Sathurbot trojan targets WordPress sites using illegal movie and software torrents
Sathurbot has been active since at least June 2016 and has compromised over 20,000 computers so far.

Security researchers have uncovered a new ecosystem for a malicious backdoor trojan that uses torrents as a delivery medium to target weak WordPress accounts. The trojan, dubbed Sathurbot, has been active since at least June 2016 and has infected over 20,000 computers so far.
According to ESET researchers, Sathurbot comes disguised as a torrent with an apparent installer executable and a small text file. The backdoor trojan preys on users looking to download a free movie or software torrent and entices them into running the executable and loading the Sathurbot DLL.
"It just might happen that your favourite search engine returns links to torrents on sites that normally have nothing to do with file sharing," researchers explained in a blog post. "They may, however, run WordPress and have simply been compromised."
The researchers found multiple movie subpages that lead to the same torrent file while the software subpages lead to a separate one.
"When you begin torrenting in your favourite torrent client, you will find the file is well-seeded and thus appears legitimate," the researchers said. "If you download the movie torrent, its content will be a file with a video extension accompanied by an apparent codec pack installer, and an explanatory text file. The software torrent contains an apparent installer executable and a small text file."
Once a victim runs the executable, the Sathurbot DLL loads and displays an error message that says the installer has failed due to an incomplete download or damaged media.
"While you ponder your options, bad things start to happen in the background. You have just become a bot in the Sathurbot network," the researchers warn. "The Sathurbot then reports its successful installation along with a listening port to the C&C. Periodically, it reports to the C&C that it is alive and well, waiting for additional tasks."
The trojan can update itself as well as download and start other executables for malware, including Boaxxe, Kovter and Fleercivet, while waiting for additional tasks.
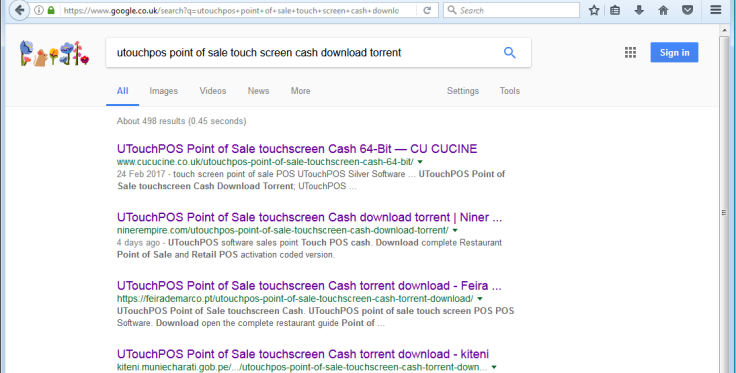
The researchers said Sathurbot comes with around 5,000+ basic generic words that are randomly combined to form a 2-4 word phrase combination used as a query string for search engines such as Google, Bing and Yandex.
"From the webpages at each of those search result URLs, a random 2-4 word long text chunk is selected and used for the next round of search queries," the researchers said. "Finally, the second set of search results (up to first three pages) are harvested for domain names."
ESET said Sathurbot is currently harvesting domain names that have WordPress sites but is also interested in Drupal, Joomla, PHP-NUKE, phpFox and DedeCMS.
Once the harvested domains are identified and sent to the C&C, Sathurbot probes for domain access credentials and passwords.
"Different bots in Sathurbot's botnet try different login credentials for the same site. Every bot only attempts a single login per site and moves on," he said. "This design helps ensure that the bot doesn't get its IP address blacklisted from any targeted site and can revisit it in the future."
Besides search engines, the malicious torrent links have also been sent via email to compromise as many sites and users as possible. ESET's analysis found the botnet now consists of over 20,000 infected computers.
The security firm recommends that web administrators check for any unknown subpages or directories on their servers that contain references to torrent download offers. Web admins are also advised to check logs for any attacks or possible backdoors.
The researchers recommend affected users change passwords, remove any subpages that do not belong to their site as well as wipe and restore the site from a backup, if necessary.
© Copyright IBTimes 2025. All rights reserved.



















