Are Isis hackers trying to destroy the internet?

A smartphone app used by Islamic State (Isis) to spread news and propaganda could be behind the massive attack on the internet's core infrastructure that took place earlier this month, according to several cybersecurity experts.
Analysis of the IS Amaq Agency app has revealed that it was potentially the source of a botnet created to perform a massive DDoS (distributed denial of service) attack on root name servers. A more powerful attack in the future could cause significant disruption to internet services and could even temporarily take down the internet.
The cyberattack, which took place between 30 November and 1 December, targeted the 13 internet root name servers that are responsible for supporting almost the entire internet. Cybersecurity experts, high-profile hackers and members of the hacktivist collective Anonymous now claim that a smartphone app was the most likely culprit for the botnet attack, which flooded the servers with five million queries per second at the peak of the attack. It is estimated that as few as 18,000 devices running the app through Wi-Fi networks would have been capable of creating such traffic.

Analysis of the Amaq Agency app found a suspicious encrypted packet containing the 13 root name server addresses. It is not possible to determine how many people use the app as it is not available through Google Play or other app stores, while those in charge of root name servers have refused to speculate on the cause of the attack.
"I feel certain that the IS news app was the source of the DDoS attack," cybersecurity expert John McAfee tells IBTimes UK. "One of my researchers has discovered encrypted packets being sent to the Amaq Agency news app.
"We found the 13 Root Server Addresses in the app memory while the app was running. The addresses did not appear inside the static app. The addresses therefore had to be decrypted at run time. Why would they encrypt the addresses inside the app unless they were trying to hide the true purpose of the app? This is the smoking gun we were looking for."
John Cassaretto, founder of web security firm BlackCert, believes that if the Amaq Agency app is behind the botnet, then the recent attack on the root name servers may have just been the first wave. The incident report from Root-servers.org did not speculate on the source of the DDoS attack and official investigations are still underway.
"What is clear is that there is much speculation, but of course there is also a lot of evaluation of data going on," Patrik Fältström, head of research and development at Netnod, tells IBTimes UK. "If and when people (including Netnod) have more data to share, we will do so."
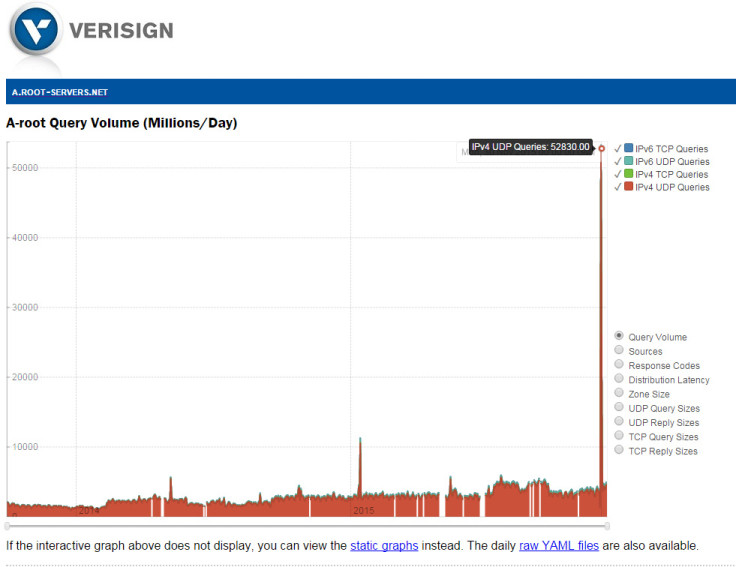
Root name server Verisign released a blogpost giving its perspective on the attacks, alongside a video that it claims is able to demonstrate that the source addresses were spoofed.
According to McAfee, this is not proof that the IP addresses were not real. "This is utter nonsense," McAfee says. "If someone is going to write a script to do a DDoS attack, why go to all of the trouble to write a set of different spoofing algorithms? More telling yet is that the bulk of the blogpost was dedicated to giving us a sense of relief and trust in Verisign. If they admitted that the IP addresses were real, there would be panic because there are no safeguards for such an event."
Threat of cyber terrorism and Western vulnerabilities
Until recently, the cyber capabilities of IS have been thought to be very limited. Despite declaring a cyberwar against the West and proclaiming a "cyber caliphate", no major attacks have previously been attributed to the group.
Digital strategy consultant Lars Hilse suggested in a report on cyber terrorism that there are "gaping vulnerabilities" in Western infrastructure that would make easy targets for IS, while recruitment of hackers would not be an issue considering the $2bn war chest at its disposal. A separate report published this week by Kronos Advisory, titled The Imminent Front, states that is is likely skilled hackers have already been recruited by IS.
"We assess with high confidence [that Daesh] has recruited individuals who possess technical skills required to conduct sophisticated cyber offensive operations," the report states. "It is assessed with low confidence that an absence of cyber attacks targeting critical infrastructure is an indicator this terrorist group is not intent upon expanding its cyber terrorism capabilities."
"This could mean the failure of dams and flood controls, power and water distribution, natural gas distribution and control failure, and more."
Should an attack on the root name servers be large enough that it overwhelms them, there are thousands of secondary servers around the world that could function as temporary replacements, but the majority are cached systems that only hold the data for a temporary period of time. There are 370 more permanent servers, but taking these servers down through a similar DDoS attack would be trivial in comparison.
What would happen if Isis destroyed the internet?
If successful, the global impact of such an attack would be catastrophic. Information security expert Eddie Mize has previously hypothesised about what would happen in the event of a global internet outage, suggesting that due to the West's reliance on the internet for critical infrastructure, everything from air travel to emergency services would be affected. Mize also believes that a catastrophic DDoS attack on the DNS infrastructure is possible using enough mobile devices.
"Imagine if the internet went down for several days, I believe we would see significant power grid failure and potentially loss of emergency services," Mize tells IBTimes UK. "This could mean the failure of dams and flood controls, power and water distribution, natural gas distribution and control failure, and more.
"Perhaps the most alarming aspect would be to the financial sector. I believe that loss of the internet for even a two week period could cause enough disruption to financial institutions that consumers would lose confidence and this could be catastrophic to the markets. All of this could set up a chain reaction that could send the public in to a panicked tailspin."
© Copyright IBTimes 2025. All rights reserved.





















