Chinese Government Hacking Report used as Bait in new Cyber Attack
A high-profile report into a sophisticated and organised group of Chinese hackers linked to the Chinese government is being used as bait in a new targeted cyber-crime attack.

Earlier this week security experts Mandiant published a report which revealed a sophisticed Chinese hacker group, embedded deep within the Communist Party of China and linked to its military wing, had been infiltrating a huge number of organisations around the globe stealing masses of sensitive data.
The report, APT1: Exposing One of Chin's Cyber Espionage Units, details Mandiat's work in tracking the group for the past seven years and monitoring their attacks on 141 organisation around the globe, with the vast majority based in the US.
However, just days after the report was published, it has been discovered that other cyber-criminals are using its publication as bait in an attempt to infect the computers of those who might be interested in reading it.
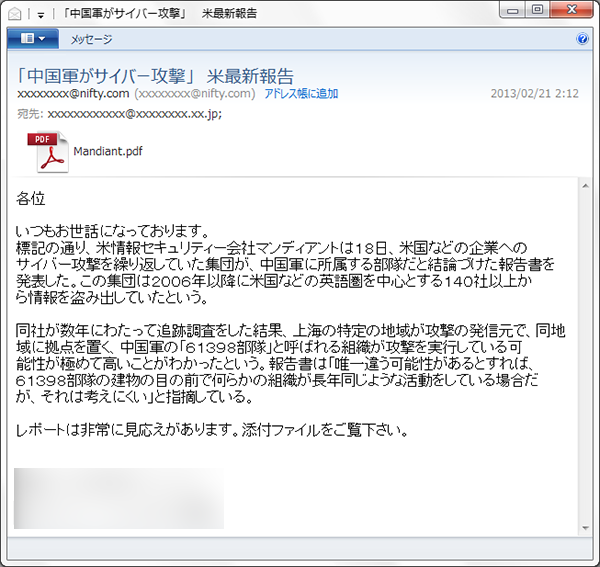
Security firm Symantec has discovered emails being circulated which have a fake copy of the report attached to them. While the sample Symantec has come across are written in Japanese, there could easily be other emails in other languages spreading across the internet.
The email arrives with an attachment called Mandiat.pdf which, when opened, displays a blank PDF document. In the background however, a piece of exploit code taking advantage of vulnerabilities in Adobe Reader and Adobe Acrobat is silently executed.
Symantec has identified a number of pieces of malware which the fake PDF document may drop onto your PC if the vulnerability is successfully exploited.
Source
While the email purports to come from someone in the media, like in many targeted attacks, it is actually sent from a free email account and the content of the email uses subpar language. "It is obvious to a typical Japanese person reading the email that it was not written by a native speaker," Joji Hmaada said on Symantec's blog.
This is not the first time this tactic has been used. Back in 2011, when Symantec released a whitepaper on another group performing targeted attacks, the attackers took the opportunity to use the publication to infect those interested in reading the paper. They did this by spamming targets with the actual whitepaper along with malware hidden in an archive attachment.
What this shows is that cyber-criminals are no longer sticking to the same old ruses in order to trick people into downloading malware. They are using up-to-the-minute news and reports in order to trick targets into downloading what appears to be relevant and important documents.
Targeted attacks are much harder for traditional anti-virus security solutions to defend against, as they use a combination of social engineering and subterfuge to pypass whatever security measures are in place.
Mandiant
The Mandiant report in particular is of huge interest to the security world at the moment, detailing how sophisticated and well-funded cyber-crime has been used to gain access to some highly sensitive data from some of the world's biggest companies.
The group, dubbed Active Persistent Threat 1 (APT1) by Mandiant, is "one of the most prolific cyber espionage groups in terms of the sheer quantity of information stolen" and it has stolen "hundreds of terabytes of data" over the past seven years.
With a very high degree of certainty, Mandiant was able to link APT1 to the People's Liberation Army's (PLA's) Unit 61398 which is based in a non-descript 12-storey white building in the Pudong New Area of Shanghai.
Mandiant's report has forced the issue into public view and in response US President Barack Obama this week has singled out China and Russia as "aggressive" players in the cyber-espionage world, warning they will continue to try and steal US industrial and technological secrets.
In a report outlining plans to deal with the theft of American trade secrets, published in the wake of Mandiant's report, the US government said:
"We judge that the governments of China and Russia will remain aggressive and capable collectors of sensitive US economic information and technologies, particularly in cyberspace."
Denial
China continues to deny being involved in cyber-espionage or cyber-theft with the Chinese defence minister calling the Mandiant report deeply flawed. And he is not the only one, as security expert Jeffrey Carr says the report has "critical analytic flaws" because Mandiant "refuses to acknowledge that other nation states engage in cyber espionage."
Carr goes on to suggest some critical analysis which could be carried out on the report to verify its findings, adding:
"My problem with this report is not that I don't believe that China engages in massive amounts of cyber espionage. I know that they do. My problem is that Mandiant refuses to consider what everyone that I know in the Intelligence Community acknowledges - that there are multiple states engaging in this activity; not just China."
© Copyright IBTimes 2025. All rights reserved.






















