Apple, Google and NASA Employees Compromised as IEEE Exposes 100,000 Passwords
Despite claiming to advance technical innovation and standards, members of the Institute of Electrical and Electronics Engineers (IEEE) will want to change their passwords, as 100,000 of them written in plain text have been exposed.

Researcher Radu Dragusin claims to have discovered the massive data breach - which accounts for around a quarter of all IEEE members and has been visible for over a month - on an FTP server owned by the institute.
"The usernames and passwords kept in plaintext were publicly available on their FTP server for at least one month prior to my discovery," Dragusin, who works in the Department of Computer Science at the University of Copenhagen as a teaching assistant, said.
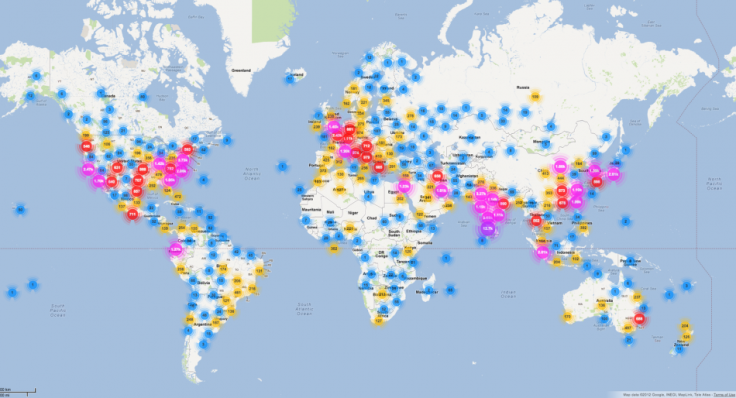
"Among the almost 100,000 compromised users are Apple, Google, IBM, Oracle and Samsung employees, as well as researchers from NASA, Stanford, and many other places," he added.
It is not known yet if anyone besides Dragusin accesses the data, however with the information being freely available for more than a month it is a very real possibility.
Dragusin said that IEEE may have access logs for the FTP server in question which may be able to identify if there has been another data leak. We have tried to contact IEEE, but at the time of publication we have not gotten a response.
Website
Dragusin created the ieeelog.com website where he explained that he came across the data breach on 18 September and told IEEE about the problem six days later. The researcher adds that he has not and will not make the data available to anyone else.
Of the 100,000 usernames and passwords exposed, it was found that "123456" was the most commonly used password, followed by "ieee2012" and "12345678".
"Password" was the fifth most commonly used password and even "123" made it into the top ten, highlighting how insecure and obvious many of the passwords were.
Brian Spector, CEO of online security experts CertiVox, said in a statement sent to IBTimes UK: "What is breathtaking here is that username and password data stored on websites has repeatedly been the subject of recent high-profile breaches, regardless of whether it was kept in the clear or not.
Prime target for hackers
"Yet even erudite organisations like the IEEE seem to think that storing the user login data on the website in some way is still acceptable practice. Let's be clear, it's not - it simply makes the site a prime target for hackers. With the two-factor authentication technology that is available today, there is no further excuse for websites to store user login data in any way."
Dragusin agrees: "Keeping a salted cryptographic hash of the password is considered best practice, since it would mitigate exactly such an access permission mistake," adding that keeping passwords in logs that can be accessed by any employee is "inherently insecure."
In his breakdown of what IEEE has done wrong, Dragusin said: "By the nature of the organization, IEEE members are highly specialised individuals, many of them working in critical industry, governmental and military projects.
"Furthermore, it would be reasonable to assume, that an organization publishing leading security-focused publications, would value the privacy of its members, and be proactive in keeping their data secure.
"The simplest and most important mistake on the part of the IEEE web administrators was that they failed to restrict access to their webserver logs for both ieee.org and spectrum.ieee.org allowing these to be viewed by anyone going to the address ftp://ftp.ieee.org/uploads/akamai/ [which has since been closed]."
© Copyright IBTimes 2025. All rights reserved.





















