The mysteries of Petya: How a global ransomware outbreak unfolded from Ukraine
The global wave of cyberattacks has allegedly been traced to its source: Ukraine.
Security researchers are still coming to terms with the global ransomware outbreak that unfolded on 27 June 2017 – but a clearer picture is now starting to emerge, showing the digital assault which infected thousands of computers likely originated from a software firm in Ukraine.
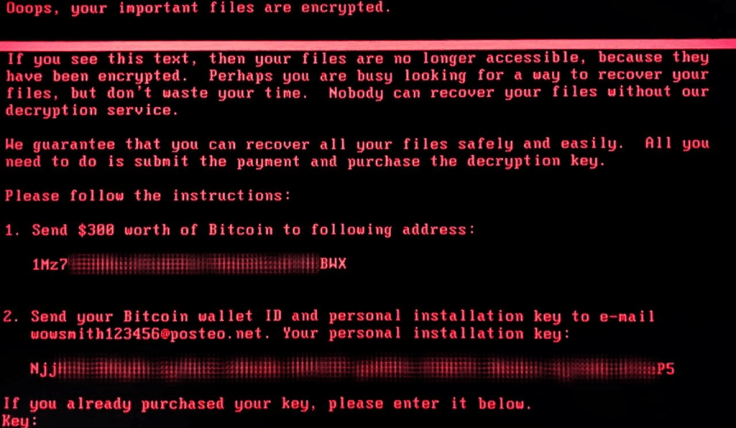
Dubbed 'Petya' – but known under myriad other names at this point – it used a sophisticated cocktail of leaked US National Security Agency (NSA) exploits and known ransomware code to lock down networks and demand $300 worth of cryptocurrency in exchange for their release.
It emerged out of nowhere, but hit hard.
Now, 24 hours later, industry experts from Kaspersky Lab, Cisco Talos, FireEye, Eset and more have largely landed at the same conclusion: a major route of infection was pushed by Ukrainian accounting firm MEDoc.
"Essentially what happened is MEDoc (big financial software) was hacked and they pushed out the malware via the update feature," tweeted MalwareTech, a researcher widely credited with stopping a previous ransomware outbreak in May this year, linked to a strain known as WannaCry.
"Current data suggests that Petya was deployed onto possibly millions of computers by hacking popular Ukrainian accounting software MEDoc then using the automatic update feature to download the malware onto all computers using the software," he elaborated in a blog.
At the same time, Petya was spreading – hitting businesses, power plants, airports and governments.
The experts all say Ukraine had the majority of affected machines, but using leaked NSA code was able to travel far and wide. Later, Microsoft all but confirmed the speculation.
"Initial infection appears to involve a software supply-chain threat involving the Ukrainian company M.E.Doc, which develops tax accounting software, MEDoc," its research team wrote in an in-depth analysis of the threat, backing up the social media post from Ukraine's cyber police.
It continued: "Microsoft now has evidence that a few active infections of the ransomware initially started from the legitimate MEDoc updater process.
"Software supply chain attacks are a recent dangerous trend with attackers which requires advanced defence."
Microsoft said it was able to spread by stealing credentials, using file-sharing to transfer the ransomware across machines on the same network and abusing unpatched Windows flaws using at least two leaked NSA tools, EternalBlue and EternalRomance.
It was not as widespread as WannaCry, however, because it was restricted to company networks. Yet it was efficient, only needing one computer with admin rights on a network to trigger the spread via two legitimate remote Windows tools, known as WMI and PSEXEC.
Analysts uncovered that when Petya first lands on a computer it searches for its own file name. If found, the ransomware is never triggered. Luckily, this allowed some experts to create a fix.
There has been mixed signals from MEDoc after the ransomware attacks started. "Attention! Our server made a virus attack. We apologise for the inconvenience!" stated one early (now deleted) update. On the same day, however, a lengthy post on Facebook denied involvement.
Global law enforcement is now probing the cybercrime wave.
Still, there remains conflicting reports from industry researchers who are still investigating the incident. Group IB, a cybersecurity firm, said the ransomware was able to spread via phishing emails, explaining its far-reach. Kaspersky claimed booby-trapped websites may be involved.
"The most significant discovery to date is that the Ukrainian website for the Bakhmut region was hacked and used to distribute the ransomware to visitors via a drive-by-download of the malicious file," Kaspersky said in an updated statement to press on 28 June.
Another firm, Bitdefender, said the spread may have been aided by global VPN connections.
In addition to known vectors, ExPetr/PetrWrap/Petya was also distributed through a waterhole attack on https://t.co/j9DvYcEgW7
— Costin Raiu (@craiu) June 28, 2017
How to fix a problem like Petya?
There are a number of methods that have emerged about how to deal with the threat. Microsoft said it recommends customers stay up-to-date will all security patches and disable SMBv1 – the system which can be exploited to spread rapidly. You can see its full technical write up here.
"It only takes one unpatched computer to get inside the network, and the malware can get administrator rights and spread to other computers," explained Eset. "For spreading, it appears to be using [the] SMB exploit (EternalBlue) used by WannaCry for getting inside the network."
"This dangerous combination may be the reason why this outbreak has spread globally and rapidly, even after the previous outbreaks have generated media headlines and hopefully most vulnerabilities have been patched." Like other firms, Eset is still analysing the attack.
"Mass infection via a rogue update is definitely something to look out for now for desktops, servers & mobile apps," warned security expert Matthieu Suiche on Twitter. "The number of companies building software with no [security] on their build environment is surely high and disastrous."
© Copyright IBTimes 2025. All rights reserved.




















