Marcher malware: Triple threat Android banking attack uses phishing, Trojan infection and data theft
Hackers prompt victims to download a malware-ridden banking security app that requests "extensive permissions".

Security researchers have discovered a new banking attack campaign that combines credential phishing, Trojan infection and data theft to target customers of major Austrian banks. Hackers have merged phishing with the distribution of the notorious Android banking malware called "Marcher", which has been active since 2013, researchers at Proofpoint said.
The new attacks begin with a banking credential phishing scheme followed by tricking the user into installing the Marcher malware. Hackers then attempt to steal the victim's credit card data using the banking Trojan itself.
According to Proofpoint, the latest Marcher campaign has been targeting customers of Bank Austria, Raiffeisen Meine Bank and Sparkasse since at least January 2017.
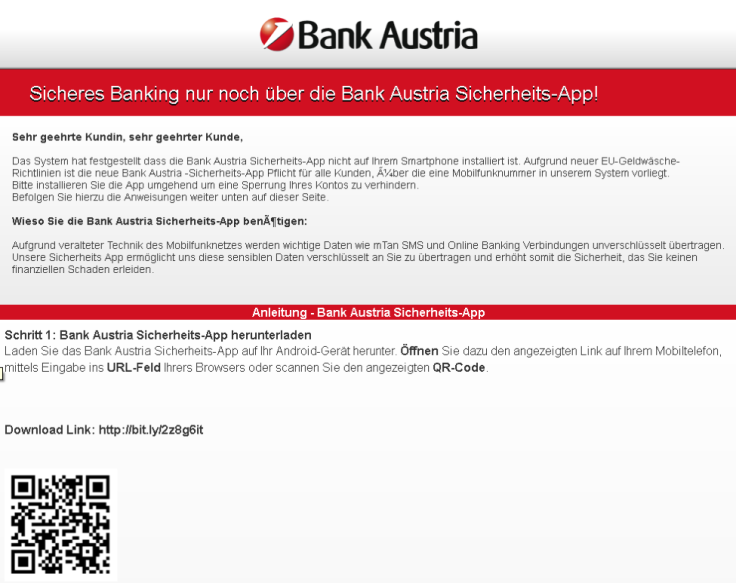
Although the Marcher malware is usually distributed via SMS, this campaign distributes the malicious code via a link in an email. The Bit.ly shortened link leads the unsuspecting victim to a phishing page that appears to be a legitimate banking page and prompts them to divulge their banking login credentials and account number and PIN. It then asks the user the login using their email address and phone number.
These acquired details are then used in the next stage of the attack when the threat actors ask the victim to download the "Bank Austria Security App" on their smartphone or risk having their account blocked.
The warning message, translated from Austrian, reads:
"The system has detected that the Bank Austria Security App is not installed on your smartphone. Due to new EU money laundering guidelines, the new Bank Austria security app is mandatory for all customers who have a mobile phone number in our system. Please install the app immediately to avoid blocking your account."
The user is then directed to another shortened URL that claims to lead to the installation of the app. However, the app is actually a version of the Marcher banking Trojan called "BankAustria.apk" that requests extensive permissions during installation that enable the malware's nefarious activities.
Some of them include writing and reading external storage, access to precise location, full control over SMS messages, initiating a phone call without going through the dialler user interface to let the user confirm the call, reading contact data, reading and writing system settings, and even locking the device.
"Once installed, the app will place a legitimate looking icon on the phone's home screen, again using branding stolen from the bank," Proofpoint researchers said. Besides operating as a banking Trojan, it also asks victims for their credit card information whenever they open apps such as the Google Play Store using stolen branding.
The threat actors also ask for other personal information, including date of birth, address and password, to make sure they have all the information needed to successfully exploit the stolen credentials.
Nearly 20,000 people have potentially unknowingly handed over their personal data and financial details to hackers, according to Proofpoint.
Researchers have warned that threats spanning across both desktop and mobile platforms are likely to increase in the future.
"As we use mobile devices to access the web and phishing templates extend to mobile environments, we should expect to see a greater variety of integrated threats," researchers said. "Attacks involving Marcher have become increasingly sophisticated, with documented cases involving multiple attack vectors and a variety of targeted financial services and communication platforms."
Users have been advised to be wary of any suspicious domains and skeptical of any emails or messages from banks that ask them to divulge any confidential credentials. Mobile users should also be skeptical when downloading any new apps outside of legitimate app stores, particularly those that request extensive permissions that seem to be unrelated to their primary function.





















