Link Between Flame and Madi Viruses Discovered
A security company has found a piece of code in the Madi malware which could indicate a link with the highly-complex, cyber espionage weapon known as Flame.
Seculert, the company which originally identified the Madi malware (also known as Mahdi), has been examining the code since it was first discovered, and within the code for the malware its experts have found a link to the highly-complex and contentious computer virus known as Flame.
Flame was uncovered back in May and has since been found to share a common heritage with Stuxnet, a highly sophisticated cyber weapon which was jointly developed by the US government and Israel to target and disrupt the uranium enrichment plant at Natanz in Iran.
When Madi was discovered earlier this month, it was seen as a rudimentary piece of computer malware, which had nothing in common with the highly-complex Flame virus, which used ground-breaking cryptography during its development.
However, following further analysis, Seculert has discovered a link.
Flame link
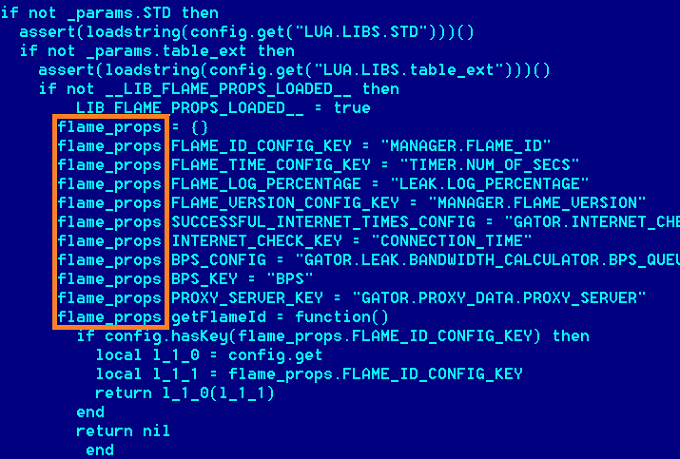
Madi, a new and improved version of which has appeared this week, is targeting victims in the Middle East, and each victim is assigned a unique identifier, which is used by the remote command-and-control server to identify which infected PC it is communicating with.
Part of this unique identifier is a prefix, which is used to help spread the targeted PCs between the members of the group controlling the malware, and allow them to identify and manage a bulk of targeted entities -and one of the prefixes in use is 'Flame'.
Seculert says that the first targeted victim with the 'Flame' prefix began communicating with the C&C server in early June, straight after Kaspersky Lab discovery of Flame went public.
While this is not an indication that the creators of Madi are the same people who are behind the Flame virus, it is surely more than a coincidence.
Joint research into Madi by Kaspersky Labs and Seculert, which tagged the malware as amateurish and rudimentary, said most of the 800 identified victims were located in Iran. The semi-offical Iranian state media outlet FARS News Agency reacted angrily, saying the Western media was seeking to play down Iran's cyber capabilities.
"The western media sought to play down Iran's cyber and computer software capability by releasing hundreds of reports on the discovery of a new computer virus and attributing the semi-professional malware to Iran."
Analysis this week by Symantec, has contradicted the location of the majority of PCs infected by Madi, saying that 72 percent of them were Isreal, with Saudi Arabia the next highest penetation of infected PCs, with 8 percent. Symantec said it hadn't identified any infected PCs in Iran - though it did identify command-and-control servers located in the country.
Among the victims specifically targetted were oil companies, US-based think tanks, a foreign consulate, as well as various governmental agencies, including some in the energy sector.
© Copyright IBTimes 2025. All rights reserved.





















