Cyber Group Behind Kash Patel Email Hack Issues $50M 'Bounty' Threat on Trump and Netanyahu
Handala Hack team's bounty announcement raises security concerns

An Iran-linked cyber group formally attributed to Iran's Ministry of Intelligence and Security by the US Department of Justice has announced a $50 million (£39.5M) reward for those who can 'eliminate' US President Donald Trump and Israeli Prime Minister Benjamin Netanyahu. This declaration comes days after the same group claimed responsibility for breaching the personal email account of FBI Director Kash Patel.
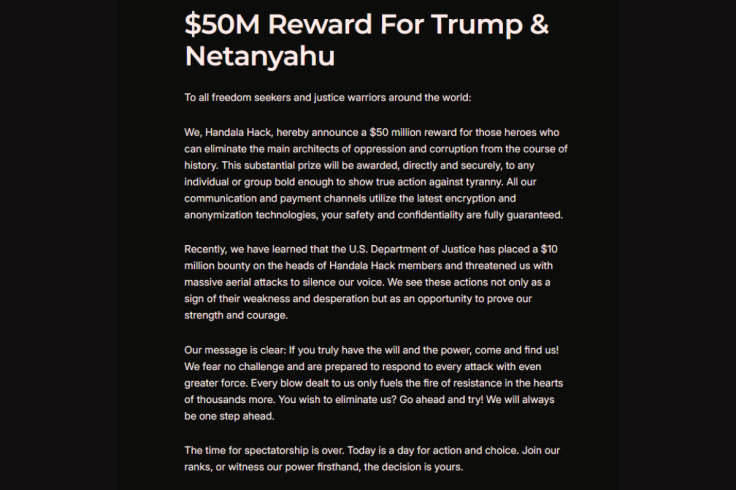
The group, known as Handala Hack Team, published the bounty announcement on its website, framing it as a call to 'all freedom seekers and justice warriors around the world.' The statement reads in part: 'We, Handala Hack, hereby announce a $50 million reward for those heroes who can eliminate the main architects of oppression and corruption from the course of history.' The announcement carries weight beyond rhetoric — the group has already demonstrated the operational reach to compromise one of America's most senior law enforcement officials.
Not Just Hackers Anymore
What makes the $50 million bounty declaration significant is less the figure itself and more the context surrounding it. The US Department of Justice formally accused Iran's Ministry of Intelligence and Security (MOIS) of operating Handala in March 2026, following the FBI's seizure of four of the group's websites. That formal attribution transforms the bounty from the posturing of a rogue hacktivist collective into something more structurally serious — a state-adjacent threat issued by a group with confirmed ties to a foreign government's intelligence apparatus.
Cybersecurity firms, including Check Point Research, track Handala under the name Void Manticore, which Check Point describes as 'one of the most active groups pursuing strategic objectives through cyber operations' on behalf of the Iranian regime. The group is also tracked under the names Banished Kitten, Storm-0842, and Red Sandstorm.
Iran International, the London-based Persian-language broadcaster that was itself a Handala target, has gone further, asserting that Handala and Storm-0842 are the same group functioning as a dedicated cyber unit within Iran's Ministry of Intelligence. According to Canada's Rapid Response Mechanism, multiple intelligence and threat research bodies — including the Atlantic Council, Recorded Future, and Trellix — have independently confirmed Handala's connections to MOIS-linked cyber units.
Patel Hack as Provocation and Proof
The Kash Patel email breach is central to understanding how the $50 million bounty fits into Handala's current operational posture. When the FBI seized four of the group's domains in mid-March, Director Patel announced the takedown himself, saying the bureau would 'hunt down every actor behind these cowardly death threats.' Handala's response was deliberate: it compromised Patel's personal Gmail account and published photographs and documents it claimed were taken from his inbox. A Justice Department official confirmed to Reuters that the account had been compromised and that the published material appeared to be authentic.
The sequencing suggests a deliberate escalation — targeting the official who announced their takedown before broadening the threat to two sitting heads of state, signalling that FBI enforcement action will be met not with retreat, but with expansion of scope.
A Documented History of Bounties
The $50 million figure is the largest bounty Handala has publicly announced, but it is consistent with an established and documented pattern. The group previously offered a $30,000 (approximately £23,700) reward for Israeli drone and air defence engineers, publishing their personal details, photographs, email addresses, and phone numbers alongside the declarations.
It also placed a $250,000 (approximately £197,500) bounty for the beheading of Iranian-American lawyer Elica Le Bon and former Canadian politician Goldie Ghamari, claiming to have shared their home addresses with cartel-linked partners. Threat intelligence firm FalconFeeds.io has assessed that the group's bounty system 'creates a direct and credible threat of targeted violence, kidnapping, or assassination attempts against named individuals.'
🚨 Threat Escalation 🚨
— Dark Web Intelligence (@DailyDarkWeb) March 24, 2026
The Handala group has issued a statement announcing a $50M reward targeting political leaders, alongside claims of secure communication channels and continued operations.
The message frames this as retaliation and calls for global participation.
⚠️ This… pic.twitter.com/gCUeWTp9M9
The $50 million announcement on Trump and Netanyahu also arrives alongside a separate campaign circulating on Iranian digital platforms, with Telegram-based posters claiming a $100 million (approximately £79M) reward for Trump's assassination, suggesting Handala's announcement exists within a wider ecosystem of Iran-tied incitement.
The formal US attribution of Handala to Iranian state intelligence means these threats exist in a different legal and diplomatic category than those from independent extremist actors. Security agencies in both Washington and Jerusalem are expected to treat the $50 million bounty declaration as a state-adjacent threat requiring a formal response, particularly given that the group has already shown it can breach the personal accounts of those at the highest levels of US law enforcement. Whether the announcement results in any tangible operational activity remains to be seen, but the pattern Handala has established suggests the group uses its public declarations as instruments of psychological pressure as much as operational intent.
© Copyright IBTimes 2025. All rights reserved.






















