Android malware that can 'steal everything' for sale on underground Russian forum
The 'Svpeng' malware was rebranded 'CryEye Android Banker', security firm found.

A sophisticated strain of Android banking Trojan, known as "Svpeng", was recently enhanced with a keylogging capability that could let hackers "steal everything" on infected devices. Now, according to security firm SenseCy, the software is up for sale on the Russian underground.
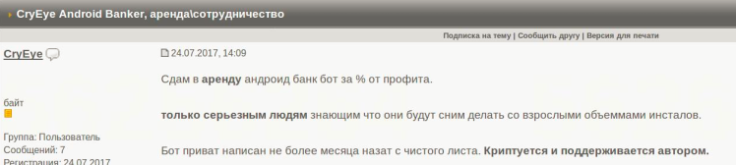
The malware, uploaded under the name "CryEye Android Banker", has also been offered for rent since mid-July 2017, experts revealed in a blog post. The culprits, who are believed to be Russian, are now touting the software in exchange for a "percentage of future profits" from criminals.
A description on the forum, which remains unnamed, said that after installation the banking Trojan attempts to exploit Android's accessibility services.
From there it can extract texts, contact lists and device logs before sending them directly to the malware operator's command and control (C&C) servers.
What alarmed researchers is that it now boasts a "keylogging" ability that can be used to hijack victims' usernames and passwords. Interestingly, SenseCy found that "neither the seller, nor his advertisement" had yet gained trust among other members of the forum.
The SenseCy report did not elaborate on how much the hackers were asking for the strain of banking Trojan, which has existed in a variety of forms since at least 2013. The Israel-based firm did not immediately respond to a request for comment from IBTimes UK.
On 31 July, a researcher from Kaspersky Lab found evidence that the Trojan was being distributed as a fake update for Adobe Flash Player. In a report, he claimed it was "one of the most dangerous" malware strains in the wild – but found circulation was still limited.
SenseCy's findings indicate that may soon change. Previous analysis found that the Trojan was able to spread across 23 countries in a single week. Infected users at the time spanned Russia (29%), Germany (27%), Turkey (15%), Poland (6%) and France (3%).
Additionally, there were clear signs that Svpeng's administrators were Russian – the biggest indicator being that the malware does not infect devices running the language. "This is a standard tactic for Russian cybercriminals looking to evade detection and arrest," the expert noted.
In November 2016, Kaspersky Lab revealed that Svpeng had infected more than 300,000 devices in just two months, with a rate of infection peaking at 37,000 victims in a day. Meanwhile, last year it was found to be stealing credentials via Google's ad network.
Security firm Sophos detects the malware as "Andr/Banker-GUA" and has dubbed it "Invisible Man".
"Android users have a new threat to worry about: keylogging malware that masquerades as a bogus Flash update and steals banking data," researcher Bill Brenner wrote on 2 August. "Needless to say, criminals in possession of your credentials will happily suck your bank accounts dry."
© Copyright IBTimes 2025. All rights reserved.




















