The Dangers Lurking In Your Inbox [BLOG]
Scott Greaux from PhishMe talks about the risks lurking in your inbox and gives his tips on how to avoid phishing attacks.
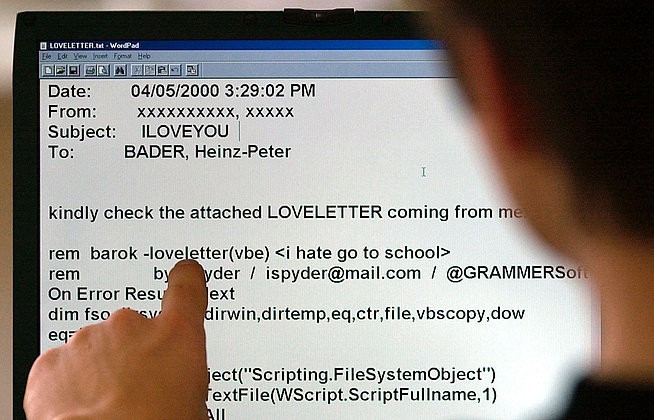
Phishing has changed. Instead of mass mailings targeting thousands or even millions of recipients, spear phishers have adopted a targeted marketing approach, developing emails that are well-crafted and researched, and much more likely to get through the IT security controls and land in a recipient's inbox.
Once they are through the traditional IT security controls, spear phishes are designed to appeal to emotions luring recipients through a sense of fear, curiosity or reward. Addressing recipients on an emotional level provides the best possible chance of soliciting a response and having the recipient follow a link or open an attachment.
Since your users may act as the last line of defence, education is essential. Email users need to be informed about what indicators signal that there may be danger lurking behind an email.
One of the easiest to spot is the sender name. An email may appear to be from a work colleague, but taking a moment to inspect the email address could show you that it was actually sent from a Gmail account. This should act as a signal to users to stop and think. Likewise, if the email isn't something you would expect that person to send you or if it simply doesn't "feel" right you should report it.
Content is another key indicator as to whether or not something is genuine. Don't fall for an attachment marked '2013 salary reviews' because you are feeling nosy. Likewise, does something sound too good to be true? Then it probably is.
For example, if you haven't ordered something online that you should be wary of delivery notifications urging you to open attachments or follow a URL (one of the most prevalent types of phishing email at the moment). The final warning of something suspicious is grammar; poorly written emails should raise suspicion.
The power to defeat a spear phishing attack is distributed throughout the workforce. So how do you make sure that that all users are up to speed? There are a few steps you can take.
1. Train your users
This doesn't mean making them sit through an online course for an hour when they start, and then repeating it once a year. Engage them in a way that is designed to truly change behaviour. Immerse users in an educational experience designed to measure behaviour and deliver targeted, bite-sized education.
2. Send mock phishing emails to your employees
See what they do. If they click on the link, open the attachment or provide personal data, then provide immediate feedback in the form of training. Repeat the exercise every few months using different emotional 'tricks' that the criminals would use. Over time, your users will become much more likely to dodge an attack.
3. Remind users of risks
Remind your users about the risks that can hide under links or in attachments, and encourage them to think twice before clicking or opening them. If they aren't sure that an email is genuine then it is best to check using a different communication channel, such as phone or face-to-face to ask the sender if it has come from them.
If users do receive a malicious email, they need to know what to do with it. For example, should they just delete it? Or should they report it to a person or team within your organisation to investigate and determine if it is legitimate?
Reporting attacks allows information security teams to share select details about spear phishing attempts throughout the organization, so everyone knows what to look out for.
Users are the last line of defence against spear phishers, and armed with the right education and awareness programmes, they can ensure that you all stand the best possible chance of thwarting any attack.
Scott Greaux is the Vice President of product management and services at online security company PhishMe.
© Copyright IBTimes 2025. All rights reserved.




















