Crisis Malware to Cause Low Risk for Virtual Machines, Threat Seen in Future
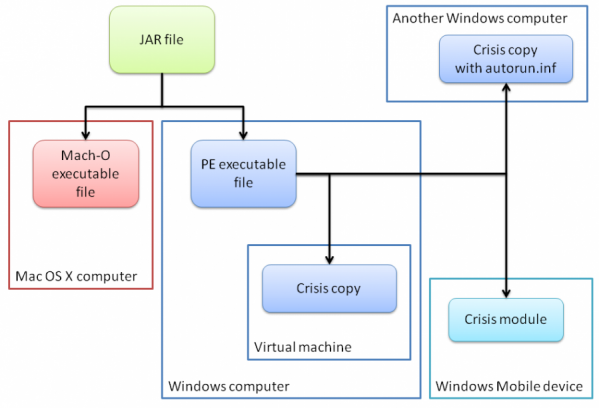
Crisis malware aka Morcut was discovered in July and was found to infect four platforms - Mac OS X, Windows, VMware virtual machines and Windows mobile smartphones - rather that the two previously discovered. eWeek has reported that the malware has been found to cause "no real danger for virtual machines", while it does presage a possible move by criminals towards finding better methods to infect virtualised servers and infrastructure, according to security experts.
"You don't have to go looking for Crisis on your data centre VMs, because it's not really targeted at that," Warren Wu, director of the data centre business unit at security software firm Trend Micro, said in an interview, according to reports.
"But a future malware author could have an 'Aha!' moment and decide to use the same technique to get access to the VMs in the data center," Wu adds.
TrendMicro, a cloud security blog, notes that the VMware virtual machines are no stranger to malware infections. Firstly, Crisis malware checks for the virtual machines and infects them. Second, it will infect the machine via underlying infrastructure by modifying the .vmdk file.
"All the interesting aspects aside, we do not feel that there is an immediate threat from this malware. The actual rate of incidence in the wild is very low (less than 100), so it does not appear to be widespread or capable of spreading quickly," explains TrendMicro.
The site claims there are two types of hypervisor deployments such as Type 1 and Type 2. In regard to Type 1 Hypervisor deployment, Wu claims that it is not the deployment Crisis malware that attacks. In Type 2 case, the hypervisor will run on top of the operating system and in turn hosts several virtual machines. Wu claims that the majority of virtual machines are Type 1 that run on data centre where an intermediate operating system is not required.
"Crisis infects virtual machines like macro viruses infected Word documents," Wu said, according to eWeek. "To protect against that, companies should make sure that they restrict acces to their repositories of virtual machines."
© Copyright IBTimes 2025. All rights reserved.





















