Heartbleed 2.0 - Hackers Selling Another OpenSSL Flaw for $1,000

Security experts have poured cold water on claims made by a group of five hackers that they have discovered another major security flaw in OpenSSL, just weeks after the Heartbleed Bug caused major worry for millions of internet users.
The claim was made on the text-sharing service Pastebin by an unidentified group of five hackers. They claim:
"We have just found an vulnerability in the patched version OpenSSL. A missing bounds check in the handling of the variable DOPENSSL_NO_HEARTBEATS. We could successfully Overflow the DOPENSSL_NO_HEARTBEATS and retrieve 64kb chunks of data again on the updated version."
The hackers said they would not make the vulnerability public as it would only allow companies to patch the flaw. They added they could exploit the flaw themselves "for a long time" before it gets patched, but they are also willing to sell it for 2.5 bitcoins ($1,085; £645) or 100 litecoins ($981).
"We are team of five people, and we have coded nonstop for 14 days to see if we could find a workaround, and we did it! We have no reason to make it public when the vendors will go for a update again," the group said.
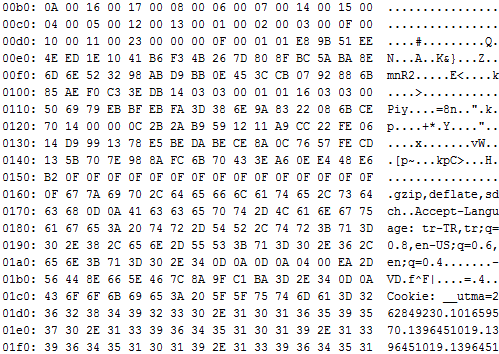
The only evidence given that the vulnerability is realise this image of what appears to be the output from a server to a request from the attackers.
However there may not be need for the widespread panic seen when the original Heartbleed Bug was revealed, with security experts casting doubt on the legitimacy of the claims made by the hackers.
Experts have pointed out that the DOPENSSL_NO_HEARTBEATS variable mentioned by the hackers doesn't actually exist.
The only identifier used by the hackers is the email address BitWasp@safe-mail.net which, according to Softpedia, was previously used by groups selling user information from collapsed bitcoin exchange MtGox.
© Copyright IBTimes 2025. All rights reserved.




















