Hammertoss: Putin-backed hackers are using Twitter to control an army of malware-infected PCs
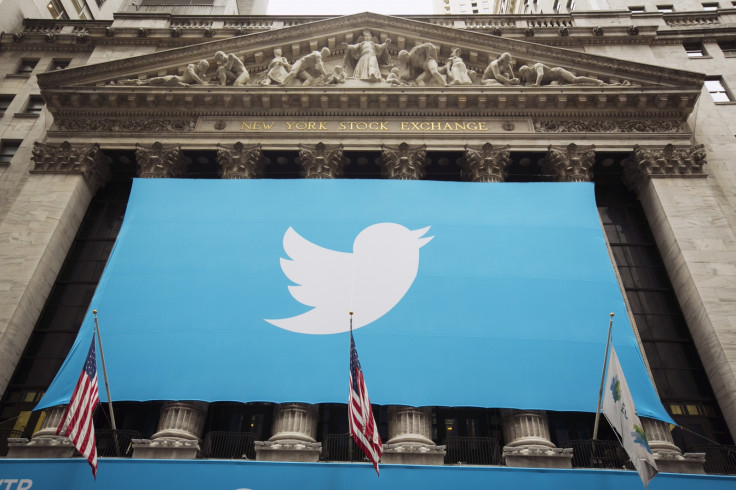
A group of hackers known as APT29 – thought to be backed by the Russian government – are using an innovative method of controlling its army of PCs infected with malware, known as Hammertoss. They use Twitter and messages hidden within seemingly benign images.
The group's actions were uncovered by security company FireEye in early 2015 when it was investigating the systems of an unnamed customer. FireEye says APT29 was using its innovative techniques to infiltrate government organisations to target geopolitical information related to Russia, which points to a link to the Kremlin.
The malware has been used to infect systems since at least late 2014. The group has shown a high level of sophistication by continually deploying updates to the malware as well as monitoring the defensive activities of its victims to avoid detection.
The group's most sophisticated trick to avoid detection is in the way it communicates with the infected machines using Twitter as a command-and-control server. Here's how it works:
- Once a system has been infected with HammerToss, it is programmed to generate new Twitter handles in a very specific way, on a daily basis
- Once generated it searches Twitter for this specific address
- If it doesn't find the address, it repeats the process daily
- If the hacker wants to send a particular command to the infected machine, they create the predetermined Twitter handle and post a message containing a hashtag and a URL
- The URL leads the infected machine to an image stored on another server which has been embedded with encrypted data using stenography, a method for concealing hidden data in an image or file
- The hashtag contains the image's file size and a few characters which are added to a decryption key stored within Hammertoss in that allows the malware to read the content
With most companies unlikely to be blocking outbound traffic to Twitter's servers, the hackers can remain under the radar as anyone who even noticed the link to Twitter would only find what looked like a benign image. This system would allow the hackers to remain on the infected systems, search for relevant files repeatedly and exfiltrate the files they were after to a server under their control.
FireEye last October published a report into another Russian government-backed hacking group known as APT28, which was accused of attacking high-profile targets in the US, as well as Nato and Eastern European governments. FireEye said at the time the report was published that it showed "evidence of long-standing, focused operations that indicate a government sponsor – specifically, a government based in Moscow".
It is unclear how closely APT29 and APT28 are linked. Similarly, it is unknown if they are targeting the same victims.
© Copyright IBTimes 2025. All rights reserved.




















