Has Renowned Blackhole Exploit Kit Creator 'Paunch' Been Arrested?
One of the people behind the Blackhole exploit kit, one of the most prevalent threats on the web - nicknamed Paunch - has reportedly been arrested in Russia.

Update: Europol Confirm Arrest of Blackhole Creator Paunch
On Monday a tweet from Maarten Boone, a security researcher at Fox-IT, a Dutch security firm claimed that a Russian hacker nicknamed Paunch, one of the creators of the Blackhole exploit kit, had been arrested in Russia.
There were no more details from Boone, but the tweet was quickly picked up by others in the security industry. Hours later however, and despite some false confirmations, there has been no official word about the arrest of Paunch or the cyber-criminal gang he controls.
With such a lack of official information to go on, Jerome Segura, senior security researcher at Malwarebytes, has been examining other indications that Boone was correct and that the renowned cyber-criminal has been arrested.
The first is that crypt.am, a Russian service used to encrypt the Blackhole exploit kit, has been offline at least since Boone first tweeted about the alleged arrest. At the time of publication the service was still offline.
Corroboration
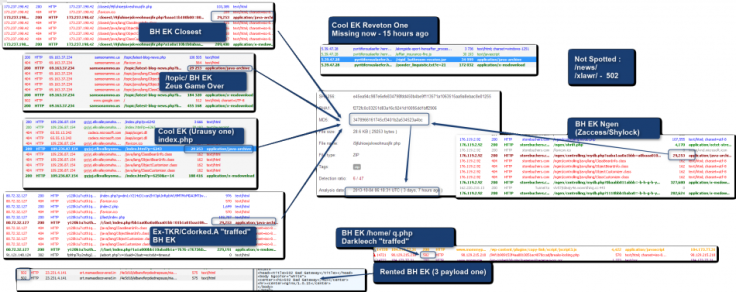
The second piece of corroborating evidence comes from French security researcher Kafeine, who has been documenting the Blackhole Exploit Kit for a long time, and in the wake of reports of Paunch's arrest, published a graphic showing how the malicious Java applet normally updates once or twice a day by Paunch simply hasn't changed in at least four days.
Malwarebytes has also "confirmed the strong presence of the same Java file in the last 24 hours from our own honeypot collection."
Major event
According to the security researcher the arrest of Paunch "would be a major event in the exploit kit business, one that could trigger a chain reaction leading to more arrests and disruption."
The Blackhole exploit kit is used to booby-trap compromised websites in order to download malware without the user even knowing it is happening. The type of malware typically downloaded include banking Trojans and ransomware.
According to AVG, Blackhole is the most prevalent web threat on the internet, with 91% of all web threats detected by the anti-virus company due to this exploit kit.
Rental
Unlike other pieces of malware, Blackhole is licenced from the owners and can be customised to suit the clients' particular needs. Cyber-criminals licencing the product can then redirect users from a malicious webpage to the Blackhole exploit kit server's landing page.
If Paunch and his cohort have been arrested it will mean that criminals who have rented Blackhole will no longer receive updates and eventually the exploit and payload are "going to go stale" according to Segura.
Some cyber-criminals host the exploit kit themselves and therefore have more control over it, meaning if they have the technical know-how they will be able to make the necessary alterations, meaning Blackhole is unlikely to disappear completely from the web any time soon.
© Copyright IBTimes 2025. All rights reserved.





















