Meet Ge Xing, the alleged Chinese state-sponsored hacker who has attacked multiple countries

A group of security researchers have outed a Chinese civil servant whom they believe was paid to work full time maintaining malware used to conduct cyberespionage and steal data from international bodies and multiple governments around the world.
Naikon is the name of multiple variants of malware that have been connected to the Chinese military. Since 2013, research by firms such as TrendMicro and Kaspersky Labs has confirmed targeted cyberattacks using this malware have been made against the governments of Singapore, Malaysia, the Philippines, Vietnam, Laos and Myanmar, as well as international bodies such as the Association of Southeast Asian Nations (ASEAN).
Over the past two years, media reports of attacks by state-sponsored hackers against Western governments have been on the rise.
The US recently implicated China in a huge cyberattack that saw hackers steal the fingerprints of over 5.6 million federal personnel, and the head of Defense Advanced Research Projects Agency (DARPA) said in August that cyberattacks against the US military are now occurring every single day.
Of course, if the country is indeed behind cyberattacks against the US or any other territory, China will never admit to it, so researchers from security firms ThreatConnect and Defense Group decided to analyse traffic from the various malware variants to work out exactly how the operations were carried out, and even who was behind them.
Proving malware originated from the People's Liberation Army
The Naikon malware worked using traditional phishing methods – emails containing malicious attachments of fake newspaper articles were sent to unsuspecting users. When opened, their computers became infected with malware, which would then search for sensitive information to steal.
If found, the information would be silently sent to a proxy command and control server, which acted as an intermediary to receive the information and then sent it on to a Chinese military server, neatly disguising the activities of the Naikon hackers, who could then remotely send back further commands to the malware.
In their report, the researchers reveal they found at least eight types of custom malware samples configured to communicate with the greensky27.vicp.net domain, so they analysed five years' worth of DNS data traffic going back and forth between the domain and the malware.
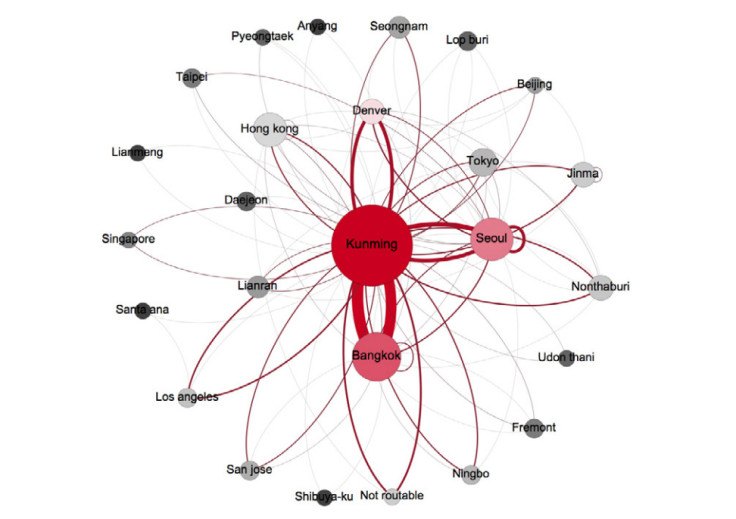
They discovered the domain had connected to almost 1,236 IP addresses in 26 cities and eight countries in the world between 2010 and 2015, and although most of the hosts were in south east Asia, there were also several in North America.
Further analysis showed the IP addresses all seemed to eventually point to Kunming in China, which told the researchers that the city was the real central home for the domain, even though the hackers had carefully routed traffic through other hosts in Denver, Hong Kong, Bangkok and Seoul too.
Meet Ge Xing, who used the same username too often

Convinced by their data that all the malware originated in Kunming, where the military intelligence Unit 78020 of the People's Liberation Army (PLA) resides, the researchers decided to search for the phrase "GreenSky27" on the internet.
They discovered the hacker was allegedly a man who used GreenSky27 as a username across several different social media accounts, posting content about himself publicly, such as the back of his car showing his Yunnan licence plate, as well as geolocated bicycle routes travelling across Kunming.
By scanning the content on his QQ Weibo account, which listed over 700 public posts and photo albums containing over 500 photographs, the researchers saw the man was a PLA member as he kept posting photos from PLA events, as well as photos of buildings in and near the Kunming headquarters compound.

He also listed that he attended the Sichuan International Studies University, which was originally founded as the Russian Training School of Southwest Military University of PLA in 1950, and has a long history in training PLA officers in military foreign relations and intelligence translation.
But the true clincher came from searching for "GreenSky27" on a multiple of local and hobby-related forums, where the researchers finally discovered the man's real name was Ge Xing. Using that information, the researchers then located two research papers about Thai politics in a national database that were written by a Ge Xing in 2008.
Beneath the title of the paper and the author's name was listed the affiliation line, which read: "Chinese People's Liberation Army Unit 78020, Yunnan, Kunming, 650223".
He only hacked during office hours
The researchers decided they also wanted to prove Ge Xing's job was to hack for the Chinese military for a living. So they looked at all the times of the day when the greensky27.vicp.net domain was inactive, and they discovered the domain was only active during regular daily working hours, from 9am to 6pm.
The activity would fall at midday, presumably when Ge Xing went for lunch, and the domain name was also inactive during major Chinese national holidays, such as Chinese New Year.
Ge Xing's Weibo social media posts also corresponded to periods of inactivity on the domain. For example, the domain was inactive for eight days after he posted about the birth of his child in November 2012, which was presumably when he went on paternity leave.
What you should take away from this

Since the release of the report, Ge Xing's social media accounts have been deleted and activity from the domain has decreased. While he very likely feels that this is an invasion of privacy, this case serves as a reminder that everyone should be careful about what sort of content you put on the internet.
Not only that, but everyone, from regular consumers to big companies, need to realise that hacking and cyberespionage is now a big game.
This case serves as a reminder that everyone should be careful about what sort of content you put on the internet
"The inherent unfairness of the security game should be plainly obvious from the scope of this investigation. Those who still picture the adversary as hoodie-wearing teens crouched over a computer in their mom's basement are doing their organisations a disservice," the researchers wrote.
"In many cases, as evidenced in this document, the adversary thinks well beyond even your 'long-term' strategic plan and is far better resourced than your entire organisation."
Of course, for the researchers, the point is that there probably is a great deal of truth in the claims that Chinese state-sponsored hackers are indeed conducting cyberattacks against other countries, including the US.
"China will undoubtedly continue their routine of blasé denials and dismissals of all allegations. Such a position becomes harder to maintain, however, when one of their own – albeit unwittingly – offers the incriminating evidence," the researcher concluded. "We hope the evidences revealed in this report serve as a catalyst for greater awareness and improved diplomacy within the South China Sea region and around the globe."
© Copyright IBTimes 2025. All rights reserved.




















