Businesses Aware of Cyber Threats, They Just Can't Stop Them
Enterprises are aware there is a serious threat from cyber-attacks, but they are simply not doing enough to protect themselves, or the systems they have in place are not working.
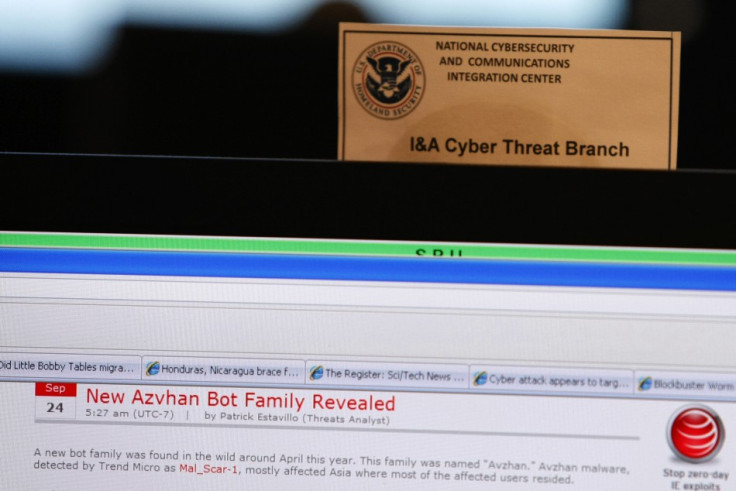
Hacking and cyber-attacks are growing in prominence and sophistication with three distinct factions emerging. One is the nation-state sponsored cyber espionage groups, as highlighted by recent Mandiant report into the Chinese-government sponsored hacking conclave, infiltrating over 140 organisations over a seven year period.
The second group are cyber activists, or hactivists, represented by the Anonymous collective who use tactics such as Distributed Denial of Service (DDoS) attacks to disrupt and cripple their targets. Hacktivists are not interested in money, but are doing it for a cause.
Both these groups don't impinge directly on individuals or businesses to a major degree, but the final group, cyber-criminals, are increasingly targeting enterprises, gaining access to their systems and stealing valuable data which can be easily traded on the black market.
A report by analyst firm Quocirca, commissioned by security firm Trend Micro, claims that over 70 percent of European businesses are victims of targeted cyber-attacks, while the rest have simply not noticed yet.
Cyber-attacks by criminals have evolved from the scatter gun approach of a few years ago to the laser-focused targeted attacks today, which have the dual purpose of by-passing traditional security measures and looking more viable to the intended victim.
Engineered
Cyber criminals use social engineering to craft emails and attachments which look as if they come from someone you know, are written using the correct language, and which contains information which is timely and related to you and your work.
According to Quocirca, although awareness of the growing threat from targeted attacks is improving amongst European organisations, most are still failing to muster an effective response.
The problem is that these targeted attacks are not stopped by traditional security measures such as firewalls and anti-virus software.
And things are only likely to get worse in 2013, according to Rik Ferguson, VP of Security Research at Trend Micro. He points to the already high incidences of hacking reported in the first six weeks of the year and believes that this year will see the threat go mobile.
Mobile
Targeted attacks are currently aimed at computers running the Windows operating system. Once a malicious attachment or link in the targeted email is opened, a piece of code is silently executed in the background, taking advantage of any one of a number of known vulnerabilities.
This opens the door to allow malware to be downloaded to the computer, which scans for relevant information which it packages up before uploading to the criminals at the other end.
Cyber criminals are currently using highly-automated exploit kits which they rent or buy from the computer scientists who create them. It means that cyber criminals don't have to have much technical knowledge to carry out these attacks and has seen an explosion of criminal gangs getting involved in this type of attack.
Ferguson told IBTimes UK that the company had been tracking these exploit kits and has spotted a worrying new feature. The exploit kits are now gathering information about Windows 8 and mobile operating systems, which can only mean the criminals are developing cross platform exploit kits and Ferguson says: "If this can be achieved on mobile, everything changes."
The move to mobile is one which security companies have been flagging for some time now, but it has previously been thought the main threat was posed by malicious apps being distributed through the app store.
BYOD
With the advent of the Bring Your Own Device (BYOD) phenomenon, more work is being carried out on smartphones, with emails being checked out of office hours. Currently if you open an email on your smartphone which is part of a targeted attack and click on a malicious link, nothing will happen, as the exploit behind it only works on the Windows desktop operating system.
However with cross platform support, it would mean that no matter what device you opened the malicious link or attachment on, it would infect you system.
Defending against these attacks is a major worry for businesses, and according to the Quocirca report, just 29 percent of enterprises with between 2,500 and 5,000 employees have deployed technology specially designed to prevent targeted attacks. That figures is slightly higher (41 percent) for larger companies.
Among the advanced defence techniques being used are network traffic inspection, white listing, sandboxing and behavioural analysis.
However, as these advanced techniques are put in place, the criminals are evolving their exploit kits in order to avoid detection. For example, sandboxing, which sees code executed in a virtual environment to see if contains anything malicious before being installed, is no longer a fool-proof measure.
Malware typically stops when it detects it is running in a virtual environment as this had indicated it was running in a sandbox. However, with enterprises moving in a big way to virtual environments, malware creators are now investing their time in sandbox avoidance techniques, rendering current security techniques redundant.
"We are all Mat Honan"
Ferguson believes that as more and more of our lives move online and into the cloud, securing our data is going to become even more difficult.
"Everything we do is becoming increasingly linked to everything else. The more everything becomes interlinked, the more invisible it becomes to us and the easier it makes it to get into someone's life."
Ferguson referenced Mat Honan, the Wired journalist who had his digital life stolen by hackers last year, saying: "We are all Mat Honan."
© Copyright IBTimes 2025. All rights reserved.





















