Tor Phone: Privacy activists developing super private and secure version of Android
Tor Project launching new version of Tor-enabled Android phone prototype dedicated to security and privacy.
The Tor Project is currently developing a prototype of a Tor-enabled phone that tries to improve Google's Android mobile operating system by focusing exclusively on security and privacy, due to grave concerns that Google and smartphone manufacturers that rebrand Android are not taking security threats seriously enough.
"The Android ecosystem is moving very fast, and in this rapid development, we are concerned that the freedom of users to use, study, share, and improve the operating system software on their phones is being threatened. If we lose these freedoms on mobile, we may never get them back. This is especially troubling as mobile access to the Internet becomes the primary form of Internet usage worldwide," Tor developer Mike Perry wrote in a recent blog post.
"We are trying to demonstrate that it is possible to build a phone that respects user choice and freedom, vastly reduces vulnerability surface, and sets a direction for the ecosystem with respect to how to meet the needs of high-security users."
How the Tor Phone works
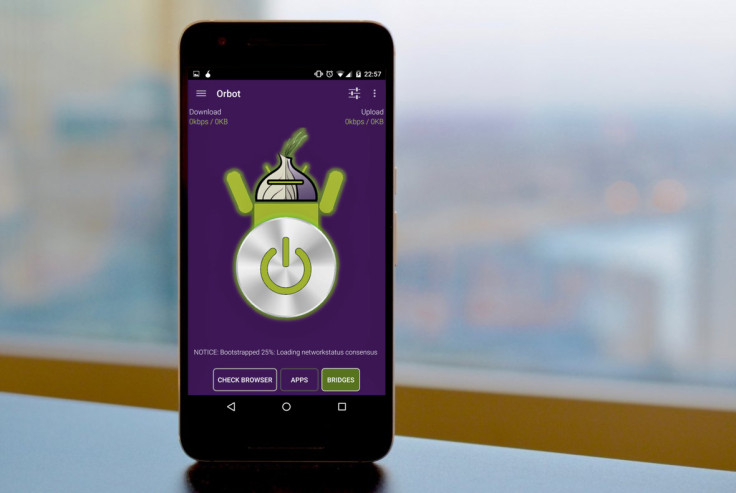
The Tor Phone is based on Copperhead OS, which is an Android distribution that includes numerous security enhancements in order to fix the many vulnerabilities in Android, and Tor's developers have also added an app called orWall that forces all apps to route their traffic over the Tor anonymity project through an Android firewall called Orbot, while blocking unwanted traffic.
orWall brings full control of how your smartphone uses the internet back to the user, who needs to choose which apps should have their traffic encrypted by Tor and which don't need it. The app also lets voice over IP (VoIP) call apps bypass Tor to send voice data, but still ensure that locations and personal data of the parties on the call remain anonymised through Tor.
Of course, you could always argue that you don't need the Tor Phone if you're already using a virtual private network (VPN) on your Android phone, but Perry points out that Android's VPN APIs are not that secure and can still leak data at boot, and this problem affects Orbot too. But if you put orWall on top of it and root the traffic through Tor, then the traffic definitely can't be seen by prying eyes.
Is Android still open source?
The Tor Project is concerned that Android is now becoming an operating system that isn't really fully open source and that Google is "surreptitiously" locking down Android in order to prevent security vulnerabilities from weakening the platform and affecting users, which defeats the original purpose of Android, which was to enable end users to actively study, improve and share ideas to make the operating system better for everyone.
"We believe that more transparent development and release processes, along with deals for longer device firmware support from SoC vendors, would go a long way to ensuring that it is easier for good OEM players to stay up to date. Simply moving more components to Google Play, even though it will keep those components up to date, does not solve the systemic problem that there are still no OEM incentives to update the base system," Perry stressed.
"Users of old AOSP base systems will always be vulnerable to library, daemon, and operating system issues. Simply giving them slightly more up to date apps is a band aid that both reduces freedom and does not solve the root security problems."
Google should force OEMs to take security seriously
The Tor Phone prototype currently works on the 2015 Google Nexus 6P smartphone, and users can download it onto their smartphones now, but they will need a basic understanding of Linux to get it set up. The developers plan to add support for Pixel soon and are only looking at Nexus and Pixel phones for now as these are the only devices that currently support Verified Boot and user-controlled keys.
Verified Boot is a file security system that uses cryptographic integrity checking to verify that the device's system partition is protected and unchanged by using a public key to verify the signature of the hash, so that malware with root privileges cannot hide itself on the device and make changes to files in order to avoid being caught by malware detection programmes.
"If Google Play is to be used as a source of leverage to solve this problem, a far better approach would be to use it as a pressure point to mandate that OEMs keep their base system updated. If they fail to do so, their users will begin to lose Google Play functionality, with proper warning that notifies them that their vendor is not honoring their support agreement," wrote Perry.
"Google should be competing on overall Google account integration experience, security, app selection, and media store features. They should use their competitive position to encourage/enforce good OEM behaviour, not to create barriers and band aids that end up enabling yet more fragmentation due to out of date (and insecure) devices."
IBTimes UK has contacted Google to ask for a response to the Tor Project's comments on Android and Google's role in securing it.
© Copyright IBTimes 2025. All rights reserved.






















