Cybercriminals Use Text Messages to Empty ATM Cash

Cybercriminals are able to withdraw cash from ATMs "across the world" by simply texting an SMS message to a compromised cash machine, according to a new report.
The discovery was made by security firm Symantec which warns that such attacks are likely to become even more prevalent as support for Windows XP - run on 95% of ATMs worldwide - ends next month.
Symantec has previously reported on a type of malware known as Ploutus used by cybercriminals to access ATMs using an external keyboard.
The latest attacks stem from a variant of this malware identified as Backdoor.Ploutus.B. Once an ATM is infected by this type of Ploutus, cyber criminals are able to simply send a text message to the machine and it will dispense cash.
According to the report, this technique is being used in "a number of places across the world at this time", though Symantec has informed IBTimes UK the majority of infections are currently in South America. Exact numbers are yet to be confirmed.
Fast and convenient
In order to pull off the cyberattack, criminals first need to gain remote control access to an ATM by connecting a mobile phone to the inside of an ATM. This can apparently be achieved multiple ways, though a technique known as 'USB tethering' is commonly used. It creates a shared Internet connection between the phone and the ATM.
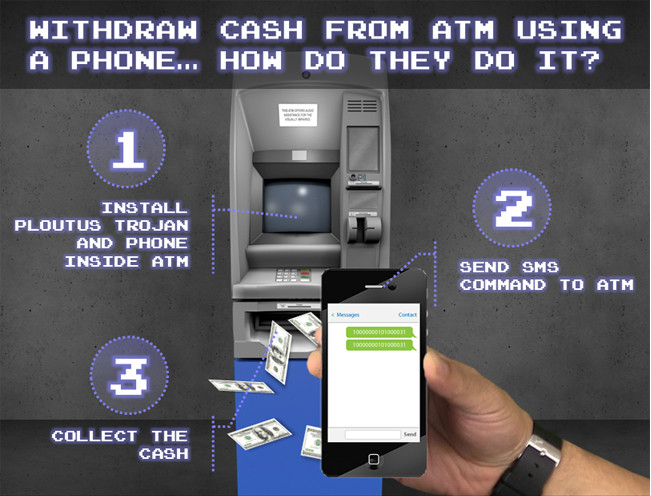
"After the mobile phone is connected to the ATM and set up is completed, the criminals can send specific SMS command messages to the phone attached inside the ATM," said Daniel Regalado, a malware analyst at Symantec.
"When the phone detects a new message under the required format, the mobile device will convert the message into a network packet and will forward it to the ATM through the USB cable."
Regalado believes using SMS messages to control the ATM is the most convenient method for cybercriminals to control an infected machine.
"The master criminal and money mule can synchronise their actions so that the money is issued just as the money mule pretends to withdraw cash or is walking past the ATM," Regalado said.
© Copyright IBTimes 2025. All rights reserved.




















