Snapchat's New Ghost Security Feature Hacked in 30 Minutes

Within 24 hours of Snapchat releasing an improved security feature, a developer has written a computer program capable of cracking it - and it only took him just 30 minutes to code the program.
Snapchat, the popular Android and iOS messaging app that allows users to share photographs that instantly self-destruct after being viewed, came under fire last month when it was revealed that 4.6 million usernames and passwords were stolen by an anonymous group of hackers known as Snapchat DB.
On Thursday Snapchat released the new Ghost captcha feature which was designed to prevent the app being hacked by bots - automated computer programs which can read traditional captchas.
The Ghost captcha is is shown to new users when they set up their accounts so that they can prove they are human.
Misgivings
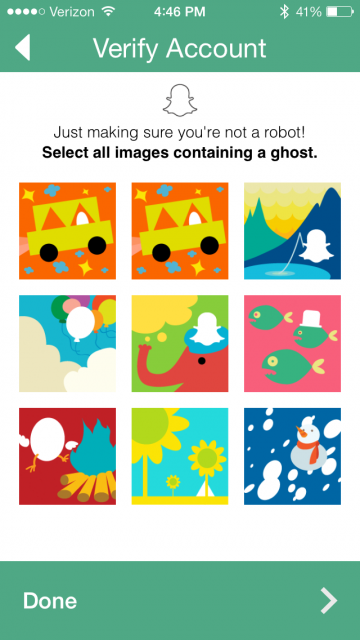
Developer Steve Hickson had misgivings about Snapchat's new security feature, which requires a user to spot where the Snapchat ghost mascot is in nine images.
"The problem with this is that the Snapchat ghost is very particular. You could even call it a template. For those of you familiar with template matching (what they are asking you to do to verify your humanity), it is one of the easier tasks in computer vision," Hickson said on his blog.
"This is an incredibly bad way to verify someone is a person because it is such an easy problem for a computer to solve."
In a statement to Mashable, a Snapchat spokesperson said: "We continue to make significant progress in our efforts to secure Snapchat. For security reasons, we cannot provide detailed information on security countermeasures."
Hacked
On 2 January, a hacker known as "Lightcontact" hacked and stole the account information from 4.6 million Snapchat users, posting all the data on Reddit and another website called SnapchatDB.info, although the hacker did censor the final two digits' of users' phone numbers and their second names.
Snapchat waited a week before it issued an apology to users for the leak, together with an update to the app that included the ability for users to opt out of linking their phone number with their username, but only after they hand over their mobile number to verify the account when setting it up.
Hickson has posted his code on his blog and says that "with very little effort", the code he wrote is able to find the ghost in the nine-image captcha feature with 100% accuracy.
"I'm just saying that if it takes someone less than an hour to train a computer to break an example of your human verification system, you are doing something wrong. There are a ton of ways to do this using computer vision, all of them quick and effective. It's a numbers game with computers and Snapchat's verification system is losing."
© Copyright IBTimes 2025. All rights reserved.






















