What is the World's Most Hackable Car?
Ford, Range Rover, Audi and BMW all among top 10 most hackable cars

It's not a question most people ask when they are thinking about buying a new car, but as our vehicles become ever more connected and more dependant on computers, car salesmen will soon be asked by many people: How hackable is this car?
In the first list of its kind, security experts Charlie Miller and Chris Valasek revealed the findings of research they carried out into which makes and models are the most hackable.
According to the researchers - who work at Twitter and IOActive respectively - the most hackable cars on the market at the moment are the 2014 model of the Infiniti Q50 from Nissan, the 2014 Jeep Cherokee and the 2015 model of the Cadillac Escalade.
On the other side of the coin, the researchers said that of the cars they looked at, the 2014 Dodge Viper, the 2014 Audi A8 and the 2014 Honda Accord were the "least hackable" models.
The pair looked at each car under three categories - attack surface, network architecture and cyber physical - to assess how vulnerable each model was.
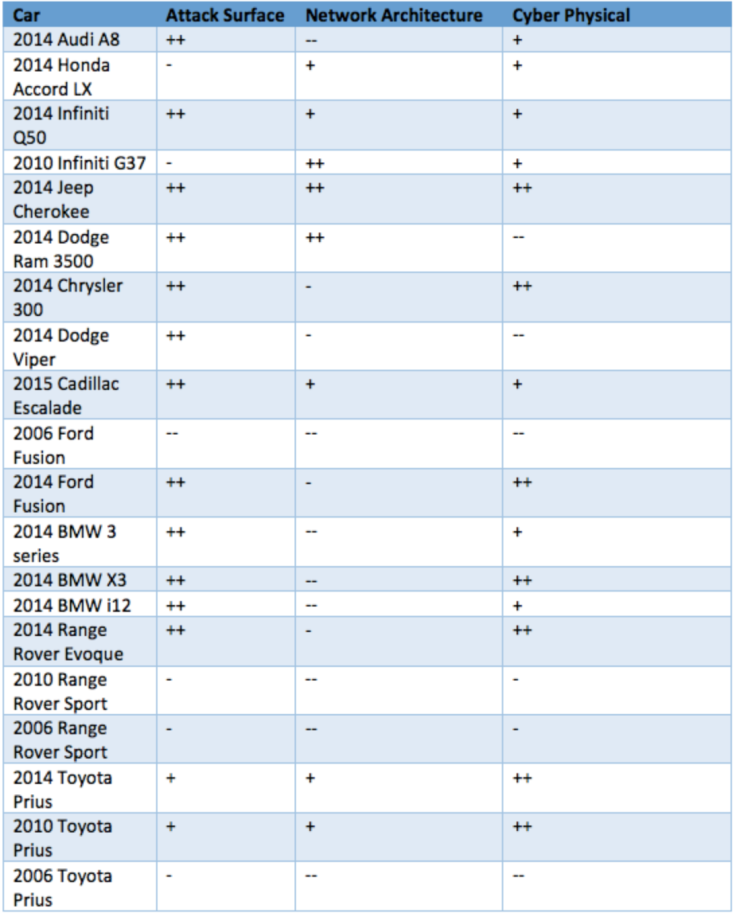
The attack surface relates to the variety of wireless connections (including Bluetooth, wi-fi and network connections) through which an attack could be carried out.
The network architecture includes how much access these features give to the vehicle's critical systems, such as the steering and brakes.
Cyber physical relates to capabilities such as automated braking and parking sensors that could be controlled using wireless commands.
Weaknesses
While the researchers pointed out that their research doesn't show definitive security threats, it does give an indication of weaknesses in these cars:
"Automotive security concerns have gone from the fringe to the mainstream with security researchers showing the susceptibility of the modern vehicle to local and remote attacks," said Valasek and Miller in their 92-page report entitled A Survey of Remote Automotive Attack Surfaces.
"A malicious attacker leveraging a remote vulnerability could do anything from enabling a microphone for eavesdropping to turning the steering wheel to disabling the brakes."
Opportunistic
Miller and Valasek last year demonstrated how a Toyota Prius could be hacked and the steering wheel remotely controlled by the attacker, even while the victim was driving.
While the thoughts of someone hacking your car and taking control of your steering wheel are obviously scary, Miller and Valasek were eager to point out that the risk of such an attack happening at the moment is very low.
"This is really an opportunistic attack., It takes a lot of time, effort, dedication, and money to figure out how to perform one of these attacks and to succeed doing it. Joe Consumer doesn't have to worry, but if you're a high-profile person with a lot of technology in your vehicle, it's something to consider," Valasek said during his presentation at the Black Hat hacker conference in Las Vegas last week.
Safety rating
While Miller and Valasek were highlighting the growing problem of cyber-threats to motorists, a couple of days later at the DefCon hacking convention, a security advocacy group called I Am The Cavalry proposed a framework for rating cars for cyber-security.
The Five Star Automotive Cyber Safety Program aims to standardise the rating of a car's cyber-defences and calls on the automotive industry to "acknowledge that vehicle safety issues can be caused by cyber-security issues" and "embrace security researchers as willing allies to preserve safety and trust."
The Program's five points would be:
- Safety by Design
- Third Part Collaboration
- Evidence Capture
- Security Updates
- Segmentation and Isolation
The group has already unveiled the first five-star rated car under the proposed new system, with Tesla's Model S achieving full marks for cyber-safety - despite Chinese hackers last year claiming they had hacked the car (though this was never demonstrated publicly).
© Copyright IBTimes 2025. All rights reserved.






















