespie, who was involved with finding a cure for the original Jigsaw strain, has tweaked his 'decryptor' tool so that it now works with CryptoHitman – which, like its predecessor, spreads to users via spam email and malicious attachments. Once the files have been vanquished from a computer, the researchers highly advise running a strong anti-malware programme and a virus scan to ensure the system is free from infection.
The threat of ransomware is becoming an increasing problem for all internetusers – from governments to law enforcement to businesses. In one recent precedent-setting case, a US-based hospital was forced to pay $17,000 (£12,000) to regain access to crucial systems that had been encrypted by a cybercriminal.
Have you been infected with the CryptoHitman ransomware? Get in touch: j.murdock@ibtimes.co.uk or @Jason_A_Murdock
© Copyright IBTimes 2025. All rights reserved.




















