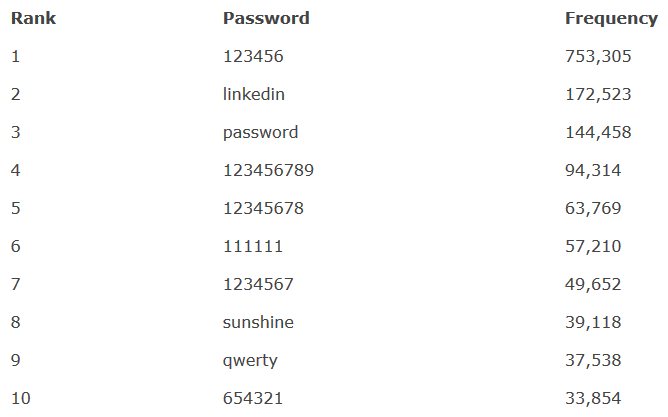
Has your LinkedIn been hacked? The 10 worst passwords used by members revealed

With major hacks and data breaches becoming almost a daily occurrence, it's more important than ever to make sure basic security measures are taken while surfing the web – including choosing a strong username and password.
However, if the recent LinkedIn breach is anything to go by, this fundamental aspect of digital protection is still being completely ignored by hundreds of thousands of people. A list of the most commonly used passwords from the hack has been released by LeakedSource, which analysed the breach and was able to easily decrypt 90% of the credentials.
The top password, rather embarrassingly for everyone involved, was '123456' with an astonishing 753,305 accounts. This was followed by 'linkedin' with 172,523 and then 'password' with 144,458. The list continues with '123456789' being used by 94,314 people, and 'qwerty' being chosen by nearly 40,000 members.
As previously reported, a hacker called 'Peace' is now attempting to sell the dataset containing 117 million LinkedIn user accounts on the dark web. While the data is from an older breach that occurred in 2012, the scale of the breach is far worse than previously reported.
At the time of the initial hack, it was estimated that 6.5 million encrypted passwords were stolen. It has since emerged to be significantly more widespread. Furthermore, the passwords were reportedly hashed with the recently depreciated SHA-1 algorithm – meaning they can now easily be cracked with modern technology.
Responding to the reemergence of the breached data, LinkedIn has attempted to play down the severity of the incident. It said there is "no indication that this is a result of a new security breach." However, the firm later enforced a password change on many users, with emails now being sent out to anyone the social media platform thinks was impacted.
In a statement, LinkedIn's security director Cory Scott said: "In 2012, LinkedIn was the victim of an unauthorised access and disclosure of some members' passwords. At the time, our immediate response included a mandatory password reset for all accounts we believe were compromised as a result of the unauthorised disclosure. Additionally, we advised all members of LinkedIn to change their passwords as a matter of best practice."
In a 18 May update, Scott added: "We have demanded that parties cease making stolen password data available and will evaluate potential legal action if they fail to comply. In the meantime, we are using automated tools to attempt to identify and block any suspicious activity that might occur on affected accounts."
© Copyright IBTimes 2025. All rights reserved.






















