Edward Snowden Interview Live: NSA Whistleblower Speaks at SXSW 2014
- Governments need watchdogs to provide "oversight" for Congress
- NSA is giving other countries a "green light" to collect data on citizens
- It's not wrong for large companies to collect data, but it's the length of time it's kept that's at issue
- Users should use TOR anonymity network to encrypt their data
17:01 Our live coverage ends here, thank you for reading.
16:58 SXSW: "A final question for you Edward, why did you decide to go public with your allegations?"
ES: "When I went public with this, it wasn't to try to change the government. What I wanted to do was to inform the public so that they could make a decision and consent to the surveillance. The result is that every society in the world has benefited with a more secure environment. Would I do it again? Yes. This is something we have a right to know and deserve to know. I took an oath to protect the country and the interpretation of the constitution had been changed in secret from 'No unreasonable search or seizure' to 'any search and seizure is fine' and that's something everyone should know about."
16:56 SXSW: "From Twitter, wasn't NSA mass surveillance a solution to the internet driven by contractors?"
ES: "The problem is that when the NSA gets a pot of money, they don't develop the solution for themselves - they bring in contractors. The problem is you've got contractors and private companies influencing policy. You've got people who aren't accountable, who are saying, 'Hey, let's do that, let's move money into public surveillance,' without asking if it's in the public's interest, and we need to make sure this doesn't go too far."
16:49
SXSW: "From Twitter, Isn't it just a matter of time before NSA can unencrypt any form of data?"
ES: "The US has investigated my dealings with journalists, and they still have no idea what documents they have or don't have, because encryption works. To encrypt the data so that no one can break it, the keys need to be protected so that they can't be stolen. The maths is sound and the data isn't going to be stolen. The US government actually supports that they know at this point, that neither the Russian or Chinese government have any access to this information, and the US government would know."
CS: "Ed is right. If the US government want to know what you do, they won't break your encryption, they'll hack into your devices and find vulnerabilities that haven't been patched. The goal here isn't to stop the NSA from going after criminals and terrorists - the goal is to stop the NSA from spying on innocent users. To make it too expensive for the NSA to spy on everyone, to raise the price of surveillance so that it no longer becomes economically viable to spy on everyone."
16:44 CS: "Cryptographers are all really pissed about the allegations that have come out about the NSA subverting security. Those people should be mad and they can make a difference. This is good, because the security tools that come out in the next six months will be far more secure than they are now."
SXSW: "A question from Twitter: Is there anything we can do to make sure are data is secure from the NSA?"
ES: "There are a couple of technologies. There's full disc encryption, then there's network encryption and then there's also TOR, a mixed-routing network that's encrypted from the user, through the IP to a network of clouds, so because of this, your ISP can no longer spy on you by default, when you go to any website. In order to spy on TOR, you'd have to try to hack into the TOR cloud or monitor exits from TOR, but that's really difficult for any sort of mass surveillance. You'll be much safer."
16.41: CS: "Tech companies need to win back trust, a lot of people are wary of trusting American companies with their data now."
SXSW: "A degree of hopelessness has descended in the international community about the NSA, GCHQ weakening encryption. Should people still be confident that the basic encryption we use protects us?"
ES: "Encryption does work. It's like the Defence Against the Dark Arts for the digital realm. We need to keep working on it and improving it. We need to have the moral commitment, the technical commitment and the philosophical commitement to improving encryption."
16:39 ES: "Throughout history we've seen governments repeat the trend. If we don't resolve these issues and allow the NSA to continue unrestrained, then other governments will see a green light to do the same."
16:36 SXSW: "A question from Twitter - why is it less bad for companies to have access to our data than governments?
ES: "They can jail you. Governments have the policing and intelligence powers to take away your rights. Companies can surveil you to sell you products, to sell your information to other companies and it's not great, but you have legal rights. If you challenge the government about these things, the government throws it out and says you can't even ask about it. The courts aren't even allowed to tell us if it's legal or not, we're just allowed to do it anyway.
16:35 CS: "If not for Edward Snowden's revelations, tech companies would not have improved their security processes. Many at home might think that what Edward Snowden did is wrong, but he is the reason why Yahoo users now have SSL encryption, why security is improving."
16:34 CS: "Many Americans are not happy with that data being stored about them. Even if they trust the person in the Oval Office, that person changes every few years."

SXSW: "The first question is from the founder of the internet Tim Berners-Lee - how would you change mass surveillance and what sort of programme would you put in place to improve privacy?"
ES: "We have an oversight model that could work. The problem is when we have congressmen who are shooting for the NSA rather than holding them into account...that's an incredibly dangeous things. The key fact is accountability. We can't have officials who can lie to the country, to the congress and face no criticism. In the US we have open courts that are expected to decide on important matters and secret courts that validate warrants, but that's not enough.
