Tilon Financial Malware Targets UK and European Banks
A piece of financial malware called Tilon is targeting European banks and uses "a full bag of tricks" to avoid anti-virus detection.
Tilon affects browsers such as Microsoft Internet Explorer, Mozilla Firefox, Google Chrome "and probably others" said security firm Trusteer, which discovered the malware.
Only four out of 41 anti-virus engines detected the malware installation but even those that did logged it as a "fake system tool" instead of financial malware.
Tilon is an updated version of the Silon malware, which appeared in 2009 and defrauded online banking customers who were supposed to be protected by two-factor authentication.
The 'Man in the Browser' (MitB) style malware targets a number of banks, although a full list has not yet been published.
"Quite a few European banks are being targeted. It won't be published which ones until they have been informed otherwise the criminals go in and do a quick grab," Trusteer's Neil Stinchcombe told IBTimes UK.
Tilon is a piece of software that injects itself into your web browser and then fully controls the traffic running to and from that browser.
It creates a log of all the information entered into online forms and sends those details it back to a central server, in a process is known as "form grabbing." Tilon also controls the web pages a user sees and targets specific URLs by replacing parts of those pages with its own text.
Stinchcombe said that the most impressive thing about Tilon is the breadth of evasion techniques it employs to avoid detection and scrutiny and to survive attempted purges by security products.
Avoiding Anti-virus
Some of the evasion techniques Trusteer lists include:
- Tilon will not install properly on a virtual machine.
- The malware installs as a service with a genuine-looking name and with a random executable name.
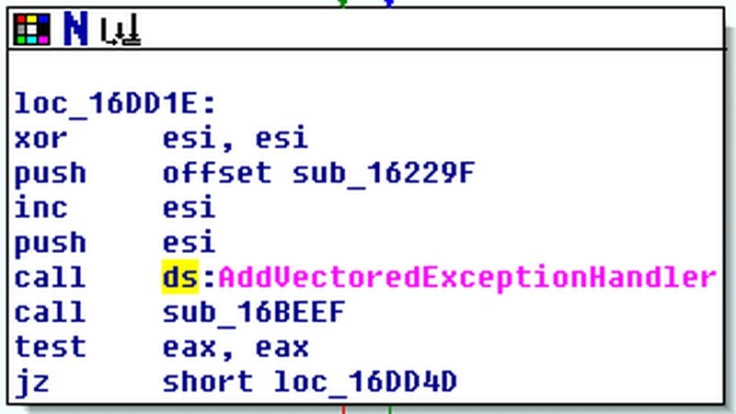
- Inside one of the Windows native processes, Tilon starts a watchdog thread that monitors its service entry in the registry and its executable file on disk. If these are tampered with, Tilon restores them within three seconds. This mechanism resists removal by many security products.
- Tilon has a very peculiar way of hooking browser functions, which is the standard implementation for form grabbing and HTML injection. Most malware families replace the first five bytes of the functions they hook with "JMP stub", where "stub" is the malware code that implements the hook logic. Tilon takes an unorthodox approach that is likely to evade security products looking for traditional hooking techniques on browser functions.
- Tilon mutates. Trusteer discovered Tilon in July 2012 and it has already mutated once - around the end of July / early August. The mutation changed how random file names are generated.
Stinchcombe said that Trusteer had wondered whether the people behind Silon were taking a long vacation in prison, as the malware had begun to decline.
"Alas, not so. In July 2012, Trusteer discovered a new financial malware, which upon close investigation, contained some behaviours identical to those exhibited by Silon," he said.
Stinchcombe said Trusteer's Pinpoint product detects Tilon, while Trusteer Rapport prevents its installation, detects its presence in the browser and removes it from already infected machines.
© Copyright IBTimes 2025. All rights reserved.




















