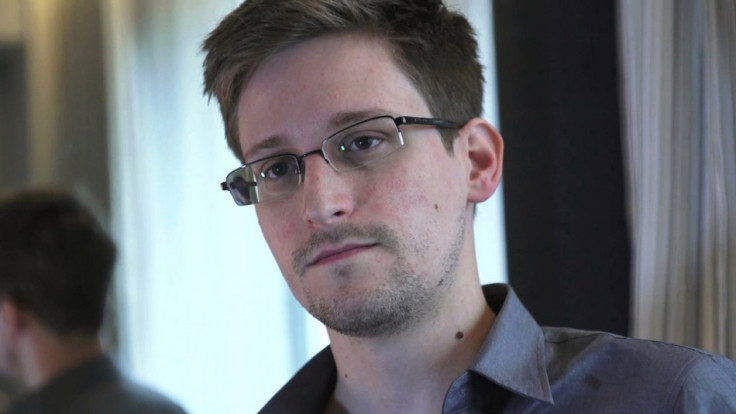
New Edward Snowden Leak 'Reveals Inner Workings of NSA's Surveillance Tool'
NSA whistleblower Edward Snowden has revealed a new batch of slides claiming to document a computer system allowing the National Security Agency to search through a vast database of emails, browsing histories and the private Facebook messages of millions of individuals.
Published by Glenn Greenwald in the Guardian, the training material from 2008 explains how a programme called XKeyscore works, which the documents claim to be the NSA's "widest-reaching" system for obtaining intelligence from the internet. All 32 slides can be viewed here.
One slide claims that data held by the XKeyscore database covers "nearly everything a typical user does on the internet," including "the content of emails, websites visited and searches, as well as their metadata," the Guardian claims.
Despite insistence that NSA surveillance can only be performed on non-US citizens, Greenwald claims XKeyscore "provides the technological capability, if not the legal authority, to target even US persons for extensive electronic surveillance without a warrant provided that some identifying information, such as their email or IP address, is known to the analyst."

XKeyscore can be used by NSA staff and contractors to search for the communications of individuals by providing their name, telephone number, IP address, keywords, the language in which the communication was conducted, or the type of web browser used.
Facebook chats
Beyond emails, it is claimed that XKeyscore can be used to monitor activity within social networks. An NSA tool called DNI Presenter can be used to "read the content of stored emails," and also enables an analyst using XKeyscore "to read the content of Facebook chats or private message. An analyst can monitor such chats by entering the Facebook user name and a date range into a simple search screen."

One slide claims the programme allows NSA staff to access "nearly everything a typical user does on the internet" thanks to the ability to search HTTP activity by keyword. The slide shows company logos for Facebook, Yahoo, Twitter, MySpace, CNN, Wikipedia, Google and Gmail.
It's not just people that can be tracked by XKeyscore, but traffic to a specific website too. One slide states: "If you know the particular website the target visits. For this example, I'm looking for everyone in Sweden that visits a particular extremist web forum."
The slide then shows an annotated page of search boxes where an NSA analyst could enter a website address, although with a 'justification' for their search, such as it containing extremist content.
Terabytes
Explaining the quantity of data collected by XKeyscore, Greenwald says the system "is continually collecting so much internet data that it can be stored only for short periods of time. Content remains on the system for only three to five days, while metadata is stored for 30 days."
Greenwald adds: "One document explains: 'At some sites, the amount of data we receive per day (20+ terabytes) can only be stored for as little as 24 hours'."
The slides also say that in 2012 there were at least 41 billion total records collected and stored in XKeyscore for a single 30-day period.

In a statement sent to the Guardian, the NSA said its activities "are focused and specifically deployed against - and only against - legitimate foreign intelligence targets in response to requirements that our leaders need for information necessary to protect our nation and its interests.
"XKeyscore is used as part of NSA's lawful foreign signals intelligence collection system. Allegations of widespread, unchecked analyst access to NSA collection data are simply not true. Access to XKeyscore, as well as all of NSA's analytic tools, is limited to only those personnel who require access for their assigned tasks.
"In addition, there are multiple technical, manual and supervisory checks and balances within the system to prevent deliberate misuse from occurring."
© Copyright IBTimes 2025. All rights reserved.





















