Microsoft Raids Tackle Online Crime
Microsoft in collaboration with US Marshalls have raided two offices in a bid to disrupt one of the most pernicious forms of online crime, known as botnets, which capture and harvest bank account details and passwords.
Microsoft has been working with Financial Services - Information Sharing and Analysis Center (FS-ISAC) which represents 4,400 financial institutions and NACHA - The Electronic Payments Association - as well as Kyrus Tech Inc. to try and disrupt these botnets, or groups of computers, which are infected with the Zeus family of malware.
The system works by initially infecting an individual's computer with the malware. This is usually done by someone clicking on a link in a scam email - which a lot of the time looks like a security update from Microsoft itself.
Once the link is clicked, the malicious software searches for a security hole in your browser or other piece of software and installs itself on your PC. The Zeus software, and variants of it, then capture every keystroke a user enters which is related to online banking or credit card accounts. This allows the people using the malware to siphon off money from these accounts.
The software is also used to send out millions of spam emails from the users' accounts to help propagate the botnet. Since 2007, Microsoft has detected more than 13 million suspected infections of the Zeus malware worldwide, including approximately 3 million computers in the United States alone.
The raid on Friday targeted the people Microsoft believes is behind the Zeus, SpyEye and Ice IX botnets. SpyEye was initially set up as a competitior to Zeus and even went as far as to remove ZeuS if it found it on a computer that SpyEye was trying to infect. More recently the two code bases have been merged into a single piece of crimeware.
"With this action, we've disrupted a critical source of money-making for digital fraudsters and cyberthieves, while gaining important information to help identify those responsible and better protect victims," said Richard Boscovich, senior attorney for the Microsoft Digital Crimes Unit in a blog post. "The Microsoft Digital Crimes Unit has long been working to combat cybercrime operations, and today is a particularly important strike against cybercrime that we expect will be felt across the criminal underground for a long time to come."
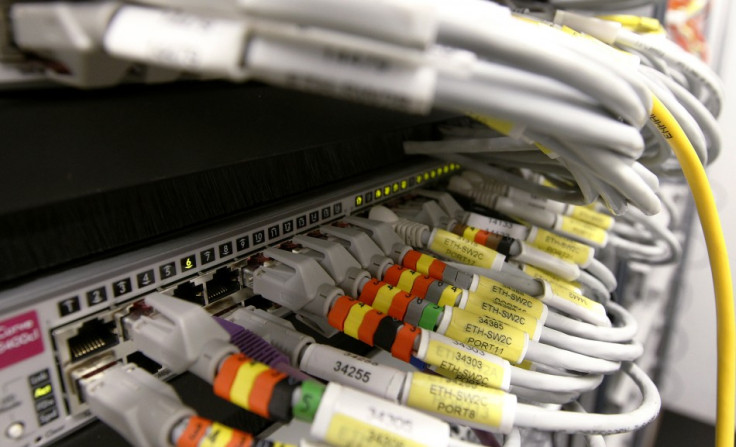
As a part of the operation Microsoft and its co-plaintiffs, escorted by US Marshals, seized command and control servers in two hosting locations in Pennsylvania and Illinois to seize and preserve valuable data and virtual evidence from the botnets for the case.
Microsoft and its partners took down two Internet Protocol addresses behind the Zeus command and control structure, and Microsoft is currently monitoring 800 domains secured in the operation, which are helping identify thousands of computers infected by Zeus. However this is just 800 out of a total of 3357 domain names across 35 registrars which have been identified by Microsoft.
Microsoft has been able to use the courts to attack these botnets thanks to a new approach by Boscovich, a former federal prosecutor. He has argued that the culprits behind botnets were violating Microsoft's trademarks through fake e-mails they used to spread their malicious software.
Using this approach Microsoft has been able to attack three botnets in the last few years through civil suits. It has allowed Microsoft to seize the computers behind these botnets without having to inform the owners ahead of time.
Zeus is one of most complex pieces of software Microsoft has tried to disrupt. The owners of the code offer it to customers for up to $15,000, which has resulted in many different variants of the Zeus software, making it even harder to fight. Microsoft believe that the people behind the Zeus botnet are based in Eastern Europe.
Microsoft estimate that since it first surfaced in 2007, the Zeus malware has been responsible for the loss of $100m through 13 million infected computers.
Because Zeus is so big, this action will not be a major blow to the botnet, but Microsoft has said this is just the first action in a major plan to upset the botnet working properly. "The plan is to disrupt, disrupt, disrupt," Boscovich said.
Rik Ferguson, a security expert at Trend Micro, speaking about the Microsoft raid, said: "If nothing else, this indictment serves as a graphic illustration of the maturity of the criminal business model."
© Copyright IBTimes 2025. All rights reserved.