'Armada Collective' hackers to launch bitcoin-extorting DDoS attacks on unwitting victims
Hackers claiming to be Armada Collective have sent email extortion demands promising 300Gbps DDoS attacks.

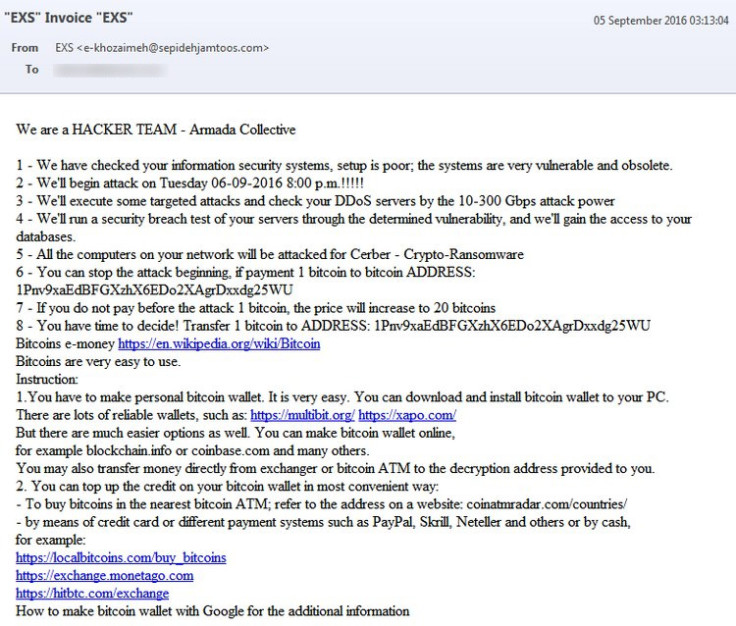
A group of cybercriminals claiming to be the Armada Collective have sent a new wave of extortion demands by email to the owners of independent and small business websites around the world, demanding bitcoin ransoms and threatening to launch a huge new Distributed Denial of Service (DDoS) attack on Tuesday 6 September.
Etienne Delport, the owner of Alpha Bookkeeping Services in Port Elizabeth, South Africa, and Michael O'Connor, a professional musician based in Cornwall, UK, both showed IBTimes UK similar emails from the purported hacking group.
The cybercriminals claim they won't attack the victim's website if the victim pays the hackers 1 bitcoin ($606, £456), but if the victim ignores the demand, it will cost 20 bitcoins to make the DDoS attacks stop.
The email warns, "We have checked your information security systems, setup is poor; the systems are very vulnerable and obsolete. We'll begin attack on Tuesday 06-09-2016 8.00p.m.!!!!!". A specific time zone is not listed, and the hackers claim that they will attack all the computers on the user's network with the Cerber ransomware, using "10-300 Gbps attack power".
And in case you don't know how to use bitcoin, so you wouldn't know how to pay, the cybercriminals helpfully include instructions on how to download a personal bitcoin wallet like Multibit or Xapo, or where to go to set a bitcoin wallet up online.
Rather than being concerned, Delport has openly dared the hackers to DDoS her website on Twitter, as she doesn't feel that she has anything to lose from it, while O'Connor chose to report the email to the City of London Police's Action Fraud UK website, which is operated by the National Fraud Intelligence Bureau (NFIB).
"I don't think they can harm me. I freelance at clients' premises. I have no database or any sensitive information locally," said Delport. "My website is a basic WordPress site on a shared server. Attacking that server will affect many and be the host's problem, not mine. Ransoming the server will affect me exactly zero. If they do it to the laptop I will just wipe the hard drive and restore."
But is it the real Armada Collective?
There is an actual hacking group called Armada Collective in existence that extorted money from numerous Swiss firms, several Thai banks and even the encrypted webmail provider ProtonMail using continuous, sustained DDoS attacks in October and November 2015.
Not much is known about this group, except that they don't like being mentioned in the media, as UK cybersecurity expert Graham Cluley discovered when he wrote an article about them, and then saw his website hit by a DDoS attack for several days.
However, it is impossible to tell if the cybercriminals behind this new email demand are the real group, or simply cybercriminals taking advantage of the real group's infamy. In April, security firm CloudFlare revealed that a hacking group pretending to be the Armada Collective had raked in $100,000 in just two months simply by issuing fake threats that they never followed up on.
CloudFlare analysed the web traffic of over 100 existing and prospective customers and found that the hackers never actually issued any real attacks, and the emails reused the same Bitcoin addresses again. However, the reputation of the real Armada Collective seemed to ensure that victims were willing to pay up.
Whatever you do, don't pay the ransom

City of London Police told IBTimes UK that its standard advice is that businesses should definitely not pay the demand but instead report it to Action Fraud hotline or use the online reporting form. Victims should also maintain a timeline of the attack, recording all times, content, method and types of contact from the hackers, as well as retaining the original emails, including their headers.
"You should look to purchase additional services to protect against DDoS, which will be much cheaper than 1 bitcoin. We say to people, if you get involved in ransomware, don't ever pay the
cybercriminals, you're just funding them," Mark James, a security specialist at internet security firm ESET told IBTimes UK.
"There's a very high possibility that the email demand is fake – it's building on an established name. It's a mass mailing campaign, knowing that just a few hundred or thousand might actually send off a bitcoin. That's a relatively tidy haul for a spam campaign."
© Copyright IBTimes 2025. All rights reserved.






















