Fin4 cyber-gang tricks Wall Street companies to play the stock market

A highly sophisticated cyber-crime gang, known as Fin4, is stealing data from more than 100 public companies in order to play the stock market.
The group, which is based in the US or Western Europe and has been operating for over a year, collects data from the companies themselves, their advisory firms and all parties who handle insider information in order to get a clear trading advantage.
The on-going attacks don't rely on malware but utilise targeted phishing and social engineering campaigns along with deep subject matter expertise to "deliver weaponised version of legitimate corporate files" according to a report entitled 'Hacking the Street' from US security firm FireEye, which has been tracking the group since mid-2013.
FireEye has not been able to estimate how much money the group has made from its campaign to date, but says its "network activities must reap enough benefit to make these operations worth supporting for over a year - and in fact, Fin4 continues to compromise new victims as we finish this report."
The strong command of English colloquialisms, regulatory and compliance standards as well as in-depth industry knowledge lead FireEye to surmise that Fin4 is based in the US itself or in Western Europe.
"Advanced threat actors conducting attacks to play the stock market to their advantage has long been a worry but never truly seen in action," said Dan McWhorter of FireEye. "FIN4 is the first time we are seeing a group of very sophisticated attackers actually systematically acquire information that only has true value to a criminal when used in relation to the stock market."
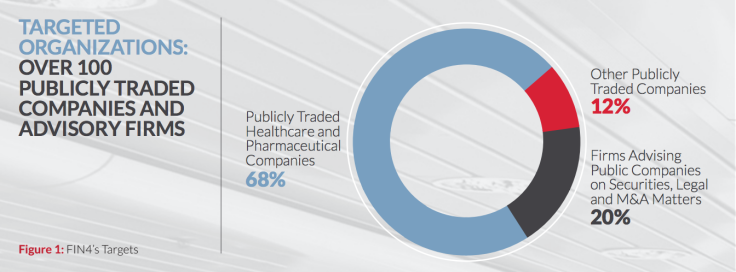
Over two thirds of the targeted organisations are healthcare and pharmaceutical companies according to FireEye, probably because stocks in these areas can move dramatically in response to news of clinical trial results, regulatory decisions or safety and legal issues.
The security firm believes Fin4 intentionally targets individuals who have inside information
about events that will cause the price of stocks to rise or fall substantially in a short period of time. These include C-level executives and senior leadership, legal counsel, researchers and scientists.
The Fin4 gang are highly organised with FireEye identifying over 70 separate identifiers to specify who their targets are and track what they do.
Using spear phishing campaigns the group is able to earn the trust of their targets and obtain login details to monitor email traffic.
"Fin4 knows their audience. Their spear-phishing themes appear to be written by native English
speakers familiar with both investment terminology and the inner workings of public companies. Fin4's phishing emails frequently play up shareholder and public disclosure concerns."
The group has also been observed targeting several parties involved in a single deal, and using compromised email accounts in one advisory company to target and compromise another one involved in the deal.
© Copyright IBTimes 2025. All rights reserved.
