"We need public oversight...some way for trusted public figures to advocate for us. We need a watchdog that watches Congress, because if we're not informed, we can't consent to these (government) policies. Oversight has been overlooked for too long."
16:28 SXSW: "Do we need to be storing all this data?"
ES: "The reality is now that we've reached a point where a majority of US citizens' telephone communications and metadata is being stored, and we need to think about what are we getting out of it? We're monitoring everybody's communications instead of terrorists' communications. With several bombers, like the underwear bomber, we were warned using traditional methods about the bombers beforehand, but we didn't follow up on it. Instead we spent all this money on hacking Google to collect data, and what did we get out of it? Two White House investigations have proven this."
16:18 Christopher Soghoian, principal technologist of the American Civil Liberties Union: "Companies like Google are only interested to secure your connection from your computer to their servers, but how secure is the data? There need to be more rules about what data companies can store."
ES: "It's not that a large company cannot collect data. It's just that they shouldn't be keeping that data after they no longer need it. A company that was hacked had my driver's license from four years ago and it was posted to the internet. These things need to age off. Whether you're Google or Facebook, you can do things in a responsible way so that you can still gain value without storing it for longer than they need to.
16:16 SXSW: "Using secure communication encryption tools like PGP and Tor is really hard. Is there a call to arms to make this technology more easy to use?"
ES: "Absolutely. We want secure services that aren't opt-in. If a journalist gets an email from someone saying, 'Hey, I know something that the public would want to know about.', then the journalist needs to be able to securely access that. It has to be out there, it has to be open and easy to use."
16:11 SXSW: "How can we make mass surveillance more challenging and less viable?"
ES: "Encryption. There are two types of encryption - one type of encryption is the type we use for Google services. End-to-end encryption [however] is completely impossible to be cracked from your computer to the other computer without a codebreaker. End-to-end encryption would create a new type of law enforcement surveillance whereby they can only target specific communications and not just read everything users [are putting online]. We need to enforce end-to-end encryption in order to improve security."
16:05 Hugh Forrest, director of SXSW: "Why did you choose to speak to SXSW first?"
Edward Snowden: "SXSW and the technology community are the folks who can really fix our rights, even if Congress hasn't yet gotten to technical legislature.... in order to bring this legislature, there's a political response that needs to occur, but there's also a tech response that needs to occur. the NSA is setting fire to the future of the internet and the people in this room now, you're the fire fighters. We need you to fix this."
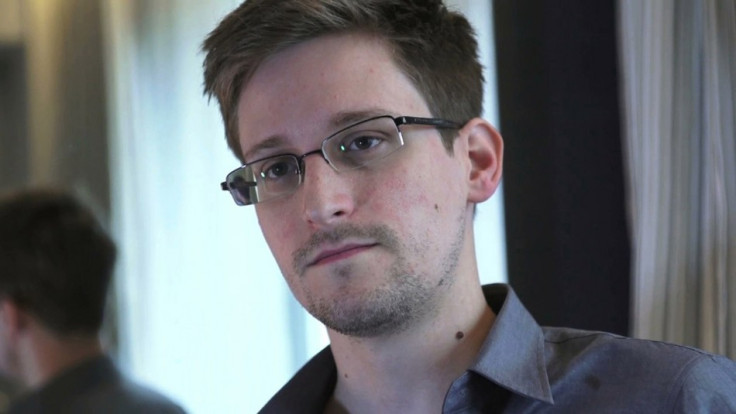
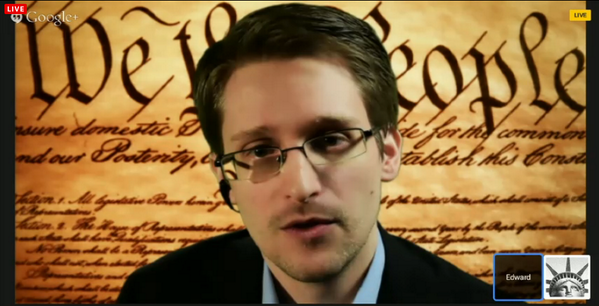
16:02 Snowden is appearing live for the virtual interview on Google Hangouts through seven proxies, in order to protect his location.
16:00 Welcome to our live coverage of the Edward Snowden interview session. You can submit questions to SXSW for Snowden to answer by tweeting using the hashtag #asksnowden.
Edward Snowden, a former security contractor turned whistleblower, who leaked over 20,000 top secret NSA documents to the media and is now living in exile in Russia, will be speaking to the SXSW 2014 conference live today about the global impact of the allegations so far and his experiences since the furore began.
© Copyright IBTimes 2025. All rights reserved.





















