Grum Botnet Bigger and More Complex Than Suspected
The spam botnet known as Grum which was shut down last month contained email addresses for one third of the world's population.
When the monster spam botnet called Grum was taken offline last month, it was suspected that the botnet consisted of more than 20,000 infected PCs around the globe. A month later, following some research, it has been discovered the real figure was closer to 200,000.
A botnet is a group of computers infected by a virus which allows criminals to control the PCs remotely, and send out billions of spam emails using command and control (C&C) servers which 'talk' to the infected PCs. Grum's C&C servers were mainly located in Ukraine, Russia and Panama.
Grum was shut down by security company FireEye and spam-monitoring service SpamHaus, working in conjunction with local internet service providers (ISPs). Now, one of those ISPs has revealed that the scope and capabilities of Grum were much larger and more complex than many experts had suspected.
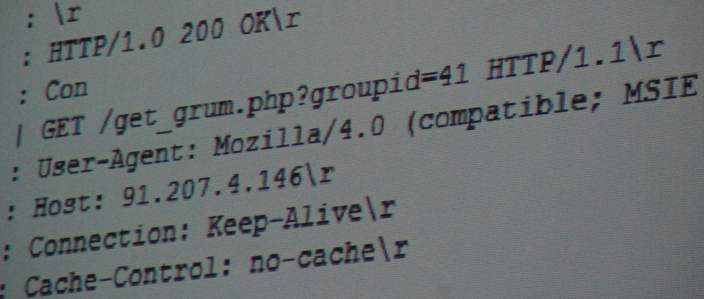
Security blogger Brian Krebs, a former Washington Post reporter, was given access to a copy of a web server installation that was used as one of the C&C servers for the Grum botnet.
"According to the database maintained on this Grum control server prior to its disconnection in mid-July, more than 193,000 systems were infected with one of three versions of the Grum code, malware that turned host systems into spam-spewing zombies," Kreb said on his blog.
At its high-point earlier this year, Grum was spewing out one third of all the world's spam email, and was capable of sending out 18 billion emails every single day.
Spew out
Grum was able to spew out so much spam because it had built up massive email address lists, totalling more than 350GB in size in all. Kreb said there were dozens of separate email lists on the server he had access to, each containing between 20 million and 60 million email addresses.
Kreb was unable to assess how many of these were unique or active email addresses, but "a quick tally of 60 different address list files found in one directory on the server showed that they contained more than 2.3 billion addresses."
Grum's main use was to send out ads for rogue, fly-by-night pharmacies. Customer information for more than 1.3 million orders placed at these internet pharmacies between 2006 and 2010 was discovered on the server.
This information included order numbers, dates, the type of drug purchased, strength, quantity, price, customer country, and email address, among other information.
While spam was the primary purpose of the Grum botnet, there is also a suggestion that it would have been used to distribute malware. "There are indications that the botnet was at some point in 2011 used to distribute malware disguised as a DHL shipping notification."
Hints at the identity of the person cbehind the grum botnet were also found. A decrtpyerd password used to administer the botnet's web-based interface was found to be "megerasss". The name Gera appears in this password, a nickname previously identified as the person behind the botnet.
© Copyright IBTimes 2025. All rights reserved.






















