SMS-based two factor authentication is insecure and should be banned, warns US standards body
The US National Institute for Standards and Technology wants enterprises to move towards biometrics instead.

A major US standards body is starting to dissuade businesses from using two-factor authentication as a security measure to protect consumers as the method is insecure and can be exploited by cybercriminals.
The US National Institute for Standards and Technology (Nist) publishes the Digital Authentication Guideline (DAG), a set of guidelines designed to help software developers build secure apps, as well as enabling enterprises and government agencies to access and improve their cybersecurity practices when securing their software and services.
In general, in order to unlock or access a banking service or an account that contains valuable information offline, the user in question needs to have their debit or credit card with them, or another form of official government identification, like a driver's license or passport.
Today most things are done over the internet or on the phone, where there is no way for a business or the government to physically check your documents, and if you lose the bank card or your safety deposit box key, for example, then there is no way to access your account.
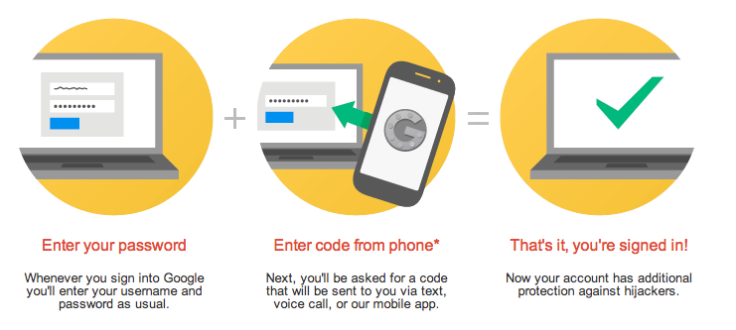
So to solve this problem, two factor authentication was developed as an alternative method that would enable users to prove that they were in fact the named individual on an account or service, because people carry mobile phones everywhere and this is considered to be a personal device that you wouldn't share with someone else. Today, two factor authentication is used as a standard security procedure on most popular online services.
The idea is that if the business or service send you a one-time valid, dynamic passcode consisting of digits via SMS text message to your smartphone, and you can enter this information together with your regular account password or answer a special security question, then you have proven who you are and should be granted access to your account.
The problem with two factor authentication
The problem with two factor authentication, however, is that the technology relies on the fact that the person with the mobile phone and your phone number will always be you, and so, in recent years cybercriminals have been coming up with innovative ways to spoof phone numbers in order to trick service providers into thinking that they are account holders.
In March, UK bank NatWest admitted that its online banking system was in sore need of an overhaul after a series of cases where customer accounts were compromised and money was stolen due to SIM swap fraud, whereby criminals hijack the SIM card in the user's phone and trick their mobile operator into activating a new SIM card owned by the criminal.
The criminal then initiates the two factor authentication process and receives the SMS text message containing the unique one-time passcode, and uses it to hijack and take control of the user's accounts and services. But this is not the only way to spoof a mobile number – the user's mobile phone could be stolen and used by the criminal to access the authentication message, and text messages can easily be intercepted by third parties.
Nist has updated the guidelines in a new draft document, and the language indicates that the standards body is not keen for anyone to use two-factor authentication.
Please consider alternative methods to authenticate users

"Due to the risk that SMS messages may be intercepted or redirected, implementers of new systems should carefully consider alternative authenticators. If the out of band verification is to be made using a SMS message on a public mobile telephone network, the verifier shall verify that the pre-registered telephone number being used is actually associated with a mobile network and not with a VoIP (or other software-based) service," Nist writes in the draft document.
"It then sends the SMS message to the pre-registered telephone number. Changing the pre-registered telephone number shall not be possible without two-factor authentication at the time of the change. Out of band using SMS is deprecated, and may no longer be allowed in future releases of this guidance."
Nist recommends that providers consider implementing other techniques as well as two factor authentication in order to tell whether the authentication attempts come from an actual user rather than a hacker, such as requiring the user to wait for an hour before they can try to login after too many failed attempts; accepting authentication requests only from familiar IP addresses (Facebook does something similar when it alerts you if you login from another country); or using the Captcha test to differentiate a human from a botnet.
The standards body also mentioned that biometrics could be used in the future, but at the moment cannot be used on its own because biometric tests can generate false positives and false negatives, and because criminals can try to spoof fingerprints and facial recognition by lifting prints from objects touched by an individual, or by taking a high resolution pictures of the person's face.
© Copyright IBTimes 2025. All rights reserved.






















