Snowden Obtained Top Secret NSA Passwords Simply by Asking for Them
Edward Snowden gained access to top secret National Security Agency documents by persuading colleagues to hand over their usernames and passwords, claiming they were needed for his computer administration role.
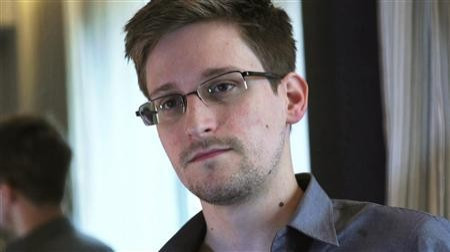
The sensitive information was unwittingly given to Snowden by fellow workers at a spy base in Hawaii, where he worked as an NSA contractor hired by US consultancy firm Booz Allen.
Speaking to Reuters, sources close to several US government investigations said a handful of agency employees who gave their details to Snowden were identified, questioned and removed from their assignments. The sources do not know if the employees were moved to other assignments or fired.
Snowden worked at the NSA's Hawaii site for a month in the spring of 2012, during which time he downloaded tens of thousands of secret NSA documents.
It is thought that Snowden, who fled Hawaii for Hong Kong and then Moscow after he began leaking the stolen classified documents, may have persuaded between 20 and 25 fellow workers to give him their login details, telling them they were needed for him to carry out his job as a computer systems administrator.
Worst breach
The handing over of these passwords subsequently led to the worst breach of classified data in the NSA's 61-year-history, and is another example of inadequate security measures employed by the agency.
In October it was reported that the NSA's Hawaii site had failed to install the most up-to-date security software used to prevent data leaks, leading Snowden to download the sensitive files belonging to the agency and its UK counterpart, Government Communication Headquarters (GCHQ).
The revelation of how Snowden used colleagues' passwords came to light as the US Senate Intelligence Committee approved a bill intended to tighten security surrounding US intelligence data. One provision of the bill would be to use a classified sum of money to fund the installation of new software designed to identify and record unauthorised attempts to download secret material.
The insider threat
Steve Aftergood, a secrecy expert with the Federation of American Scientists, told Reuters: "In the classified world, there is a sharp distinction between insiders and outsiders. If you've been cleared and especially if you've been polygraphed [lie detector test], you're an insider and you are presumed to be trustworthy. What agencies are having a hard time grappling with is the insider threat, the idea that the guy in the next cubicle may not be reliable."
Sources "familiar with efforts to access the damage" to US intelligence caused by Snowden's leaks say investigations into the data breach are progressing slowly because the whistleblower obscured some electronic traces of how he accessed the documents.
Read more: Security Committee Examination of Spy Chiefs Labelled Inadequate
© Copyright IBTimes 2025. All rights reserved.





















