This Android malware can empty your bank account – and it was found on Google Play
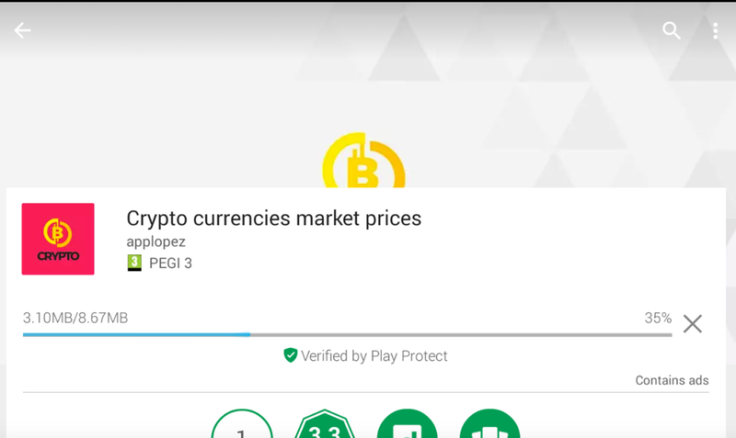
The app - "Cryptocurrencies Market Prices" - had more than 1,000 downloads.

A notorious banking Trojan that can mirror legitimate applications in order to steal passwords was recently discovered on Google's official marketplace posing as a cryptocurrency service.
The software was lurking on the Play Store posing as "Cryptocurrencies Market Prices" and, before being removed by Google, had been downloaded more than 1,000 times. Security firm RiskIQ first detected the Trojan – called BankBot – on 18 October. It was gone seven days later.
The BankBot malware, which has plagued Android devices for months, uses an "overlay technique" in an attempt to fool unsuspecting victims into entering their details into an app they believe is legitimate.
"The instance of BankBot was distributed using social engineering," RiskIQ said Thursday (8 November).
"A user manually downloads and installs the fully functional app on their Android device to compare cryptocurrency market prices with fiat currency values.
"Once installed, the user is presented with an app that can perform cryptocurrency exchange monitoring."
"However, BankBot is using this seemingly legitimate application to mask its actual purpose. By giving the victim an app that works, the user may be less suspicious of [its] nefarious nature."
Once downloaded, the malware sits silently on a device and checks for any of the financial apps it can pose as. If one of the desired financial applications is launched, BankBot will overlay a screen that looks identical to the legitimate service – and scoop up any entered passwords.
In this case, experts said the Trojan asked for a number of suspicious permissions upon installation.
These included the ability to read text messages and access the internet. If the hackers could read the victim's texts, RiskIQ said, they could also intercept two-factor authentication codes.
This variant of BankBot appeared to be targeting users of Polish banks. It remains unclear if the culprits – whose identities remain unknown – were successful in raiding any accounts.
Risk IQ said the discovery "serves as a reminder of the sophistication of malicious mobile apps" and that users should be vigilant in evaluating all apps before downloading, even from trusted stores.
BankBot, which is primary designed to target Android smartphones, had its source code leaked online in January this year – and has since developed into a major cybercrime threat.
Experts previously said that some variants have the ability to mimic "hundreds" of real services.