Hackers can now spy and track locations of phones using flaw in 3G and 4G LTE networks
The security vulnerability could reportedly pave the way for next-gen stingray devices.
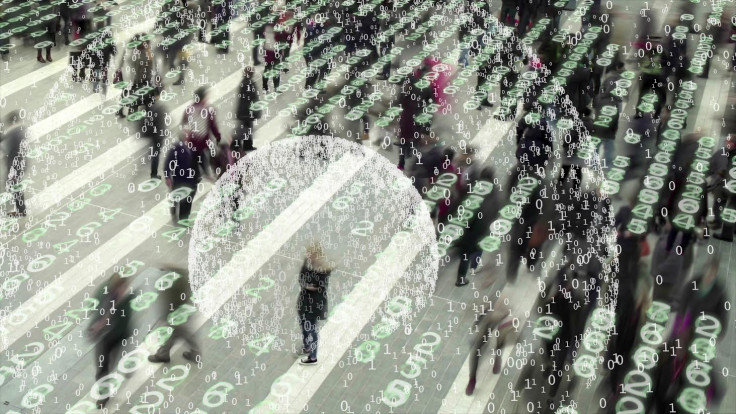
New vulnerabilities recently found in 3G and 4G networks can reportedly allow hackers to spy, monitor and track locations of phones. Security researchers also reportedly believe that the flaw could pave the way for next-gen low-cost stingray devices.
According to security experts Ravishankar Borgaonkar and Lucca Hirschi, who discussed their research at the BlackHat event in Las Vegas, the flaw was reportedly found in the authentication and key agreement of high-speed networks – which allows a phone to securely communicate with a user's network.
The flaw can reportedly allow hackers to monitor calls made, messages sent, as well as track the location of a phone. However, the vulnerability is limited and doesn't allow for messages or calls to be intercepted.
"Due to low-cost hardware and software setup, we would not be surprised to see criminal stalking and harassment to more mundane monitoring of spouse or employee movements, as well as profiling for commercial and advertisement purposes," Borgaonkar told ZDNet said.
The researcher said that the vulnerability could likely boost hackers' ability to create the "next generation" of stingray devices, which can cost as low as $1,500. He explained that the stingray-style intrusions could let hackers remotely gather information about a target, even when not constantly in the same area as the target.
ZDNet reported that Borgaonkar and his colleagues in Germany conducted several successful proof-of-concept attacks on various EU mobile networks. Researchers said that the nature of the flaw means that "all operators worldwide" and most devices are affected. Give that mobile OS don't currently have the ability to detect radio-level attacks, researchers say that "very little" can be done to protect against this threat.
According to the researchers, the telecoms standard organisation that allegedly developed the flaw-ridden protocol acknowledged the vulnerability and hope that the issue will be fixed in the impending 5G standards.
© Copyright IBTimes 2025. All rights reserved.




















