Superfish: Everything you need to know about Lenovo adware and how to remove it

Lenovo is shipping its laptops with a piece of software which not only serves up unwanted ads, but is able to snoop on your secure online communications.
This has huge security implications and could be a major problem for Lenovo's reputation.
Here we take a look at the software causing the problem - Superfish - to see how it works, which laptops are affected, and how you can get rid of the problem:
What is Superfish?
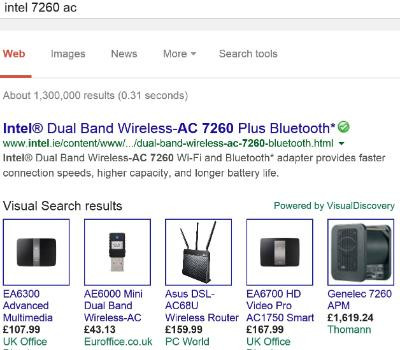
Superfish Visual Discovery is a piece of software which comes pre-installed on some Lenovo laptops. It is a browser extension which injects ads into Google search results as we see below on the left.
It promises to help "users find and discover products visually".
As well as being the name of the software, Superfish is the name of the company it with headquarters in Israel and the US. It says it has "developed the most advanced and scalable visual search technology in the world" and has been named America's 64th most promising company by Forbes.
However, Tom Fox-Brewster at Forbes has dug deeper into the company to find a history of malware complaints and surveillance.
That doesn't sound too bad?
Annoying yes, but not too bad - if that was all Superfish was doing. The software also installs a root certificate which allows it break the SSL encryption used by websites including Google, Amazon and your online banking to secure communication between their servers and your computer.
By breaking this security, it allows Superfish to monitor what are supposed to be private communications in order to serve more targeted ads. But even that is not the worst part.
This opens everything up to hackers. If they are able to extract the private encryption key used to sign every certificate it issues, then they will be able to monitor all communication on affected systems.
The scary thing is that within hours of this news hitting the headlines one security researcher has already cracked the password protecting the encryption.
That's not good, how does it work?
The problem is all related to certificates.
Every time you visit a website which uses SSL or TLS encryption (you know it is being used by the padlock symbol in the search bar), it checks that the person visiting the site is a legitimate person and not a malicious actor or security threat.
Certificates are issued by trusted Certificate Authorities (CAs) which are large security companies like Symantec. But because Superfish uses a self-signed certificate it replaces the website's security with its own, allowing it to insert adverts based on the content being sent/received.
This means that Superfish is able to generate a valid (from the browser's point of view at least) encryption certificate for any website using HTTPS, including Google, Facebook, Amazon or all online banking portals.
This leaves computers running Superfish wide open to what are called "man-in-the-middle" attacks by hackers.
Why is Lenovo shipping this on its laptops?
The simple answer is money. Superfish pays Lenovo for each and every laptop which ships with the software pre-installed, and they may have a deal to take a slice of advertising revenue generated by the software.
Lenovo has yet to reveal how much it is getting paid by the software company.
Which Lenovo laptops are affected?
This unfortunately is a grey area. IBTimes UK has asked Lenovo to specify which laptops are affected but so far there has been no answer.
The company has however confirmed that none of its enterprise-focused ThinkPad computers were compromised. In a post on the Lenovo forum in January, product manager Mark Hopkins said the software was bundled with "consumer products only" but what this means exactly is unclear.
Lenovo says that only laptops sold between October and December 2014 had SuperFish installed.
The company says it stopped pre-loading the Superfish software in January and has "disabled all server side interactions" however the root certificates - which are the main bone of contention with security experts - remain on users systems.
What does Lenovo say?
In its official statement, the Chinese company said:
Lenovo removed Superfish from the preloads of new consumer systems in January 2015. At the same time Superfish disabled existing Lenovo machines in market from activating Superfish. Superfish was preloaded onto a select number of consumer models only. Lenovo is thoroughly investigating all and any new concerns raised regarding Superfish.
In a post on the Lenovo forum on Thursday, 19 February, Hopkins added:
We have thoroughly investigated this technology and do not find any evidence to substantiate security concerns. But we know that users reacted to this issue with concern, and so we have taken direct action to stop shipping any products with this software.
It seems that Lenovo think there is no problem to address here - but it also seems to be ignoring the huge issue around the self-signing certificates and only addressing the issue about third-party ads, which in the scale of things is a minor issue.
How can I check if my laptop has Superfish installed?
Easy - visit this website on your Lenovo laptop and if you see a 'Yes' then check out the section below on how you go about uninstalling it.
If you see a 'No' then relax and have a cup of tea.
How can I uninstall Superfish?
Hopkins gives these instructions:
Uninstalling Superfish Visual Discovery
- Go to Control Panel > Uninstall a Program
- Select Visual Discovery > Uninstall
However, as he helpfully points out, "registry entry and root certificate will remain" meaning that the problem of your system being open to attack from criminals remains. This is something many users have already reported on Lenovo's forums.
The only way to effectively remove Superfish from your system is to back up all your files and install a clean version of Windows which doesn't come bundled with any third-party software.
Here are Microsoft's instructions on how to perform a clean install.
© Copyright IBTimes 2025. All rights reserved.




















